The North Face hit by credential stuffing attack
Following the incident, hackers gained fraudulent access to 194,905 customer accounts

The North Face has confirmed it was hit by a credential stuffing attack that exposed the personally identifiable information of its customers.
A preliminary examination of the cyber security incident indicated the American clothing firm’s website was compromised as early as July 26. However, North Face only learned of the attack on 11 August.
The top 12 password-cracking techniques used by hackers Top 200 most common passwords of 2021 revealed What is cyber security?
Although the attack was contained by August 19, North Face noted that the perpetrators gained access to nearly 200,000 customer accounts using valid credentials.
The attacker’s modus operandi, credential stuffing, allowed the automated entry and use of stolen usernames and passwords on the company's website.
Customer name, purchase history, billing address, shipping address, telephone number, account creation date, gender, and XPLR Pass reward records were exposed in this attack. The North Face does not store sensitive financial information, so cyber criminals are unlikely to have gained access to customers’ payment details, including credit card numbers.
VF Corporation, the brand's parent company, is notifying customers of the data breach in response to the incident. A precautionary reset of all user passwords has been carried out. The firm also erased payment card tokens from accounts that were accessed during the attack timeframe.
"We do not keep a copy of payment card details on thenorthface.com. We only retain a "token" linked to your payment card, and only our third-party payment card processor keeps payment card details," explained North Face in a statement.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
RELATED RESOURCE
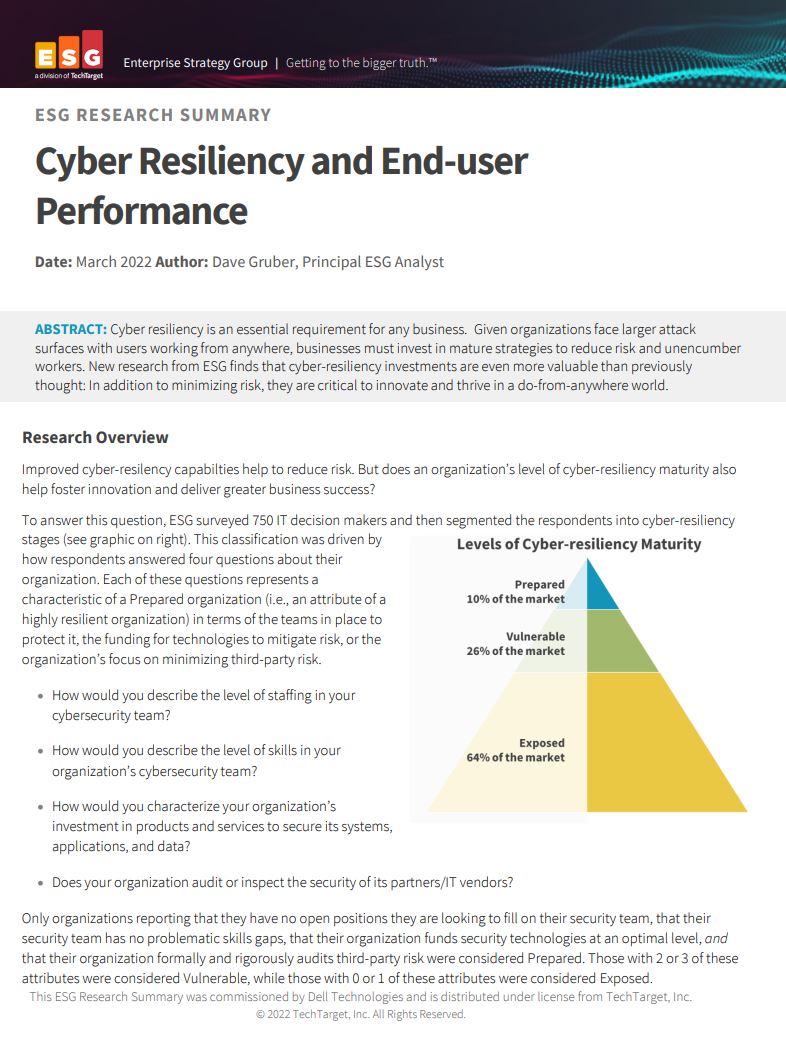
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
"The token cannot be used to initiate a purchase anywhere other than on thenorthface.com."
The recent attack is reportedly The North Face’s second credential stuffing security incident.
Back in 2020, The North Face reset passwords of an undisclosed number of customer accounts after detecting a credential stuffing attack on its website.
“We strongly encourage you not to use the same password for your account at thenorthface.com that you use on other websites. If a breach occurs on one of those other websites, an attacker could use your email address and password to access your account at thenorthface.com,” added the company.
-
 Dell unveils Deskside Agentic AI at Dell Technologies World 2026
Dell unveils Deskside Agentic AI at Dell Technologies World 2026News Deskside Agentic AI is the latest in the Dell AI Factory with Nvidia stable, with the company saying it further demonstrates its end-to-end enterprise AI capability
-
 Dell Technologies World 2026: all the news, updates, and announcements from the Day 1 keynote
Dell Technologies World 2026: all the news, updates, and announcements from the Day 1 keynoteKeep up to date with all the news as it happens live from Dell Technologies World 2026 in Las Vegas
