There are 11 home screens and each can accommodate 20 applications. Each app icon is the same size as on the iPhone, so you'll notice there's lots of space around each. This may not be the most attractive way of doing it, but we think adding more icons would make it much harder to find the app you're looking for, so can see the reasoning behind the decision.

Preloaded apps are pretty basic, although that's why the app store is such a success.
The first app of note is the email app that works much better in both landscape and portrait mode. If you have an iPhone, you'll find the email set up is identical, and that means seamlessly easy to set up. Forget having to add every single little detail as you do on Android and BlackBerry devices. You simply need to add your email address, domain, user name, password, give the account a name and, hey presto, your emails will start to filter through, even when using Exchange.
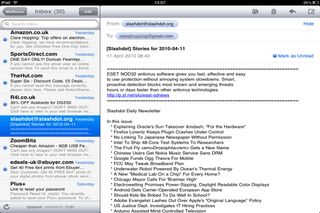
Open the Mail up and you'll find it's probably the most computer-like application possible to use on the iPad (save for Pages and Numbers that we'll cover later).
In landscape mode, your inbox is displayed on the left side of the app with the selected email showing on the right.
Some attachments (such as photos) appear in the body of the email, but you can click on them to make them full screen or open them in a third party app you may have downloaded. We were able to open a word document in Pages after we had bought the document editing app.
In portrait mode, the inbox will appear as a pop up over the top of the main window.

Clare is the founder of Blue Cactus Digital, a digital marketing company that helps ethical and sustainability-focused businesses grow their customer base.
Prior to becoming a marketer, Clare was a journalist, working at a range of mobile device-focused outlets including Know Your Mobile before moving into freelance life.
As a freelance writer, she drew on her expertise in mobility to write features and guides for ITPro, as well as regularly writing news stories on a wide range of topics.

