How to turn a Raspberry Pi into a VPN server
A guide to building an encrypted connection to your home network from anywhere
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
With a VPN server plugged into your router, you can create a secure, encrypted connection from anywhere in the world to your home network.
This has several advantages, such as being able to access files on your NAS without any fiddly configuration or, as the connection is encrypted, the option to use your laptop on a public Wi-Fi hotspot without worrying about someone intercepting the data you transmit.
Best of all, as you control everything, you can rest assured that your data is completely safe and that you're not relying on any other service.
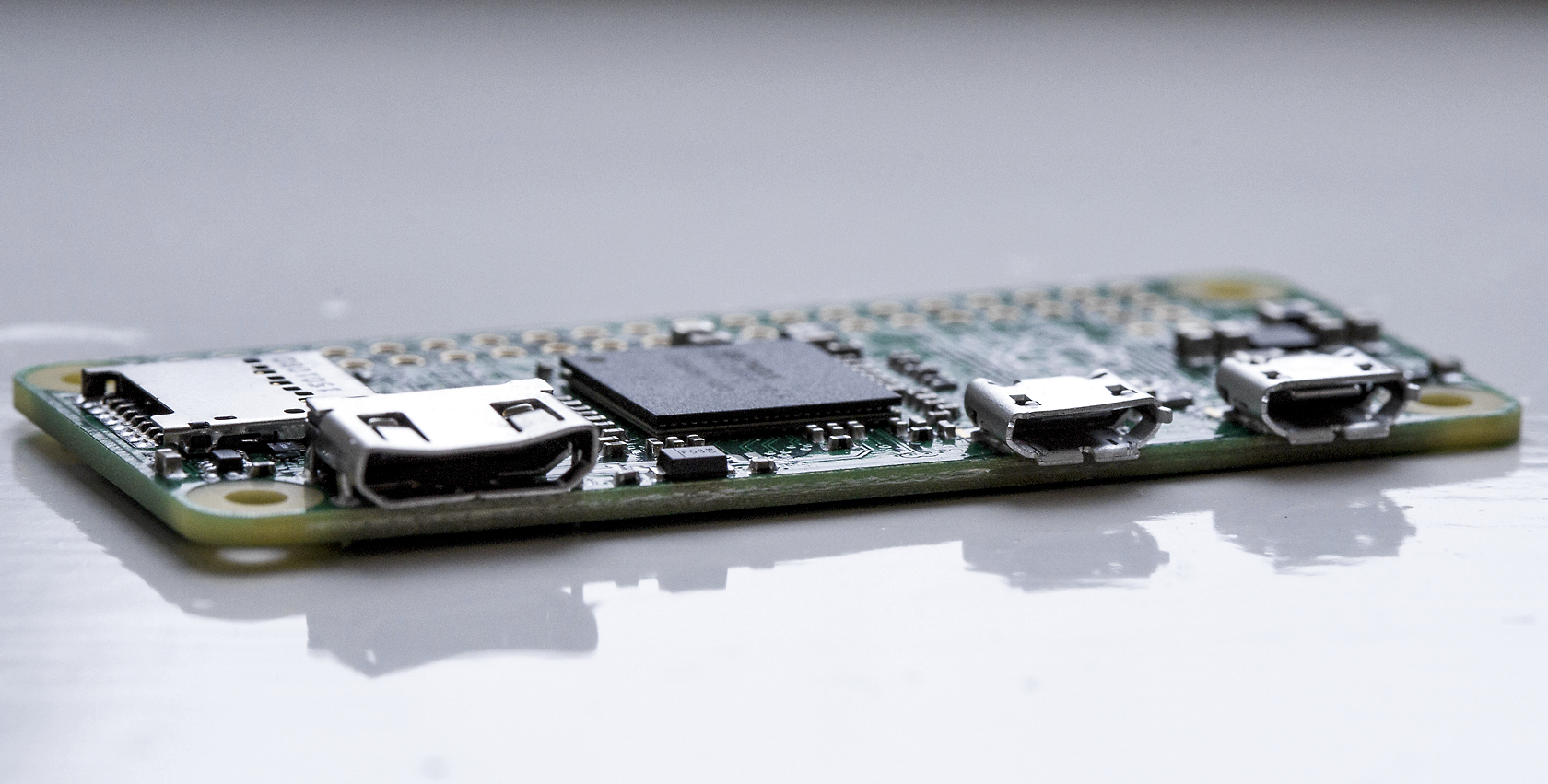
You don't need any special hardware to make the VPN, either: a simple Raspberry Pi will do. This guide will show you how to set up your Raspberry Pi with the OpenVPN server, using the clever PiVPN script.
