GitLab phished its employees and 20% handed over credentials
The exercise was designed to test the susceptibility of GitLab's remote workforce
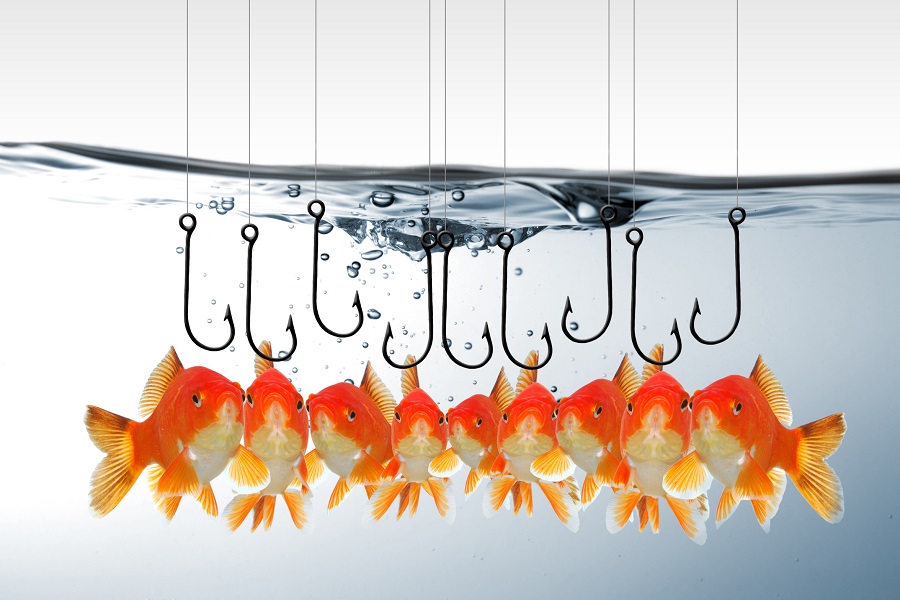
GitLab recently concluded a phishing campaign designed to target its remote employees.
The exercise sought to test the susceptibility of GitLab’s remote workforce, and 20% of employees fell for the attack by submitting their credentials to a fake login page.
While one in five is much better than average, it’s still more than GitLab would like to see. What was more alarming to GitLab was the number of employees who submitted the campaign to its security team.
The exercise was a simulated phishing campaign designed to secure the credentials of GitLab employees. By using the domain name gitlab.company, the GitLab Red Team - the team taking on the role of the attacker - used the open-source GoPhish framework and Google's GSuite to send unsuspecting GitLab employees targeted phishing emails.
"Targets were asked to click on a link in order to accept their upgrade and this link was instead a fake GitLab.com login page hosted on the domain 'gitlab.company'," explained Security Manager Steve Manzuik in a GitLab post.
"While an attacker would be able to easily capture both the username and password entered into the fake site, the Red Team determined that only capturing email addresses or login names was necessary for this exercise."
Of the 50 emails sent as part of the phishing campaign, 34% of recipients clicked on the link that led to the simulated phishing website. Of those who clicked, 59% went on to enter their GitLab credentials. Meanwhile, only 12% of recipients reported the phishing attempt to GitLab’s security personnel.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
In an email to The Register, Johnathan Hunt, VP of security at GitLab, shared, "Initially, the team had the assumption that more people would fall for the phishing scam but that assumption turned out to be false. Some vendors claim that the average rate of successful phishes is somewhere around 30-40% so it is nice to see us trending below that."
GitLab's findings shed additional light on cybersecurity concerns related to remote workers, which have grown in numbers due to the spread of the coronavirus.
Remote employees often become their own IT administrators, though not all work-from-home employees are up for the task. To address this, Hunt encourages companies to provide their employees with the knowledge they need to avoid falling for phishing campaigns.
"This means that companies, whether remote or not, should be training their staff to have a healthy level of caution when it comes to email communications," shared Hunt.
"As organizations move to being more remote and potentially leveraging cloud services, user identity management and multi-factor authentication become very important."
-
 ReMarkable Paper Pure review
ReMarkable Paper Pure reviewReviews More integrations and business features to make the distraction-free tablet a little bit more appealing
-
 SAP snaps up Dremio and Prior Labs in double AI acquisition
SAP snaps up Dremio and Prior Labs in double AI acquisitionNews The deals aim to strengthen SAP’s data foundations and sharpen its focus on tabular foundation models