Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expect
The Claude Mythos developer is aiming for a more limited approach to cyber tooling for public consumption


Anthropic has announced the public beta for Claude Security, its cybersecurity tool used for scanning codebases, detecting vulnerabilities, and generating patches.
Claude Security can scan full enterprise repositories to flag potential flaws – then open Claude Code to fix them – to reduce detection and response to one session for cyber workers.
In a video demo, Anthropic showed how Claude Security can conduct scans in just a single click, which prompts the tool to analyze relationships between components, data usage, and the viability of source code.
The tool then provides a list of potential vulnerabilities, including how each flaw can be reproduced and justifications for how severe they are. Along the way, Claude Security suggests how confident it is that the vulnerabilities it detects are legitimate.
Claude Security is accessible directly within Claude, or via a dedicated page on its website.
"Strong potential" with Claude Security
Claude Security was previously known as Claude Code Security, which Anthropic first made available to select organizations as a research preview.
The firm said it has collected feedback from hundreds of firms, which has helped make Claude Security more useful for enterprise applications.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
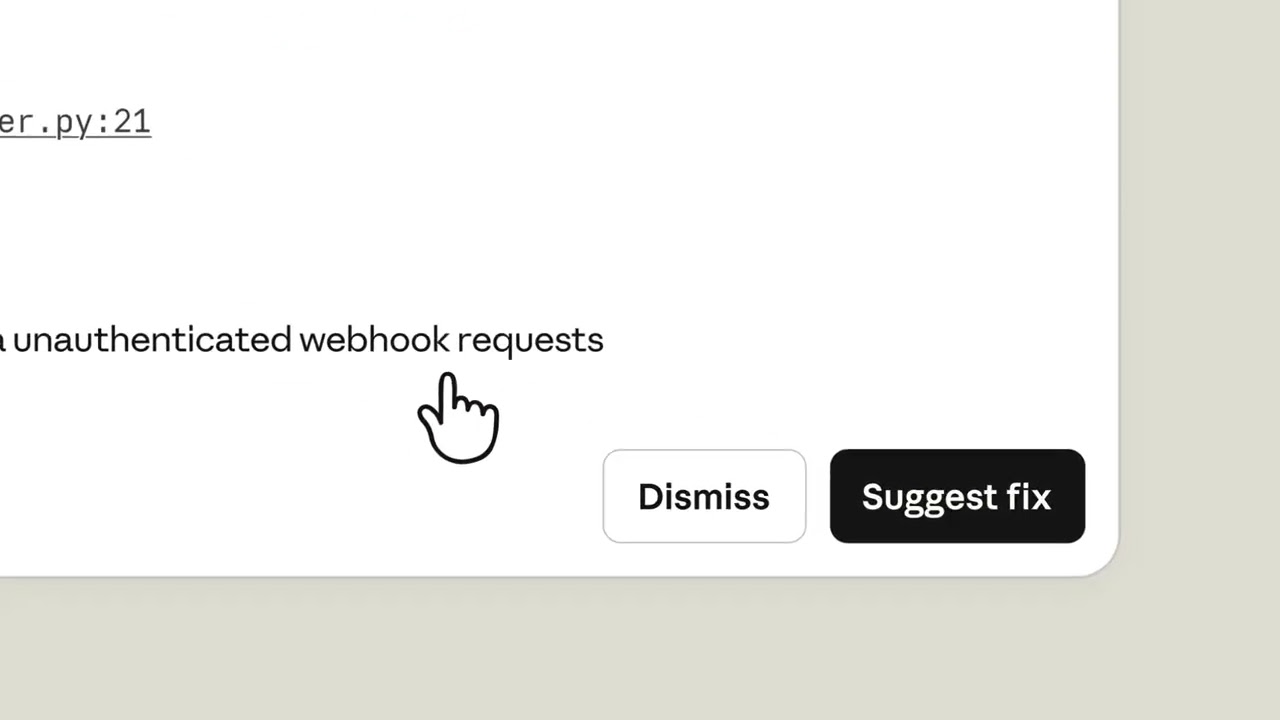
For example, Anthropic tweaked the tool to place a greater emphasis on validating AI findings, attaching a confidence percentage to each finding to reduce false positives.
New additions also include scheduled and targeted scans, as well as the option to export findings to Slack, Jira, or as CSV and Markdown files.
