Guy Matthews
-
 Macabre malware makes Halloween scary
Macabre malware makes Halloween scaryNews A gang of malware propagators is using Halloween to lure PC users into responding to malicious spams, warns a security firm.
By Guy Matthews Published
News -
 Porn images 'encouraging response to spam'
Porn images 'encouraging response to spam'News An image of a stripping woman is being used to get unwary PC users to answer spam messages.
By Guy Matthews Published
News -
 Poor file management courts disaster, says report
Poor file management courts disaster, says reportNews New research says that many organisations are facing serious consequences from poorly filed information being passed around and used unwittingly.
By Guy Matthews Published
News -
 Tape vs Disc - the new battle
Tape vs Disc - the new battleIn-depth The debate about whether tape storage can compete with a disk-only back-up solution is as hot as ever. We talk to two senior pros to find where they stand on the debate as they battle with information overload in two very different sectors.
By Guy Matthews Published
In-depth -
 The benefits of SAN
The benefits of SANIn-depth The first commercially available storage area network (SAN) hit the market nearly 10 years ago. But the cost of adopting a networked storage solution restricted take up to a handful of major organisations, leaving most to muddle on with a direct attached storage model, but that's all changed now.
By Guy Matthews Published
In-depth -
 Dealing with disaster recovery
Dealing with disaster recoveryIn-depth IT PRO talks to IT managers to get their views on the growing importance of disaster recovery provisions, and to find how their own recovery strategy has evolved.
By Guy Matthews Published
In-depth -
 Academic claims contactless payments pose data security risk
Academic claims contactless payments pose data security riskNews With the number of trials of contactless payment cards groing, a leading academic security researcher has raised concerns over the level of data security in place to safeguard sensitive information during the transaction.
By Guy Matthews Published
News -
 Anti-piracy tactics backfiring
Anti-piracy tactics backfiringNews Businesses claim that heavy-handed tactics to expose unlicensed use of software, including offering rewards and incentives to inform on offenders, will do nothing to change behaviour.
By Guy Matthews Published
News -
 Work life balance being hurt by online surfing
Work life balance being hurt by online surfingNews Research shows that participation in leisure pursuits is being hit by the increasing use of the internet for information gathering and entertainment.
By Guy Matthews Published
News -
 The Wireless Event: Businesses will still need in-building
The Wireless Event: Businesses will still need in-buildingNews Large companies will find external WiMax systems alone too expense so vendors must also offer them dedicated in-building systems to compensate, says Red-M.
By Guy Matthews Published
News -
 IP telephony services accused of freeloading
IP telephony services accused of freeloadingNews Services such as Skype benefit from multi-million pound investments in infrastructure made by mobile operators yet make no contribution, industry figures argue.
By Guy Matthews Published
News -
 Managing Bluetooth at work: Part 2
Managing Bluetooth at work: Part 2In-depth In the second part of this feature series, we look at how you can harness Bluetooth to work for your business and identify some of the sectors where it appears to be making inroads in the enterprise.
By Guy Matthews Published
In-depth -
 Users must guard against shoulder surfing
Users must guard against shoulder surfingNews People are no longer looking over your shoulder just to be nosey, they could also be doing so to get a glimpse at your corporate data warns 3M.
By Guy Matthews Published
News -
 Surge in password-protected malware
Surge in password-protected malwareNews Experts warn of viruses travelling in password-protected zip files.
By Guy Matthews Published
News -
 Infosecurity Europe 2007: Security no longer wedded to IT
Infosecurity Europe 2007: Security no longer wedded to ITNews Security is increasingly likely to end its marriage with IT to go professional, according to research published this week.
By Guy Matthews Published
News -
 Businesses still failing to encrypt sensitive data
Businesses still failing to encrypt sensitive dataNews Sixty per cent of large businesses do not adequately secure data leaving their organisation.
By Guy Matthews Published
News -
 Mobile operators unite to simplify roaming
Mobile operators unite to simplify roamingNews Collaboration between mobile phone network operator groups in Europe and Asia will help simplify cross-network roaming services and pricing.
By Guy Matthews Published
News -
 Sat nav systems at risk from hackers
Sat nav systems at risk from hackersNews In-car route-planning equipment could be the next target for hackers after researchers expose wireless data vulnerability.
By Guy Matthews Published
News -
 Wireless at the Coalface: Part 2
Wireless at the Coalface: Part 2In-depth IT PRO talks to IT managers in the public sector about their views on current wireless technology, and their hopes for its future development.
By Guy Matthews Published
In-depth -
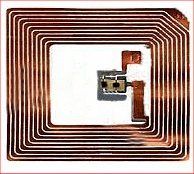 RFID open to criminal abuse
RFID open to criminal abuseNews From triggering bombs to faking passports, report exposes the flaws in this emerging technology.
By Guy Matthews Published
News -
 Managing Bluetooth at work: Part 1
Managing Bluetooth at work: Part 1In-depth The proliferation of phones, PDAs, computers and other devices that support and use Bluetooth wireless networking technology has created another headache for IT managers trying to manage wireless data services in the enterprise.
By Guy Matthews Published
In-depth -
 Wireless at the Coalface: Part 1
Wireless at the Coalface: Part 1In-depth IT PRO talks to IT managers in a range of organisations about their views on current wireless technology, and their hopes for its future development.
By Guy Matthews Published
In-depth -
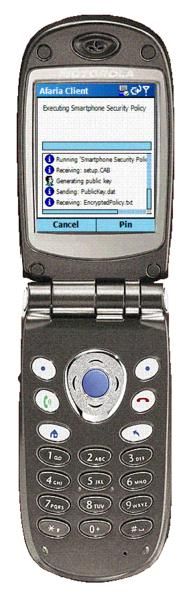 iAnywhere Afaria
iAnywhere AfariaTutorials Managing mobile devices and the flow of mobile data remains one of the most daunting tasks for the network manager. IT PRO shows you how you can use Afaria from iAnywhere to simplify the process.
By Guy Matthews Published
Tutorials -
 Banks failing to act on business ID theft
Banks failing to act on business ID theftNews Legal experts raise concern over the lack of action from financial organisations to tackle online identity 'mimicking' of businesses by fraudsters.
By Guy Matthews Published
News
