Check Point 2210 Appliance review
Check Point's new 2200 Appliances combined enterprise level network security with an SMB price tag. Its software blades provide a wealth of features, but do they complicate deployment? Read this exclusive review to find out.
Check Point’s SmartConsole management and monitoring tools are geared up towards handling multiple appliances and this makes the 2210 best suited to remote office deployment or offered as a managed security solution. SMBs will find the appliance offers a very impressive range of features that perform well for the price, but as a standalone product it’s not the easiest to deploy and manage.

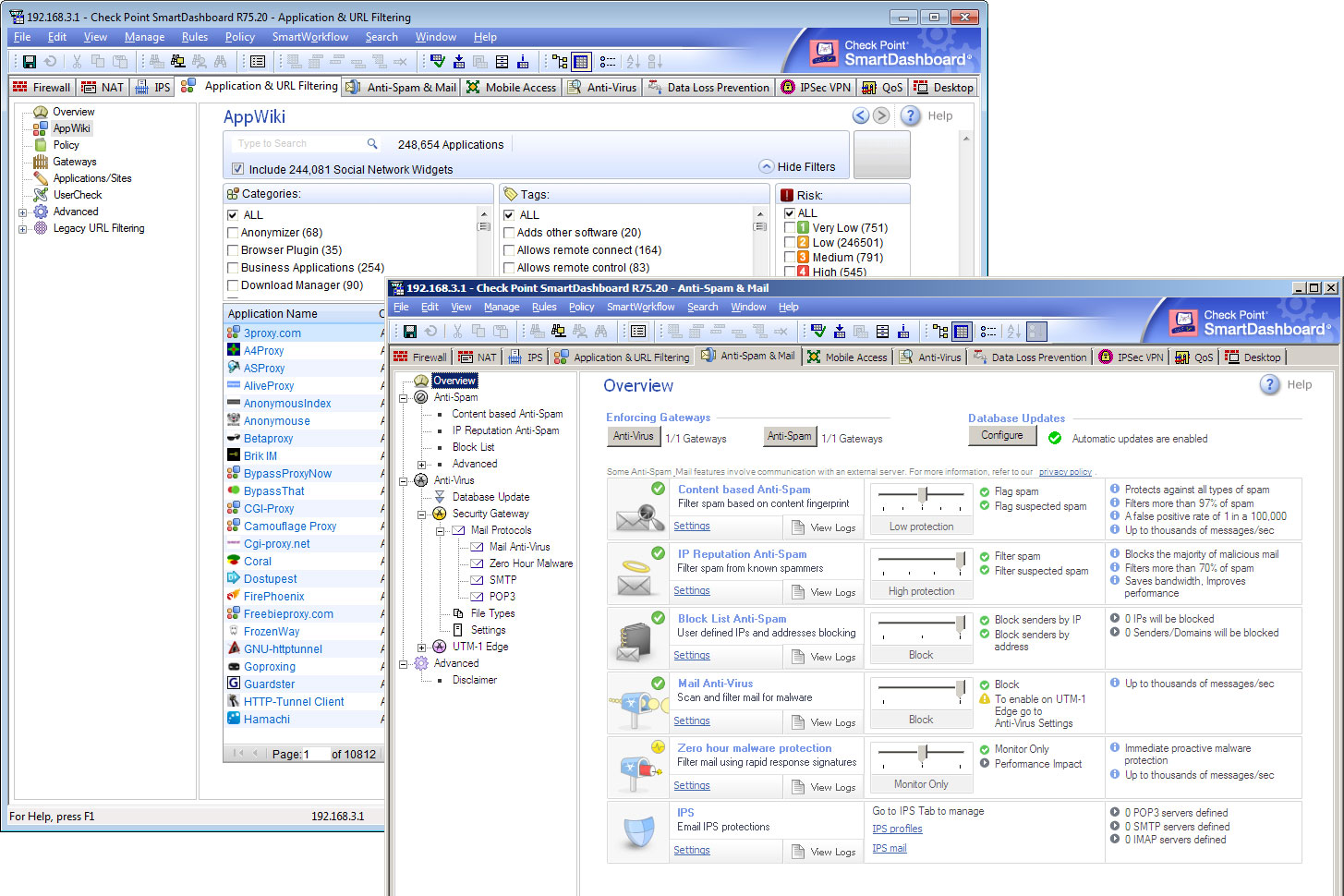
For all further security policy and blade management you download the SmartConsole software directly from the appliance. This installs a heap of management and monitoring utilities which includes the SmartDashboard for creating and deploying security policies.
A row of tabbed folders provides easy access to all the components. A network object is automatically created for the appliance and selecting it loads a properties window where you can activate each software blade.
All traffic is blocked by default so you need to create firewall rules which comprise source and destination objects, services, time schedules and logging options. Plenty of rule actions are possible as you can permit, deny or drop traffic and enforce user authentication.
Check Point has augmented its URL filtering services with a new AppWiki feature, so it doesn't just rely on traditional category databases. AppWiki makes the web filtering blade far more versatile as it provides a database of over 4,500 Web 2.0 apps, options for controlling specific Facebook activities and a list of nearly 250,000 social network widgets.
During testing we found this blade performed extremely well with very few web sites slipping past our filtering policies. For each policy you can block or allow access, request authentication and present warning web pages, redirect users or display a page informing them that an AUP is in place.
The anti-spam blade also performed well during testing with live mail as it returned a high detection rate of 98 per cent over a two week period. However, we had to tweak the confidence score for suspected spam as it was initially throwing up too many false positives.
The mobile access blade is a new feature and is designed to provide secure access for remote workers using PCs, laptops or mobile devices that want to access corporate resources. A wizard takes you through the process of creating SSL VPN portals, choosing which apps and resources are to be made available and picking an authentication method.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.
-
 Anthropic's Claude Cowork tool is coming to Microsoft Copilot
Anthropic's Claude Cowork tool is coming to Microsoft CopilotNews The new Copilot Cowork tool will be made available through a new Microsoft 365 tier at the end of March
By Ross Kelly Published
-
 MariaDB snaps up GridGain in AI push
MariaDB snaps up GridGain in AI pushNews GridGain’s in-memory computing technology will be integrated with MariaDB’s relational database platform to enable sub-millisecond data infrastructure
By Daniel Todd Published
-
 Is your new hire an AI clone? Microsoft says North Korean hackers are using AI to impersonate job seekers and steal company secrets
Is your new hire an AI clone? Microsoft says North Korean hackers are using AI to impersonate job seekers and steal company secretsNews The groups are increasingly using face-changing or voice-changing software to make their fake identities more plausible
By Emma Woollacott Published
