Phishing emails target victims with fake vaccine passport offer
Scammers could steal victims’ personal information and never deliver the illegal goods, Fortinet warns


Cyber criminals are using offering fake vaccine passports as lures in phishing email scams, according to security researchers at Fortinet.
“Successfully enticing the general population to open a malicious email attachment with the promise of receiving an illegal product may be a first. It reflects how polarizing this issue is and why cyber criminals think that they can successfully exploit it,” Fortinet said.
The researchers discovered an email with an advertisement for a fake COVID vaccine passport that requests Bitcoin payment. The Bitcoin address had zero transactions, which means no one seems to have yet fallen for this scam. The researchers were also unsure if the criminals behind the email would ever send a fake vaccine passport, or if it was a regular phishing exercise or even both.
“What's clear is that scammers ask the target for personally identifiable information (PII) along with USD 149.95 worth of Bitcoin for a potentially double windfall,” said researchers.
Other attempts appeared more professional using the Center for Disease Control’s (CDC) address to appear legitimate.
“The link in this email did not lead to any official document but instead redirected the user to a legitimate server that had been compromised. While the link has been taken down, indicators suggest that this compromised server was used in a phishing attempt,” said researchers.
Researchers also found markets on the dark web offering fake vaccine passports, ranging from blank vaccine cards to verifiable passports that can be checked against legitimate vaccine databases worldwide. They found a single blank vaccination card for $5, but researchers again added there was no guarantee a purchaser would ever receive these documents after paying.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Researchers said the demand for fake vaccine passports seems to be growing due to the large population of people who resist taking or are unable to take the vaccine but want to avoid restrictions.
“Without missing a beat, email scammers and black-market criminals have acted on this demand,” said researchers. “Because these criminals use phishing techniques to socially engineer and lure victims into following steps laid out by the attacker, it is vital to address these challenges.”
Researchers recommended organizations conduct ongoing training designed to educate and inform personnel about the latest phishing/spear-phishing techniques and how to spot and respond to them.
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
 Kaseya shifts from AI ‘insights’ to autonomous action with new agentic platform
Kaseya shifts from AI ‘insights’ to autonomous action with new agentic platformNews The company aims to evolve from its suite of management tools into an autonomous operating system for MSPs
-
 Accenture to roll-out Copilot to 700,000+ staff
Accenture to roll-out Copilot to 700,000+ staffNews Accenture will roll out Microsoft Copilot to nearly three quarters of a million employees after years of testing
-
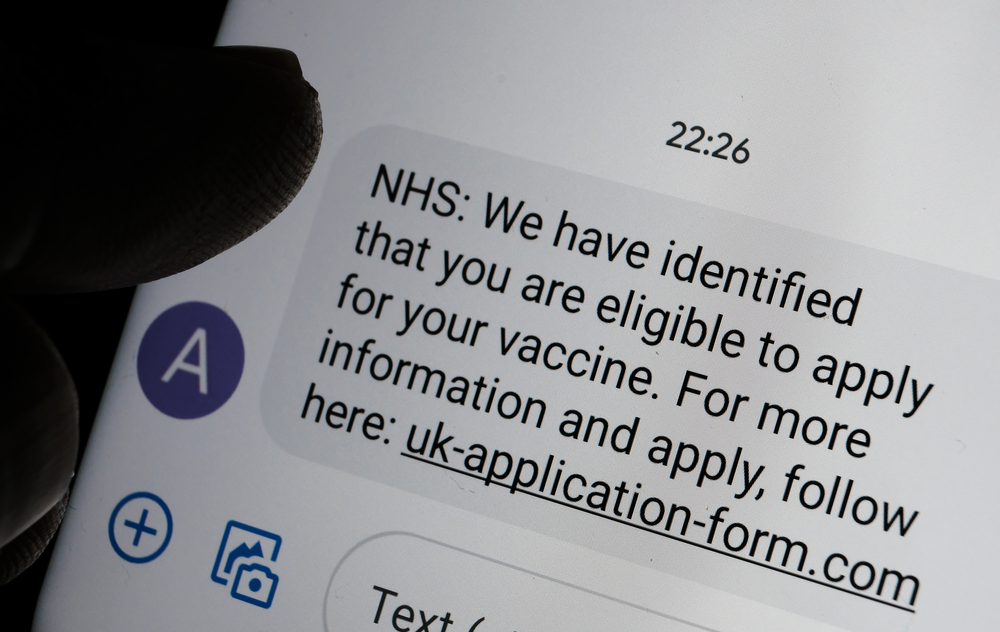 COVID-related phishing fuels a 15-fold increase in NCSC takedowns
COVID-related phishing fuels a 15-fold increase in NCSC takedownsNews The NCSC recorded a significant jump in the number of attacks using NHS branding to lure victims
-
 COVID vaccine passports will fail unless government wins public trust, ICO warns
COVID vaccine passports will fail unless government wins public trust, ICO warnsNews Data watchdog's chief Elizabeth Denham warns that it’s not good enough to claim ‘this is important, so trust us’
-
 Fake COVID vaccination certificates available on the dark web
Fake COVID vaccination certificates available on the dark webNews Fast-growing market emerges for people wanting quick vaccine proof to travel abroad
-
 Cyber security firm saw attacks rise by 20% during 2020
Cyber security firm saw attacks rise by 20% during 2020News Trend Micro found attackers also heavily targeted VPNs
-
 Hackers using COVID vaccine as a lure to spread malware
Hackers using COVID vaccine as a lure to spread malwareNews Cyber criminals are impersonating WHO, DHL, and vaccine manufacturers in phishing campaigns
-
 Website problems slow coronavirus vaccine rollout
Website problems slow coronavirus vaccine rolloutNews Florida is the epicenter of website issues, as patients struggle with malfunctioning sites and hackers
-
 NHS COVID-19 app failed to ask users to self-isolate due to 'software glitch'
NHS COVID-19 app failed to ask users to self-isolate due to 'software glitch'News The bug is the latest in a long line of errors and glitches to plague the government's contact-tracing app
-
 How businesses were left to scramble over data collection for coronavirus contact tracing
How businesses were left to scramble over data collection for coronavirus contact tracingIn-depth The lack of sufficient advice has opened the door for third-party tech firms to normalise massive-scale data harvesting