Installation
The PiVPN OpenVPN installer we're going to use doesn't currently support the latest Raspbian Stretch distro, so you'll need to use Raspbian Jessie, the previous version. Jessie was the current version of Raspbian until July 2017, and will be supported for at least another six months, by which point the PiVPN script should hopefully have been updated to support Raspbian Stretch.
The free No-IP service will make sure you can always connect to your VPN, even if your IP address changes
As we'll be using the Raspberry Pi in command-line mode, it makes sense to use the Lite version of Raspbian, which doesn't come with a graphical user interface but is a fifth of the size of Raspbian proper.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Download the 2017-07-05-raspbian-jessie-lite.zip file using this link, and extract the .img file inside. Next, download and install Win32 Disk Imager. Finally, plug your microSD card into a card reader, and make sure the card doesn't have anything on it you need.
Use Win32 Disk Imager to write the Raspbian Jessie Lite image to a microSD card
Run Win32 Disk Imager. If you're logged in with a standard (rather than administrator) Windows account, you'll need to enter your administrator password. Click the blue folder icon on the right of the white box at the top, then browse to the Raspbian Jessie Lite .img file you extracted and double-click it.
Bear in mind that the file browser may default to the administrator account's Download folder instead of the current user's, so you'll need to browse to the correct location manually.
Double-check your microSD card is the one listed under Device and click Write. When the process is finished, eject the microSD card, put it in the Raspberry Pi and boot up. Your Raspberry Pi will just need a keyboard and monitor connected, and won't need to be online for now. Log in with the normal login: username pi, and password raspberry.
As the Raspberry Pi is just going to be a server, it makes sense for it to be hidden in a corner next to your router. You don't want to have to make room for a monitor, keyboard and mouse, so it's best to set up the Raspberry Pi to be controlled remotely, in so-called 'crustless' mode. To do this, you need to enable Secure Shell (SSH). Type sudo raspi-config.
The first job is to change the Raspberry Pi's password, so that only you will be able to log in over SSH. Select option 1 and enter your password twice to change it. Now go to option 5, Interfacing options. Select P2 SSH, then answer Yes to the question, 'Would you like the SSH server to be enabled?'. The Raspberry Pi will confirm SSH is on. Go down to Finish.
Shut down your Raspberry Pi by typing sudo shutdown now, unplug your monitor and keyboard, and plug your Raspberry Pi into your router with an Ethernet cable. You don't need the monitor and keyboard any more, as you'll be controlling your Raspberry Pi remotely.
Finding Pi
Turn on your Raspberry Pi again, and give it 30 seconds or so to boot up. It's now time to find your Raspberry Pi on the network. The easiest way to do this is to use the Fing Android app, which will list every device connected to your network and show the Raspberry Pi as Raspberry, along with its IP address. Under Windows, you can use an IP scanner such as Angry IP Scanner (requires Java). Angry IP Scanner will list your Raspberry Pi as raspberrypi.local in the Hostname column.
Angry IP Scanner will show you where your Pi is on your network
To connect to your Raspberry Pi you need the PuTTY SSH client Download and install it. Put your Raspberry Pi's IP address in the Host Name box, make sure the SSH radio button is selected, then click Open. You will receive a security message, so double-check it's the Raspberry Pi's IP address in the top-left of the PuTTY window and click Yes to trust the device.
