PyPI packages succumb to Mailchimp phishing scam
The news comes after "fairly convincing" phishing emails from a Mailchimp account swindled developers into revealing credentials

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
Administrators at the Python Package Index (PyPi) registry have confirmed an active phishing campaign aimed at stealing credentials from package developers.
Django project board member Adam Johnson first broke the news on Twitter after receiving a suspicious email that urged him to comply with a mandatory process to validate any and all PyPI packages before September. The email reportedly came from a Mailchimp account.
RELATED RESOURCE
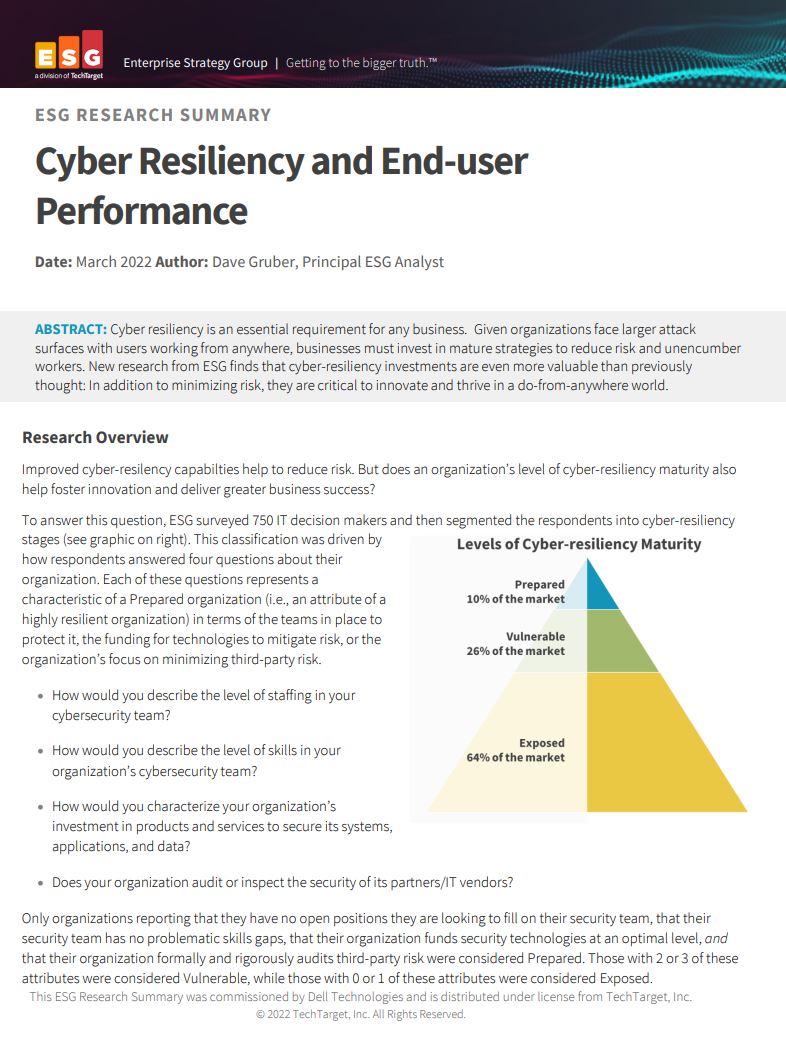
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
“Please validate your package with Google to avoid having your PyPi package removed from PyPi.org,” read the email.
Adding to the trickery, the mail said Google has mandated the validation process “due to a surge in malicious PyPi packages being uploaded to the PyPi.org domain".
The phishing site itself looks fairly convincing, according to Johnson. Consequently, a few unsuspecting developers entered their credentials on the malicious webpage that mirrored PyPI’s login page, which led to their creations getting hijacked.
“Exotel” (version 0.1.6) and “spam” (versions 2.0.2 and 4.0.2) are among the packages PyPI identified as compromised and rife with malware.
The aforementioned releases have been eliminated from PyPI and associated maintainer accounts are temporarily inaccessible. “We’ve additionally taken down several hundred typosquats that fit the same pattern,” added PyPI’s Security team.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
PyPI also recommended users enable two-factor authentication, ideally through hardware security keys or WebAuthn two-factor authentication, as a precaution. In the event that a developer already entered credentials on the phishing site, PyPI recommends resetting the password, 2FA recovery codes, and reviewing the account for any suspicious activity.
-
 Can we disrupt the data center designs?
Can we disrupt the data center designs?In-depth Distributed approaches or new power sources could enable data centers to grow with minimal harm to the environment
-
 Surging memory costs are scuppering digital transformation projects
Surging memory costs are scuppering digital transformation projectsNews Most organizations are already affected by memory cost increases, with no light at the end of the tunnel any time soon