Virginia shooting - don't open that link!
Scammers and cyber criminals love to capitalise on tragedy, and we can't help but click

Shootings in America are, sadly, not unusual, but when two journalists were shot live on air on Wednesday last week, social media went into overdrive.
What made this particular attack unique is the fact it was filmed and broadcast by the victims as it happened and, it later transpired, the shooter himself had recorded the murder and posted it online before taking his own life.
Very quickly, my Twitter feed was full tweets from news organisations such as the Huffington Post linking to stories containing the "graphic footage" or, in the case of Russia Today, having a short Vine of two people dying auto-play when you scrolled down.
Soon though, news outlets reacted to the revulsion people expressed at their decision to rebroadcast the footage and removed it from their stories. Facebook and YouTube were also diligent in their efforts to remove the footage taken by shooter Vester Lee Flanagan as it was posted and reposted.
But, for some, the desire to see the footage first hand is too much, and cyber criminals know this as much as - or perhaps better than - anyone else.
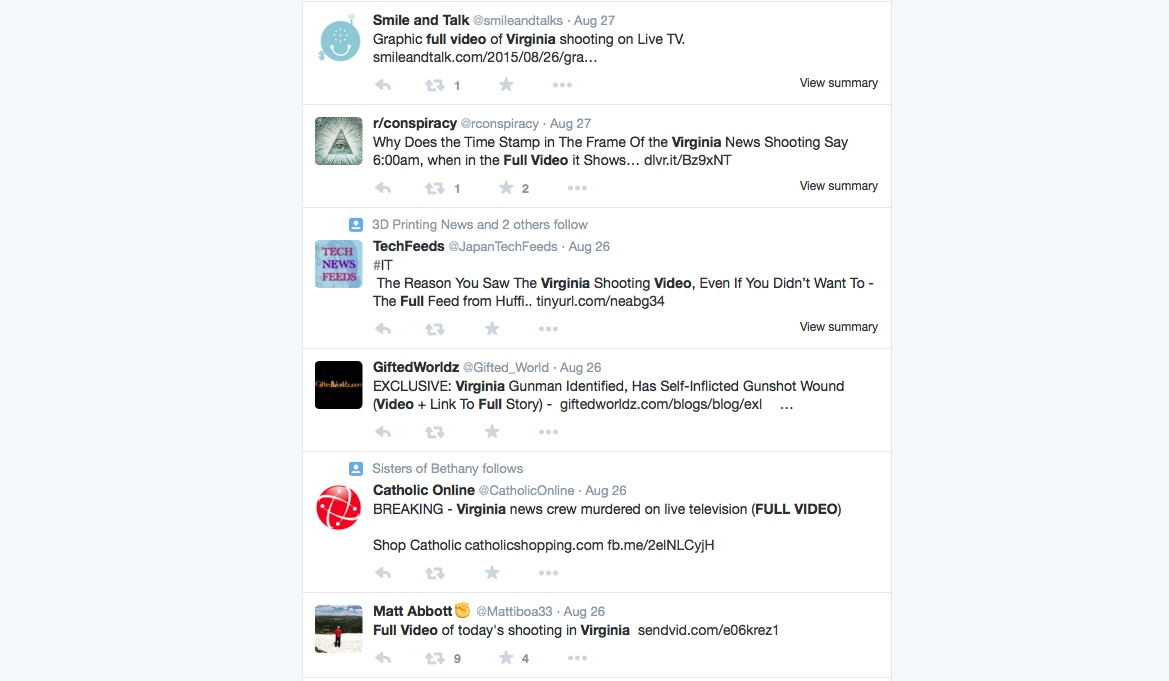
By the evening, the Virginia trend on Twitter was full of rather suspicious-looking links to the "full uncensored video".
Social engineering attacks that take advantage of our curiosity are among the most successful at attracting victims and are also relatively easy to create, which is why they remain so popular with cyber criminals as a vector of attack.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
It's not just social media, either - emails are still circulated in the wake of tragedies, be it a link to an alleged miracle survival video from a natural disaster or something more grisly, as in this case.
"Malicious actors are always going to use something that's in the media to try and lure in victims," Tim Grieveson, HP's chief cyber and security strategist, told IT Pro. "We're human, we are voyeurs, and they know that."
"To protect against successful attacks, you need to have good technology in place, but it's also about educating people to be careful, both in the business and at home. There are still a lot of people who get caught out by phishing emails - they still click that link - but education now has to be mulit-platform and include social media as well," Grieveson said.
Even though there's a strong moral argument against it, curiousity will always get the better of some people - they want to feel hope in the face of disaster, they want to feel righteous anger when ISIS execute a prisoner, they want to see something ususual and shocking.
But, just maybe the threat of malware, rather than a salacious video, will make us think twice in future.

Jane McCallion is Managing Editor of ITPro and ChannelPro, specializing in data centers, enterprise IT infrastructure, and cybersecurity. Before becoming Managing Editor, she held the role of Deputy Editor and, prior to that, Features Editor, managing a pool of freelance and internal writers, while continuing to specialize in enterprise IT infrastructure, and business strategy.
Prior to joining ITPro, Jane was a freelance business journalist writing as both Jane McCallion and Jane Bordenave for titles such as European CEO, World Finance, and Business Excellence Magazine.
-
 Latest Meta GDPR fine brings 12-month total to more than €1 billion
Latest Meta GDPR fine brings 12-month total to more than €1 billionNews Meta was issued with two hefty GDPR fines for “forcing” users to consent to data processing
-
 "Unacceptable" data scraping lands Meta a £228m data protection fine
"Unacceptable" data scraping lands Meta a £228m data protection fineNews The much-awaited decision follows the scraping of half a billion users' data and received unanimous approval from EU regulators
-
 Meta notifies around 1 million Facebook users of potential compromise through malicious apps
Meta notifies around 1 million Facebook users of potential compromise through malicious appsNews The vast majority of apps targeting iOS users appeared to be genuine apps for managing business functions such as advertising and analytics
-
 Twitter API keys found leaked in over 3,200 apps, raising concerns for linked accounts
Twitter API keys found leaked in over 3,200 apps, raising concerns for linked accountsNews Business and verified Twitter accounts linked to affected apps are at risk of takeover, use in malicious campaigns
-
 Facebook business accounts hijacked by infostealer malware campaign
Facebook business accounts hijacked by infostealer malware campaignNews Threat actors are using LinkedIn phishing to seize business, ad accounts for financial gain
-
 Meta begins encrypting Facebook URLs, nullifying tracking countermeasures
Meta begins encrypting Facebook URLs, nullifying tracking countermeasuresNews The move has made URL stripping impossible but will improve analytics
-
 Meta hit with €17 million fine over multiple GDPR breaches
Meta hit with €17 million fine over multiple GDPR breachesNews The social media giant set aside over €1 billion in November to help it cope with potential fines arising from data protection investigations
-
 Meta says Apple's iOS privacy changes will cost it $10 billion in 2022
Meta says Apple's iOS privacy changes will cost it $10 billion in 2022News The company's CFO suggests Google "faces a different set of restrictions" because it pays Apple to remain the default iOS search engine

