The endpoint as a key element of your security infrastructure
Threats to endpoints in a world of remote working

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful

With the rapid growth of remote access to corporate resources and cloud-based applications through a variety of personal devices, endpoints are now being attacked from all sides by attackers drawn to lowered security defences. Through email-based phishing, ransomware, malware, and drive-by downloads from web surfing, attacks are growing in volume and complexity to the point of several hundred thousand new programmes registered every day.
Since endpoints often store a large amount of corporate data and all the information an attacker needs to break into corporate networks, you need to ensure you have a robust endpoint protection strategy in place.
This whitepaper provides information about the types of security threats your business may be currently open to and outlines the dynamics of protecting endpoints. By downloading this whitepaper, you’ll find out more about leveraging your workforce, strategy, and technology investments in order to make the endpoints across your business as secure as possible.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
ITPro is a global business technology website providing the latest news, analysis, and business insight for IT decision-makers. Whether it's cyber security, cloud computing, IT infrastructure, or business strategy, we aim to equip leaders with the data they need to make informed IT investments.
For regular updates delivered to your inbox and social feeds, be sure to sign up to our daily newsletter and follow on us LinkedIn and Twitter.
-
 AWS UK chief touts big gains with AI-powered coding
AWS UK chief touts big gains with AI-powered codingNews Developers at AWS were able to speed up delivery of what would have traditionally been an extensive project
-
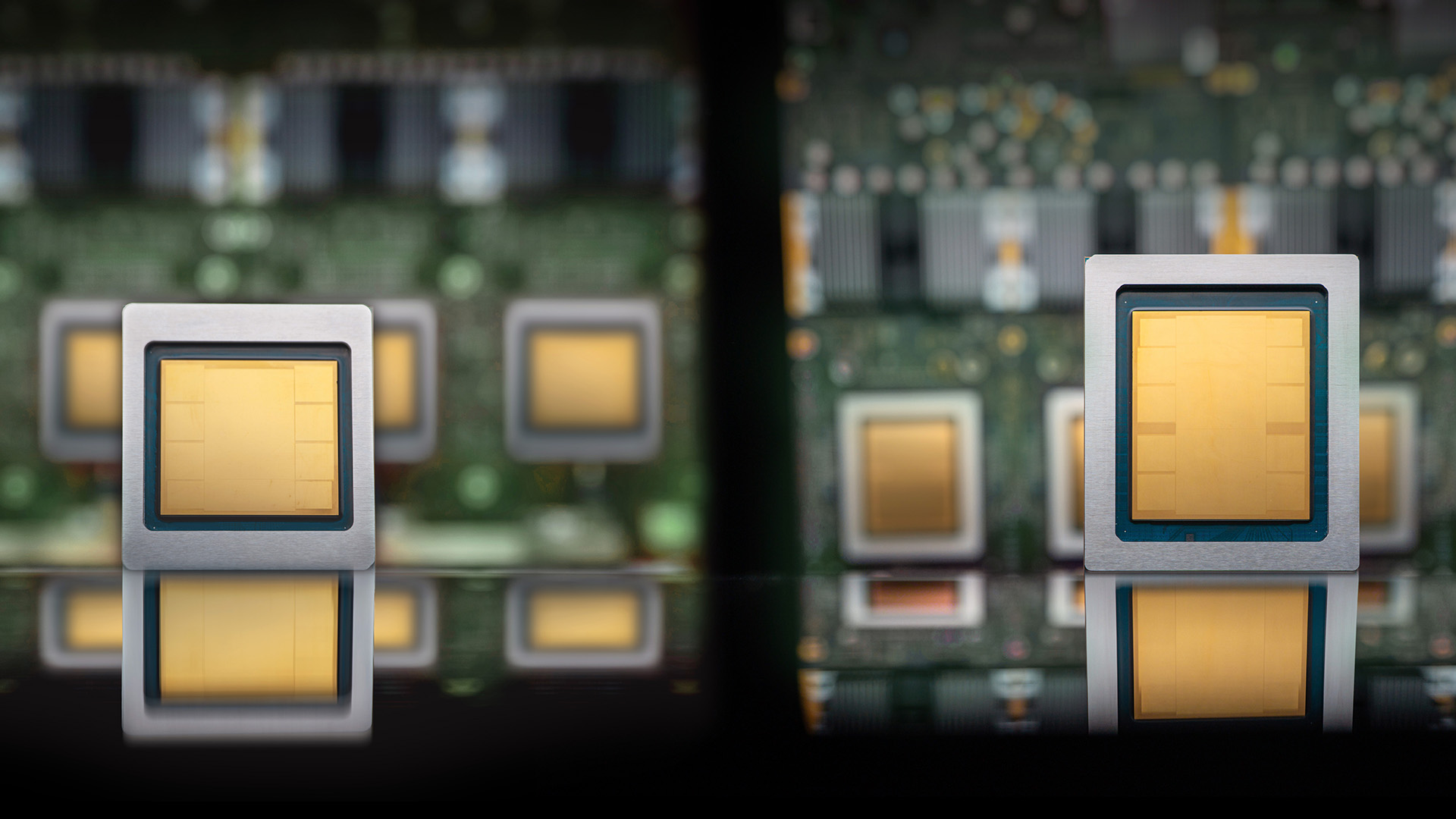 Google Cloud announces eighth-generation TPUs, boasting AI training and inference leaps
Google Cloud announces eighth-generation TPUs, boasting AI training and inference leapsNews Alongside chip improvements, Google Cloud has overhauled its data center fabric and file systems to support enterprise-scale AI deployment
