Unleashing the power of AI initiatives with the right infrastructure
What key infrastructure requirements are needed to implement AI effectively?

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful

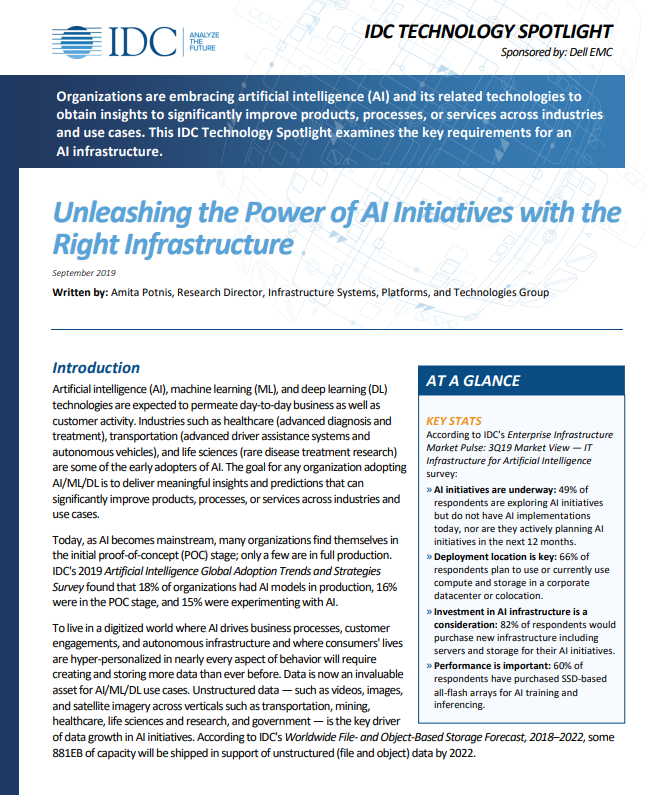
Organisations are embracing artificial intelligence and its related technologies to obtain insights to significantly improve products, processes or services across industries and use cases.
Today, as AI becomes mainstream, many organisations find themselves in the initial proof-of-concept stage. To grow to a stage where AI is driving business processes, more data will be created and stored than ever before.
This IDC Technology Spotlight examines the key requirements for an AI infrastructure, including highlighting the growing pain points for any IT organisation managing such infrastructure and how to optimise the combination of compute and storage to set up the ideal AI infrastructure.
Learn more about Dell Technologies solutions powered by Intel®
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
ITPro is a global business technology website providing the latest news, analysis, and business insight for IT decision-makers. Whether it's cyber security, cloud computing, IT infrastructure, or business strategy, we aim to equip leaders with the data they need to make informed IT investments.
For regular updates delivered to your inbox and social feeds, be sure to sign up to our daily newsletter and follow on us LinkedIn and Twitter.
-
 UK firms ponder offshoring AI workloads as energy costs surge
UK firms ponder offshoring AI workloads as energy costs surgeNews A CUDO Compute report confirms power prices are impacting the ability to rollout AI
-
 Cisco is expanding its sovereign infrastructure suite for EMEA customers
Cisco is expanding its sovereign infrastructure suite for EMEA customersNews Customers will get greater choice and control over their data and digital infrastructure, according to Cisco
