Security, Information And Event Management (SIEM)
-
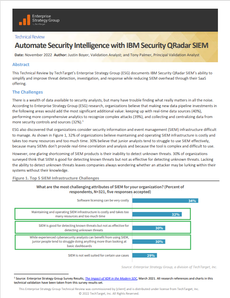 Automate security intelligence with IBM Security QRadar SIEM
Automate security intelligence with IBM Security QRadar SIEMWhitepaper Simplify and improve threat detection, investigation and response with reducing overheads
By ITPro Published
Whitepaper -
 How governments can build resilience in a new normal
How governments can build resilience in a new normalWhitepaper The cloud enables the flexibility public organisations need to overcome disruption
By ITPro Published
Whitepaper -
 The event mesh: A primer
The event mesh: A primerWhitepaper Benefits of an event-driven architecture
By ITPro Published
Whitepaper -
 Customer identity and access management for dummies
Customer identity and access management for dummiesWhitepaper Why CIAM matters now (more than ever) and what to look for in a CIAM solution
By ITPro Published
Whitepaper -
 From zero to hero: The path to CIAM maturity
From zero to hero: The path to CIAM maturityWhitepaper Your guide to the CIAM journey
By ITPro Published
Whitepaper -
 Five questions to ask before you upgrade to a modern SIEM
Five questions to ask before you upgrade to a modern SIEMWhitepaper Do you need a better defense strategy?
By ITPro Published
Whitepaper -
 Aberdeen Report: How a platform approach to security monitoring initiatives adds value
Aberdeen Report: How a platform approach to security monitoring initiatives adds valueWhitepaper Integration, orchestration, analytics, automation, and the need for speed
By ITPro Published
Whitepaper -
 ManageEngine Log360 review: SIEM for all seasons
ManageEngine Log360 review: SIEM for all seasonsReviews ManageEngine shows log management needn’t cost a king’s ransom
By Dave Mitchell Published
Reviews -
 Embracing automation will produce better analysts
Embracing automation will produce better analystsAnalysis There’s no reason why we shouldn’t be automating menial security processes in 2019, according to McAfee
By Connor Jones Published
Analysis -
 Most Android apps share data with Facebook without consent
Most Android apps share data with Facebook without consentNews The social media giant’s third-party tracking via the Facebook SDK may constitute a GDPR breach
By Keumars Afifi-Sabet Published
News -
 Kali Linux installation on Windows 10
Kali Linux installation on Windows 10Tutorials Follow these simple steps to install the security-focused Linux distro from the Microsoft Store
By Bobby Hellard Published
Tutorials -
 Security giants go cloud crazy with RSA launches
Security giants go cloud crazy with RSA launchesNews HP and RSA are two of the biggest firms launching cloudy products on the first day of the major security conference.
By Tom Brewster Published
News