Use the free PuTTY tool to connect to your Raspberry Pi remotely
You can now log in with your Raspberry Pi's username and password, and you'll have a command line just as if your Raspberry Pi was sitting in front of you. The first thing to do is to download and install any Linux updates, so use the command sudo apt-get update, followed by sudo apt-get upgrade.
It's now time to start installing OpenVPN (via the PiVPN installer). Type curl -L https://install.pivpn.io | bash to start the installer. You navigate the installer using your keyboard's arrow keys, and use tab and shift-tab to switch to the Yes/No, OK/Cancel options at the bottom of the various pages and back again. You'll also need the space bar to select some options.
Static IP
The first step is to set a static IP address; this is needed so your router always knows where your Raspberry Pi is on the network, so it can send it incoming VPN traffic. You can keep the IP address your Raspberry Pi currently has, but it may be worth setting one high in the IP range, so your router is unlikely to assign the same IP address automatically to a different device joining your network.
To do this, select No when asked if you want to use your current network settings as a static address, then change the last number of the address to, for example, 100, to give you an address such as 192.168.1.100. You can check this address isn't yet taken on your network using Fing or Angry IP Scanner.
The IPv4 default gateway should already be set to your router's IP address, so you can leave this as it is. Check the settings are correct and select Yes to continue.
Follow the steps to select which user's directory will store OpenVPN's configuration; you'll only have the default 'pi' installed, so select that. The next screen advises you to enable 'unattended-upgrades' so that your Raspberry Pi will automatically update itself with security patches; vital for a machine that is always connected to the internet and has a network port open all the time. Select Yes to enable this feature.
You can now select whether to use the TCP or UDP protocols. UDP is generally preferred as it's far quicker, but TCP has advantages in certain situations. Select UDP and press OK. Leave the port as the default (1194) and press OK. Write the port number down somewhere and confirm the port is correct in the next screen.
Paranoia level
You'll now be given three levels of encryption. The PiVPN installer recommends 2,048-bit encryption as a good compromise between security and how long it takes to generate the key, but you might want to select 4,096 for the utmost in security. If you select a 4,096-bit key you are given the option of downloading key components from a public key generation service, to cut down on generation time.
2,048-bit encryption will be enough for most people, but 4,096-bit is available for the tinfoil-behatted
However, if you're truly serious about security (or 'paranoid', as the PiVPN installer puts it), you can generate your own keys from scratch. This took less than an hour on our Raspberry Pi 3, so isn't really a big deal.
Generating encryption keys on a Raspberry Pi can take a while
A word of warning, though. The PiVPN installer doesn't support going back a stage to change a setting you've already made: if you get an IP address wrong, you'll need to quit the installer and start again, including spending an hour on key generation.
Connecting to your Pi
Now you have the keys to encrypt your VPN connection, it's time to work out how users are going to connect to your Raspberry Pi. There are two ways to do this: using your external IP address, or using a dynamic DNS service.
The external IP address is the easy way, as this requires less tinkering with your router. The disadvantage of this is that, on most residential broadband packages, the IP address changes periodically, which could leave you unable to connect to your VPN if the IP changes when you're out of the house.
To avoid this, you need to use a dynamic DNS service. This will give you an address such as pivpn.dynamicdns.com, which will translate to your router's current external IP address. What's more, when you've entered the details into your router's settings, the router will update the DNS service automatically when its external IP address changes, so the address you've chosen will always translate to your home connection's external address.
First, find out which dynamic DNS services, if any, your router supports. You'll most likely need to hunt around in your router's settings menu. You'll usually need to sign up on the dynamic DNS service's web page, but some routers, such as our Netgear D7800, let you sign up straight from the interface.
If your router doesn't support dynamic DNS, you can get around it by signing up for a No-IP account and using the Windows application. This will send your external IP address to No-IP automatically, but you'll have to leave your PC on (though not necessarily logged in) for it to work.
