CISA urges federal agencies to patch PrintNightmare flaw
The emergency directive comes after Microsoft security updates


The Cybersecurity and Infrastructure Security Agency (CISA) has told federal agencies to mitigate the Windows Print Spooler Service vulnerability, also known as PrintNightmare, that hackers are actively exploiting.
CISA issued the Emergency Directive 21-04 following Microsoft’s security updates that aim to fix the flaw in all supported versions of Windows.
The flaw enables hackers to remotely execute code with system-level privileges, allowing a threat actor to quickly compromise a targeted organization’s entire identity infrastructure. This compromise is possible because the Microsoft Print Spooler service improperly performs privileged file operations and fails to restrict access to functionality that allows users to add printers and related drivers.
This, in turn, allows a remote authenticated attacker to execute arbitrary code with system privileges on a vulnerable system.
CISA said it had validated various proofs of concept and was “concerned that exploitation of this vulnerability may lead to full system compromise of agency networks if left unmitigated.”
The agency said the vulnerability poses an unacceptable risk to Federal Civilian Executive Branch agencies and requires emergency action.
“This determination is based on the current exploitation of this vulnerability by threat actors in the wild, the likelihood of further exploitation of the vulnerability, the prevalence of the affected software in the federal enterprise, and the high potential for a compromise of agency information systems,” CISA warned.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
It said that all agencies must stop and disable the Print Spooler service on all Microsoft Active Directory (AD) Domain Controllers (DC) by 11:59 p.m. EDT on July 14.
