Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
A serious design flaw reportedly present in all Intel's CPUs made in the last 10 years could leave devices vulnerable to hackers, requiring an operating system (OS) update in order to fix it.
The flaw allegedly affects all systems running Intel x86 chips and is present across all popular operating systems, including Windows, Linux, and macOS, but is currently under embargo, meaning the full details of the bug are yet to be officially announced.
The bug allows normal user programs, such as database applications and JavaScript in web browsers, to distinguish some of the layout or contents of protected kernel memory areas of the chips, according to The Register, which uncovered the vulnerability.
However, the major problem for users is that a patch to the flaw will actually cause significant declines in performance for the affected machines, the publication said. These slow-downs could impact performance by as much as 30%, depending on the task and the processor model, but they're reportedly still being benchmarked.
The full details of the bug are expected to be revealed later this month. Microsoft is also expected to publicly introduce the necessary changes to its Windows operating system in an upcoming Patch Tuesday this month, after seeding them to beta testers running fast-ring Windows Insider builds in November and December.
A software developer who runs a popular Tumblr called Python Sweetness, has blogged about the potential trouble this flaw could cause once it's made official. They warned that "from everything I've seen, including the vendors involved, many fireworks and much drama is likely" when the embargo lifts.
"In the worst case the software fix causes huge slowdowns in typical workloads. There are hints the attack impacts common virtualisation environments including Amazon EC2 and Google Compute Engine, and additional hints the exact attack may involve a new variant of Rowhammer," they explained.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
"I would not be surprised if we start 2018 with the release of the mother of all hypervisor privilege escalation bugs, or something similarly systematic as to drive so much urgency, and the presence of so many interesting names on the patch set's CC list."
An Intel spokesperson said that "many different vendors and operating systems" are vulnerable to the bug.
They added: "Intel is committed to product and customer security and is working closely with many other technology companies, including AMD, ARM Holdings and several operating system vendors, to develop an industry-wide approach to resolve this issue promptly and constructively. Intel has begun providing software and firmware updates to mitigate these exploits.
"Check with your operating system vendor or system manufacturer and apply any available updates as soon as they are available. Following good security practices that protect against malware in general will also help protect against possible exploitation until updates can be applied."
Picture: Bigstock
-
 Can we disrupt the data center designs?
Can we disrupt the data center designs?In-depth Distributed approaches or new power sources could enable data centers to grow with minimal harm to the environment
-
 Surging memory costs are scuppering digital transformation projects
Surging memory costs are scuppering digital transformation projectsNews Most organizations are already affected by memory cost increases, with no light at the end of the tunnel any time soon
-
 AWS opens physical sites for fast data uploads – but it could cost you up to $500 an hour
AWS opens physical sites for fast data uploads – but it could cost you up to $500 an hourNews Amazon Web Service (AWS) has launched a new Data Transfer Terminal service to allow customers to upload data to the cloud from a physical site.
-
 The biggest cloud security risk in 2024 will be stolen and exposed credentials
The biggest cloud security risk in 2024 will be stolen and exposed credentialsNews Locking down accounts with multifactor authentication and investigating password breaches could help keep attackers out
-
 Amazon to retire iconic EC2-Classic network
Amazon to retire iconic EC2-Classic networkNews Customers will have until 2022 to migrate from the 15-year-old network to VPC
-
 AWS Re:Invent: AWS takes wraps off two new EC2 instances
AWS Re:Invent: AWS takes wraps off two new EC2 instancesNews Cloud services firm uses second day of customer conference to debut new instances, as well as a cloud-based data processing service.
-
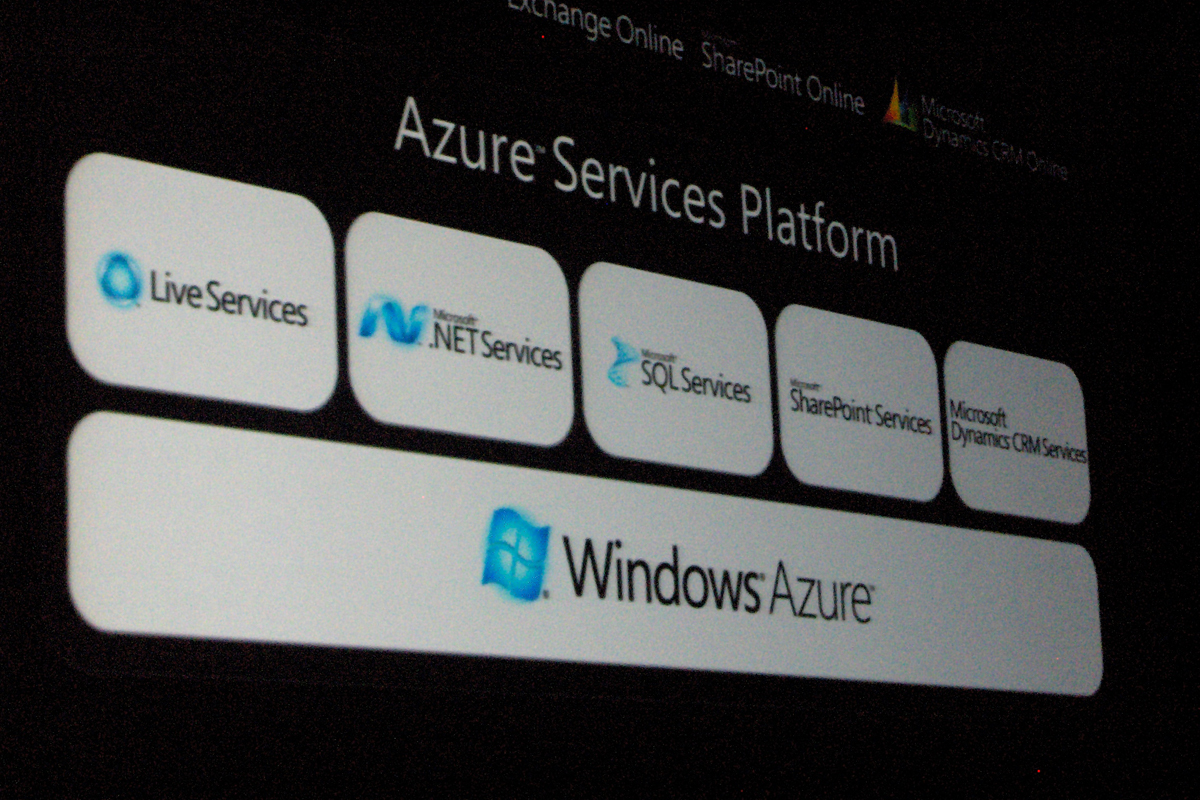 Microsoft unveils Azure cloud computing platform
Microsoft unveils Azure cloud computing platformNews Enterprise applications from Microsoft and third parties set to move into the cloud as the Windows maker reveals its enterprise utility computing ambitions.