"Claude Security surfaced novel, high-quality findings during our early testing of the research preview that helped us identify and address potential security issues before they could affect our environment or our customers,” said Krzysztof Katowicz-Kowalewski, staff product security engineer at Snowflake.
“We see strong potential as we expand its use."
Concerns over AI security threats
Claude Security is underpinned by Claude Opus 4.7, Anthropic’s latest model which comes with embedded cyber guardrails. These are intended to prevent users from using the model for high-risk security tasks.
Anthropic’s new commitment to gating its cyber capabilities comes in the wake of its Project Glasswing launch, which saw it provide its most capable cyber model Claude Mythos Preview to select partners but not the public over safety concerns.
The UK’s AI Security Institute (AISI) has independently verified that the model is more capable at cyber tasks, and that it was the first to complete a 32-step enterprise network attack simulation designed to test LLM cyber exploit capabilities.
“Mythos Preview’s success on one cyber range indicates that it is at least capable of autonomously attacking small, weakly defended and vulnerable enterprise systems where access to a network has been gained,” the researchers noted.
However, they added that there are differences between real-world environments and simulations, such as the lack of proactive human defenders, which make it difficult to confirm that a model such as Mythos Preview could successfully breach well-defended systems.
FOLLOW US ON SOCIAL MEDIA
Follow ITPro on Google News and add us as a preferred source to keep tabs on all our latest news, analysis, views, and reviews.
You can also follow ITPro on LinkedIn, X, Facebook, and BlueSky.

Rory Bathgate is Features and Multimedia Editor at ITPro, overseeing all in-depth content and case studies. He can also be found co-hosting the ITPro Podcast with Jane McCallion, swapping a keyboard for a microphone to discuss the latest learnings with thought leaders from across the tech sector.
In his free time, Rory enjoys photography, video editing, and good science fiction. After graduating from the University of Kent with a BA in English and American Literature, Rory undertook an MA in Eighteenth-Century Studies at King’s College London. He joined ITPro in 2022 as a graduate, following four years in student journalism. You can contact Rory at rory.bathgate@futurenet.com or on LinkedIn.
-
 AWS CEO Matt Garman is bullish on the future of SaaS
AWS CEO Matt Garman is bullish on the future of SaaSNews Matt Garman said fears over the ‘SaaSpocalypse’ were overblown in February, now AWS is making big moves in the SaaS space
-
 Developers warned to avoid 'early-access' Google Gemini tools
Developers warned to avoid 'early-access' Google Gemini toolsNews Attackers are tempting would-be users into downloading reverse shell malware
-
 Researchers warn millions of RDP and VNC servers are wide open to exploitation
Researchers warn millions of RDP and VNC servers are wide open to exploitationNews Researchers at Forescout spotted millions of RDP and VNC servers exposed online
-
 AI agents using Anthropic MCP could be a vector for supply chain attacks, claim researchers
AI agents using Anthropic MCP could be a vector for supply chain attacks, claim researchersNews The flaw in Anthropic’s Model Context Protocol agent communication standard could put millions of agents and 200,000 servers at risk, report says
-
 Brace yourselves for a vulnerability explosion, Forescout warns
Brace yourselves for a vulnerability explosion, Forescout warnsNews AI advances are helping identify software flaws at record pace and scale, but that's not the good news some would think
-
 AI is raising the stakes for cyber professionals – Claude Mythos just took things to another level
AI is raising the stakes for cyber professionals – Claude Mythos just took things to another levelNews AI efficiency gains work both ways, and threat actors are already capitalizing on powerful new tools
-
 ‘There was a manual deploy step that should have been better automated’: Claude Code creator confirms cause of massive source code leak
‘There was a manual deploy step that should have been better automated’: Claude Code creator confirms cause of massive source code leakNews Over half a million lines of Claude Code source code was leaked, with the company attributing the blunder to human error
-
 Ubuntu vulnerability exposes enterprises to root escalation, complete system compromise
Ubuntu vulnerability exposes enterprises to root escalation, complete system compromiseNews The high-severity Ubuntu vulnerability allows an unprivileged local attacker to escalate privileges through the interaction of two standard system components
-
 Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerability
Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerabilityNews Threat actors have been exploiting the vulnerability to achieve root access since 2023
-
 Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourself
Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourselfNews The VS Code vulnerabilities highlight broader IDE security risks, said OX Security