Phishing attacks targeting US government have evolved in sophistication, Cofense reports
The scams are aimed at stealing federal employees' Microsoft 365 credentials

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
Phishing attacks targeting the US Departments of Labor, Commerce, or Transportation have evolved to become more convincing and evasive, Cofense Intelligence revealed.
The credential phishing campaigns, active since mid-2019, have been seen in environments protected by secure email gateways (SEGs), the company added.
RELATED RESOURCE
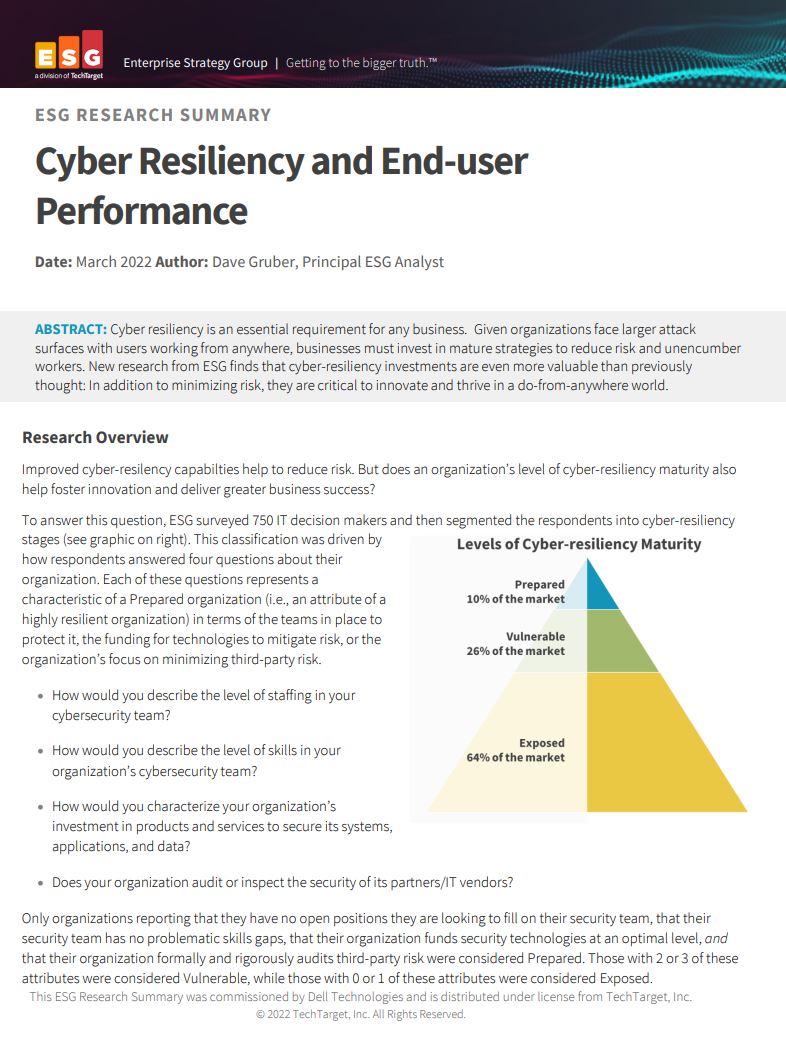
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
The emails have developed over time to incorporate legitimate-looking logos, signature blocks, and consistent formatting, including more detailed instructions in PDF documents. Typically, the emails included bid requests for lucrative government projects that lured recipients to phishing pages that mimicked legitimate federal agency websites.
Cybersecurity firm INKY detailed one such incident in January 2022, when threat actors used PDF attachments with instructions for bidding on the US Department of Labor projects.
Adding to the trickery, threat actors have also incorporated longer domain names, such as “transportation[.]gov[.]bidprocure[.]secure[.]akjackpot[.]com” in an attempt to make the website address look legitimate when accessed from mobile browsers that cannot display full-length URLs.
Additionally, on the phishing page that entices visitors into entering their Microsoft Office 365 account credentials, the threat actors have now added a Captcha Challenge step to prevent bots from participating.
“The only place where the threat actors fall slightly behind is their spoofed pages can be out of date, which will likely go unnoticed by most victims,” stated Cofense in its report.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
“Given the advancements seen in each area of the phishing chain, it is likely the threat actors behind these campaigns will continue to innovate and improve upon their already believable campaigns,” added Cofense.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles