Charity Commission extends outsourcing contract
Deal signed to 2012 to provide IT services designed to help reduce UK charities’ administrative burden.


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
The Charity Commission has revealed it has signed an extension to an outsourcing contract supporting applications and web hosting.
The regulator for charities in England and Wales has signed the deail under its existing application support and web hosting framework agreement with IT services provider, Parity.
The order, which runs from April 2008 until 2013, covers a major application transformation project to replace the Register of Charities application suite develop existing web-based communications to reduce the paper-intensive administrative workloads of the charities.
As part of the existing deal, the Commission has developed web-based solutions to give charities access to perform transactions online, re-developing its website to allow charities to update and submit information and accounts securely via the web.
The Commission has reduced the cost of transactions. A paper form costs 4 to process, but an online transaction costs 40p.
Nick Allaway, Charity Commission executive director, said: "Over three quarters of the main registered charities are now using our online services." He added that the Parity system also makes it much easier for charities to submit returns, to update changes in their organisation and reducing the duplication in administrative effort between the agency and the various organisations.
"It makes a huge difference to the Commission's administrative burden, saving time and money," he said. "Over time, we anticipate the take up rates to rise even further and we aim to expand the range of our online services."
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
A 25-year veteran enterprise technology expert, Miya Knights applies her deep understanding of technology gained through her journalism career to both her role as a consultant and as director at Retail Technology Magazine, which she helped shape over the past 17 years. Miya was educated at Oxford University, earning a master’s degree in English.
Her role as a journalist has seen her write for many of the leading technology publishers in the UK such as ITPro, TechWeekEurope, CIO UK, Computer Weekly, and also a number of national newspapers including The Times, Independent, and Financial Times.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
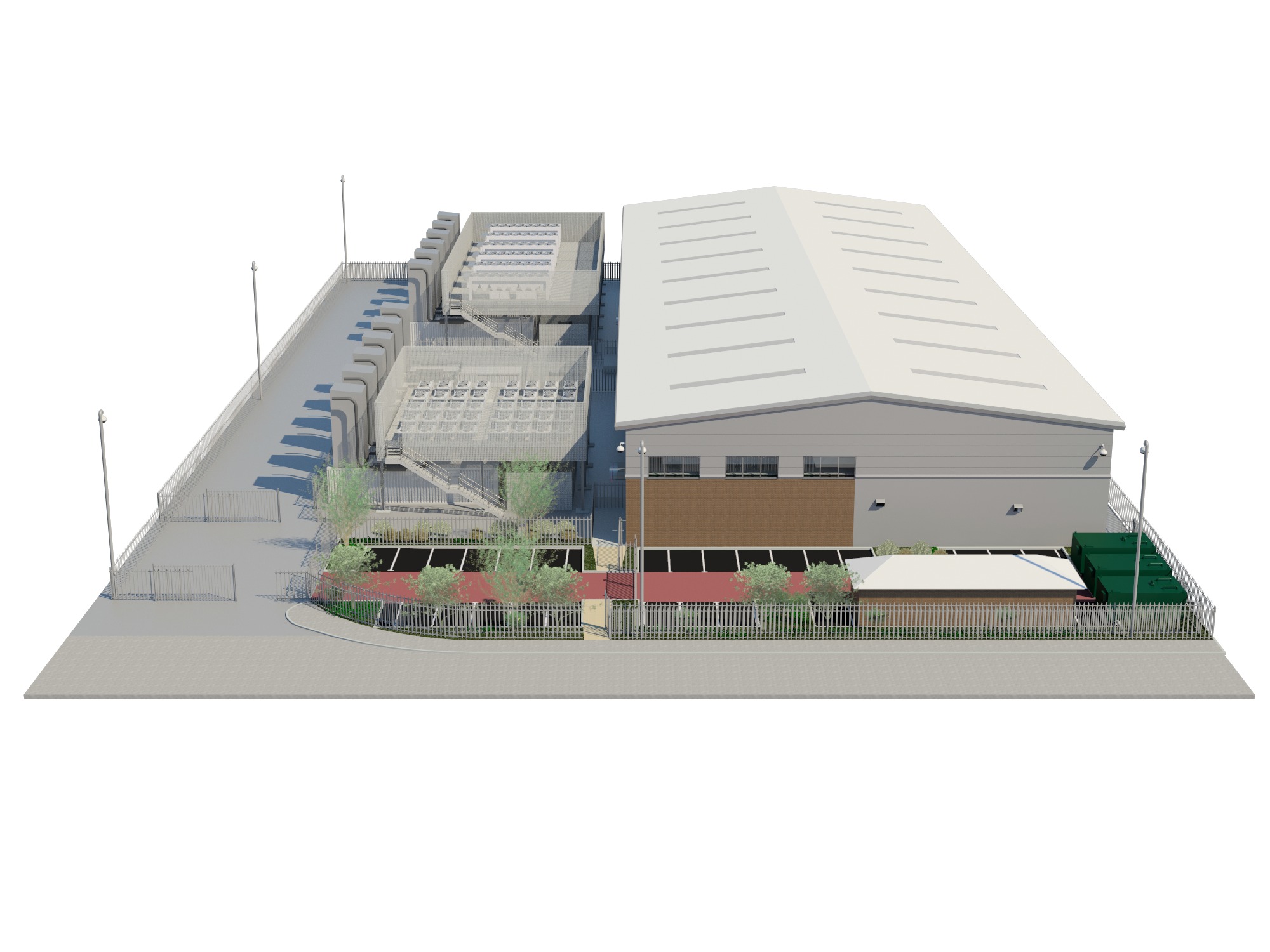 South London gains datacentre boost
South London gains datacentre boostNews New facility in Croydon will offer 8,400 sq m of space 10 miles from the City.
-
 Rightmove outsources data centre resilience
Rightmove outsources data centre resilienceNews The UK’s biggest property website has move to an outsourced “N+1” redundancy data centre model to safeguard the availability and uptime of its business.
