Researchers warn of increase in attacks against Zoho software
It's believed as much as 62% of ServiceDesk Plus instances globally are using vulnerable software versions


Security researchers have observed a significant increase in the number of attacks against Zoho software, with a number of instances and organisations already affected across the world.
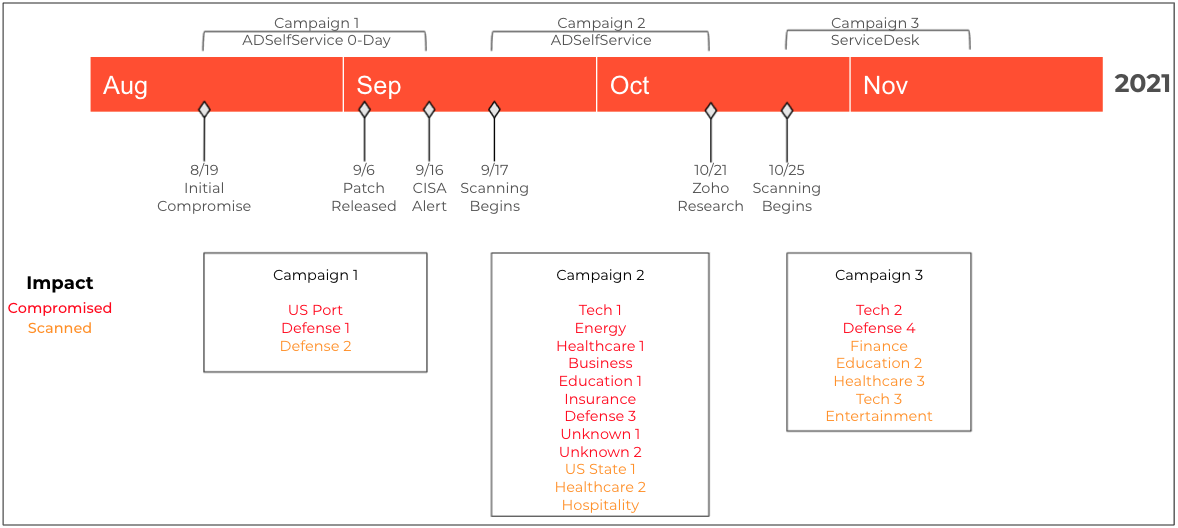
A total of 13 organisations across industries including defence, energy, technology supply chain, healthcare, and education have been compromised over a three-month period, according to Palo Alto Networks' Unit 42.
Successful exploitation of the software flaws can lead to remote code execution (RCE) and supply attacks using administrator privileges.
Attacks began back in September when CISA warned of cyber criminals exploiting a newly identified, critical-rated vulnerability, tracked as CVE-2021-40539, in ManageEngine ADSelfService Plus, a self-service password management and single sign-on solution product from Zoho.
Zoho issued a patch for the exploit in September, followed by an advisory on 22 November explaining the severity of the issue to customers and urging them to patch their systems.
However, researchers at Unit 42 drew attention to a second campaign targeting a different Zoho product in November. The exploit tracked as CVE-2021-44077 which affects ManageEngine ServiceDesk Plus, a help desk and asset management product, was more sophisticated and difficult to detect, researchers noted.
Unit 42 researchers determined that 47% of ADSelfService Plus and 62% of ServiceDesk Plus instances across the globe are still using vulnerable versions and have yet to be patched by customers.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The most recent findings from the past two weeks have confirmed an additional four businesses compromised using the vulnerabilities, two in ADSelfService Plus and two in ServiceDesk Plus, bringing the total to 13 after an initial nine cases were confirmed.
Researchers said they hadn't identified any publicly available proof of concept code for the exploit but observed that the group behind the attacks was indeed using one of their own exploits to compromise unpatched versions of the software.
The group used a variety of initial access vectors to breach Zoho's infrastructure, allowing them to drop a Godzilla webshell using RCE to provide the group with additional access and persistence in compromised systems.
Two requests were sent to the REST API allowing the attackers to upload the msiexec.exe executable and launch the malicious payload.
RELATED RESOURCE

Modernise endpoint protection and leave your legacy challenges behind
The risk of keeping your legacy endpoint security tools
Godzilla was used in attacks on both ADSelfService Plus and ServiceDesk Plus, but used different files. A Java Server Pages (JSP) file was used with ADSelfService Plus but Godzilla was dropped using an Apache Tomcat Java Servlet Filter with ServiceDesk Plus.
Using a filter allowed attackers to sift inbound and outbound requests to determine which were meant for the webshell. Installing Godzilla as a webshell also meant that there was no specific URL used by the group to send its requests to the webshell, and it could also bypass a ServiceDesk Plus security filter designed to stop webshells.
Unit 42 researchers said "the best defence against this evolving campaign is a security posture that favours prevention". Businesses are advised to patch all instances and assess the business need for all internet-facing Zoho products.
Zoho customers are also advised to review all files that have been created in the affected products since October 2021 and get in touch with Unit 42 if they think they are affected.
IT Pro has contacted Zoho for comment on the research.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Dell PowerRack launches at Dell Technologies World 2026 as a ‘turnkey’ networking, storage, and compute system for AI
Dell PowerRack launches at Dell Technologies World 2026 as a ‘turnkey’ networking, storage, and compute system for AIThe newly announced solution is designed to help organizations get up and running at super speed
-
 Dell unveils Deskside Agentic AI at Dell Technologies World 2026
Dell unveils Deskside Agentic AI at Dell Technologies World 2026News Deskside Agentic AI is the latest in the Dell AI Factory with Nvidia stable, with the company saying it further demonstrates its end-to-end enterprise AI capability
-
 Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expect
Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expectNews The Claude Mythos developer is aiming for a more limited approach to cyber tooling for public consumption
-
 Researchers warn millions of RDP and VNC servers are wide open to exploitation
Researchers warn millions of RDP and VNC servers are wide open to exploitationNews Researchers at Forescout spotted millions of RDP and VNC servers exposed online
-
 Brace yourselves for a vulnerability explosion, Forescout warns
Brace yourselves for a vulnerability explosion, Forescout warnsNews AI advances are helping identify software flaws at record pace and scale, but that's not the good news some would think
-
 Ubuntu vulnerability exposes enterprises to root escalation, complete system compromise
Ubuntu vulnerability exposes enterprises to root escalation, complete system compromiseNews The high-severity Ubuntu vulnerability allows an unprivileged local attacker to escalate privileges through the interaction of two standard system components
-
 Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerability
Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerabilityNews Threat actors have been exploiting the vulnerability to achieve root access since 2023
-
 Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourself
Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourselfNews The VS Code vulnerabilities highlight broader IDE security risks, said OX Security
-
 CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaught
CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaughtNews While the CVE figures might be daunting, they won't all be relevant to your organization
-
 Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to know
Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to knowNews Patch Tuesday update targets large number of vulnerabilities already being used by attackers
