Chrome malware masquerades as 'missing font' files
New hack tricks users into downloading missing fonts loaded with malicious files

A security researcher has discovered a new hacking tactic on Google Chrome that manipulates websites into displaying missing font prompts, which then trick users into downloading malicious files.
The infection was first spotted on an unnamed WordPress website by Mahmoud Al-Qudsi, a researcher at cybersecurity firm NeoSmart Technologies, who detailed the process in a blog post.
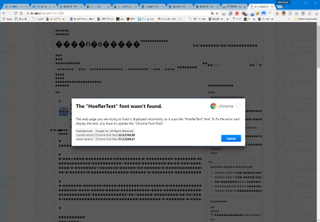
The attack involves a hacker exploiting JavaScript to alter the rendering of content on a webpage, causing it to resemble mis-encoded text which appears as a jumble of symbols and shapes. The code then prompts the user to download the missing fonts through a Chrome language pack to decipher the text.
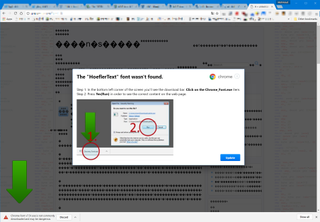
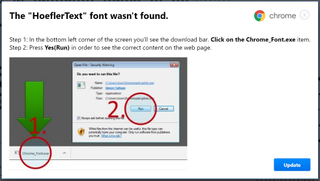
Clicking "Update" results in a file called "Chrome Font v7.5.1.exe" being downloaded and a second prompt encourages the user to run the file, all the while appearing as a perfectly safe Chrome download.
The attack is particularly well disguised and makes every attempt to appear a legitimate Chrome pop up, including the correct text formatting and right use of colours for the "Update" button.
"This attack gets a lot of things right that many others fail at," said Al-Qudsi. "The premise is actually believable: the text doesn't render, and it says that it is caused by a missing font (Hoefler Text, which is a real font), which it then prompts you to download and install."
"The shape of the update button seems correct, and the spelling and grammar are definitely good enough to get a pass."
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
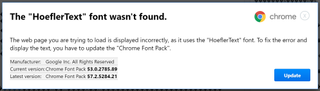
Al-Qudsi does identify some tell-tale signs that the prompt is not all as it seems. A savvy user will know what version of Chrome they are running, in this case version 56, however the prompt has version 53 hard-coded into its dialogue. It also features a rather conspicuous 'X' in the top right corner, which gives the game away, according to Al-Qudsi.
However once the file is downloaded, the quality of the scam "takes a nosedive", with text appearing blurry on prompts, and inconsistent file names for the downloaded material.
Although Chrome will notify the user with a "this file isn't downloaded very often" warning, it will not catch the download as a malicious file. It also slips by Windows Defender, and a check of virus scanning database VirusTotal reveals that only nine of 59 recorded antivirus scanners are able to correctly identify the file as malware.
Al-Qudsi has forwarded the discovery on to Google's security team, but pending an update patch, Chrome still fails to identify the file as malware. The firm advises users to be extra vigilant against these types of download prompts.
Pictures courtesy of NeoSmart
Dale Walker is the Managing Editor of ITPro, and its sibling sites CloudPro and ChannelPro. Dale has a keen interest in IT regulations, data protection, and cyber security. He spent a number of years reporting for ITPro from numerous domestic and international events, including IBM, Red Hat, Google, and has been a regular reporter for Microsoft's various yearly showcases, including Ignite.