By 11:59 p.m. EDT on July 20, agencies must apply the July 2021 cumulative updates to all Windows Servers and Workstations. At the same time, all hosts running Windows operating systems must either stop and disable the Print Spooler service on the host and configure Point and Print Restrictions Group Policy settings or override all Point and Print Restrictions Group Policy settings to ensure only administrators can install printer drivers changing registry settings on all hosts.
Agencies must also ensure technical and/or management controls are in place to ensure newly provisioned or previously disconnected servers and workstations are updated before connecting to agency networks by July 20.
CISA said the emergency directive would remain in effect until all agencies running Windows have “performed all required actions from this directive or the directive is terminated through other appropriate action.”
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
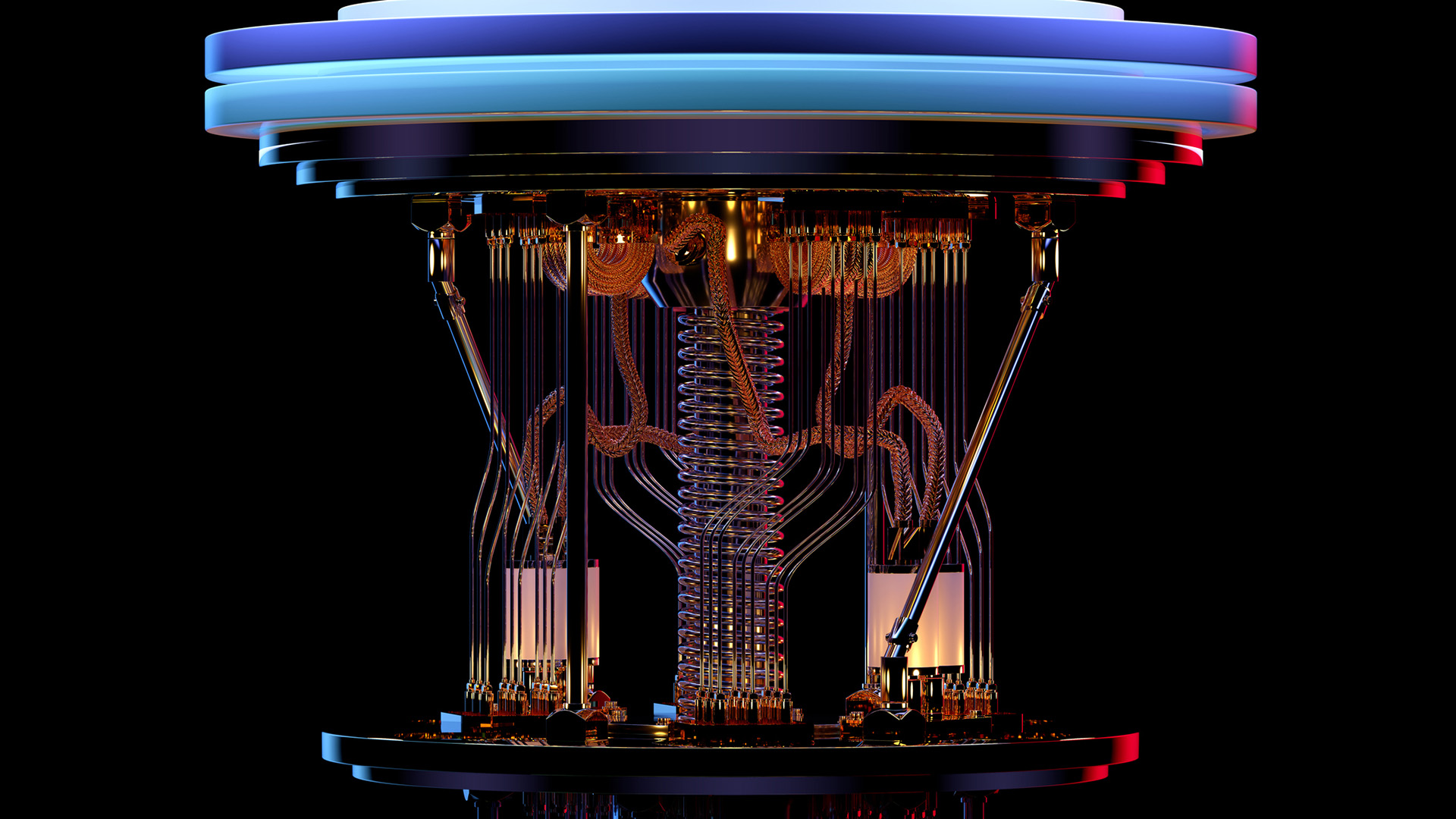 Bell Labs’ Michael Eggleston on Nokia’s research into topological quantum computing
Bell Labs’ Michael Eggleston on Nokia’s research into topological quantum computingInterview Bell Labs is known for developing radio astronomy technology, transistors and lasers – now owned by Nokia, its research is focusing on quantum computing
-
 Monetizing the quantum shift: 11 PQC channel opportunities
Monetizing the quantum shift: 11 PQC channel opportunitiesIndustry Insights Channel partners must lead clients through the post-quantum cryptography transition now.
-
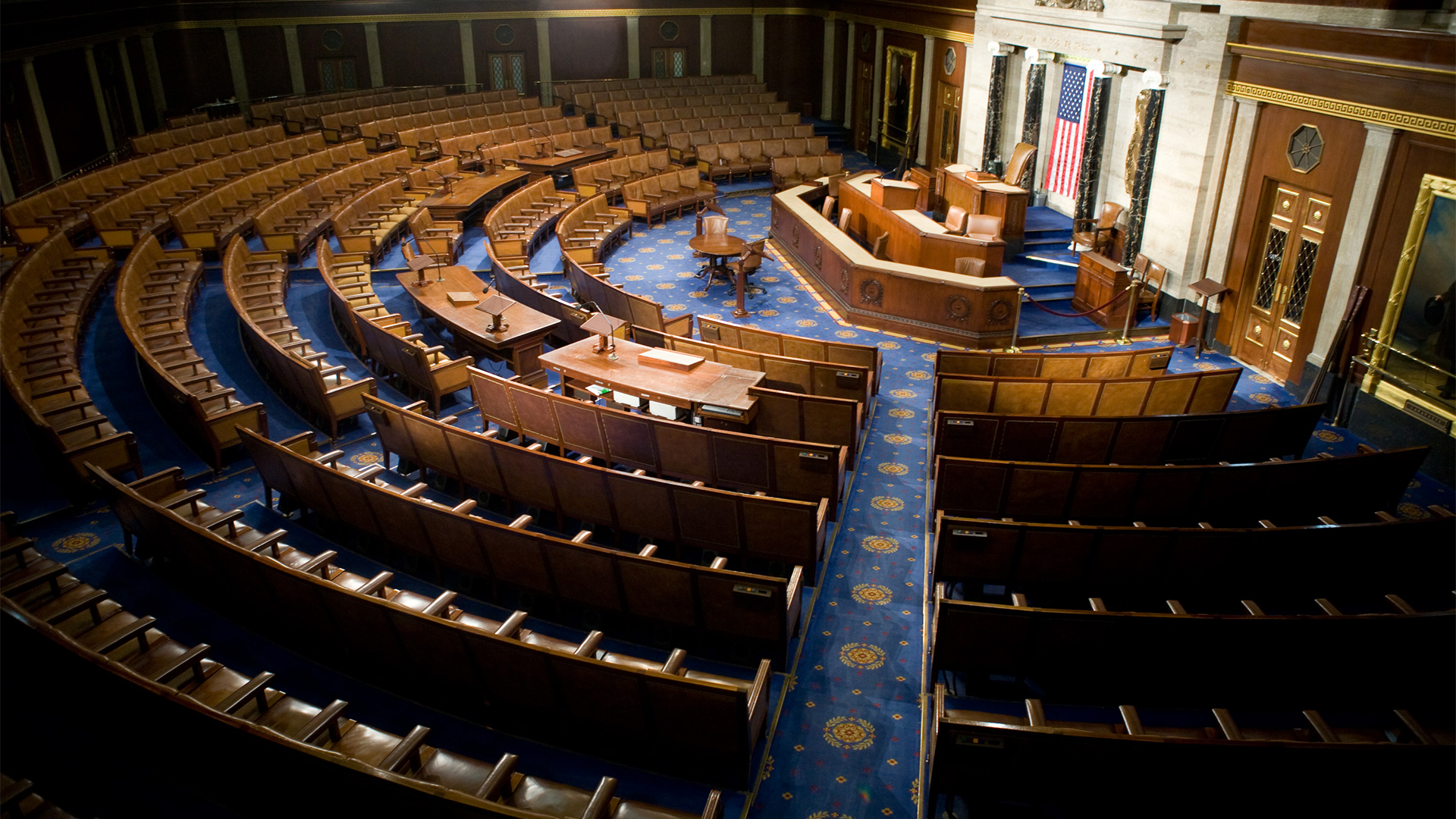 Salt Typhoon attack on US congressional email system ‘exposes how vulnerable core communications systems remain to nation-state actors’
Salt Typhoon attack on US congressional email system ‘exposes how vulnerable core communications systems remain to nation-state actors’News The Salt Typhoon campaign marks the latest in a string of attacks on US government communications networks