Once you've signed up, the No-IP dashboard will give you the option of choosing a hostname and a selection of different domains. It will fill in your IP address automatically. If the hostname you want is already taken, just keep trying hostname/domain combinations until you find a free one. You'll now see your hostname listed in the Hostnames section of the No-IP dashboard, with No Dynamic Update Detected underneath. Click this and the wizard will walk you through setting up DNS updating on your router.
Back in the PiVPN installer, choose Public IP (external IP address) or, if you're using dynamic DNS, DNS Entry. If you choose DNS Entry you'll need to put in your dynamic DNS hostname. Double-check it's correct before confirming.
You'll now be asked to choose the DNS Provider for those connecting to your VPN. This is because they'll need a DNS service to browse the web, via your Raspberry Pi's VPN server. The DNS servers will be able to see which websites those connecting to the VPN have visited, so if you're very concerned about privacy, you might want to build and use your own DNS server. That is beyond the scope of this article, though: for most people Google's DNS will be fine.
The final step will tell you to 'run pivpn add to create the ovpn profiles', but will prompt you to reboot your Raspberry Pi first. Press OK to reboot. Now is a good time to forward the necessary ports on your router. Whether you decide to use an external IP address to connect to your Raspberry Pi VPN or use dynamic DNS, you'll need to go into your router's settings and forward a port to your Raspberry Pi, so your router knows where to send incoming VPN connections.
No-IP has port-forwarding guides, and there is a comprehensive router list at portforward.com. Remember that we're using the default OpenVPN UDP port 1194, so forward that to your Raspberry Pi's IP address (making sure you select UDP not TCP).
Access granted
Log back into your Raspberry Pi with PuTTY. Type sudo-apt get update then sudo apt-get upgrade to make sure your Raspberry Pi is up to date with all the latest security patches.
The next step is to add OpenVPN profiles the users, or clients, who will be connecting to your VPN. Each client will have a username and password, which they will need to use in conjunction with a special file you generate using PiVPN, in order to connect.
Type pivpn add, and then enter the username and password for the first client you want to have access. You'll see that a .ovpn file will be generated and copied to /home/pi/ovpns. Add any other profiles you need. If you need to remove a profile, type pivpn revoke, followed by the profile name.
To copy the .ovpn files off the Raspberry Pi, it's easiest to use SFTP. You'll need an FTP client our favourite is WinSCP. Download and install WinSCP, then in the screen that appears when you run it, make sure SFTP is selected under File protocol. Enter your Raspberry Pi's IP address under Host name, make sure the Port number is 22, then enter your username and password and click Login. Click Yes to add the Raspberry Pi's host key to the cache, to avoid seeing the warning again.
By default you'll be in /home/pi, so browse to the ovpns folder and copy the .ovpn files to your PC. The combination of the .ovpn file and its matching username and password are what will let you connect to your VPN, but first you'll need some client software.
Download the OpenVPN Installer. Install it, then copy your .ovpn files to C:\Program Files\OpenVPN\config. If you're going to need to send these files to other people, it's a good idea to encrypt the files with 7-Zip beforehand, in case they are intercepted in transit. Many email services won't let you send an encrypted file as an attachment, so you'll need to host it in a file-sharing service such as Dropbox, then send a link to the Dropbox folder containing the encrypted file.
It's also a good idea to send the username and password separately from the 7-Zip-encrypted .ovpn file, preferably using an encrypted platform such as WhatsApp.
Load the OpenVPN Gui. This sits in your System Tray, and right-clicking it will give you the list of OpenVPN profiles you have installed. Just click Connect to enjoy your secure connection to your Raspberry Pi.
If you want to check the VPN is working from outside your home network, the easiest way is to connect through a smartphone running in wireless hotspot mode. We found the VPN connection let us browse the contents of our network's NAS, as well as connect to a game server.
Image: Shutterstock