-
 ‘All US forces must now assume their networks are compromised’ after Salt Typhoon breach
‘All US forces must now assume their networks are compromised’ after Salt Typhoon breachNews The announcement marks the second major Salt Typhoon incident in the space of two years
-
 UK cyber experts on red alert after Salt Typhoon attacks on US telcos
UK cyber experts on red alert after Salt Typhoon attacks on US telcosAnalysis The UK could be next in a spate of state-sponsored attacks on telecoms infrastructure
-
 Healthcare data breaches are out of control – here's how the US plans to beef up security standards
Healthcare data breaches are out of control – here's how the US plans to beef up security standardsNews Changes to HIPAA security rules will require organizations to implement MFA, network segmentation, and more
-
 The US could be set to ban TP-Link routers
The US could be set to ban TP-Link routersNews US authorities could be lining up the largest equipment proscription since the 2019 ban on Huawei networking infrastructure
-
 US government IT contractor could face death penalty over espionage charges
US government IT contractor could face death penalty over espionage chargesNews The IT pro faces two espionage charges, each of which could lead to a death sentence or life imprisonment, prosecutors said
-
 US identifies and places $10 million bounty on LockBit, Hive ransomware kingpin
US identifies and places $10 million bounty on LockBit, Hive ransomware kingpinNews Mikhail Pavlovich Matveev was linked to specific ransomware attacks, including a 2021 raid on the DC police department
-
 Breach at US Transportation Department exposes 240,000 employee records
Breach at US Transportation Department exposes 240,000 employee recordsNews An investigation is underway into the breach, which affected former and current employee data
