Pennsylvania county shells out a $500K ransom to recover stolen data
Delaware County says election data remains securely tucked way on a separate network

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
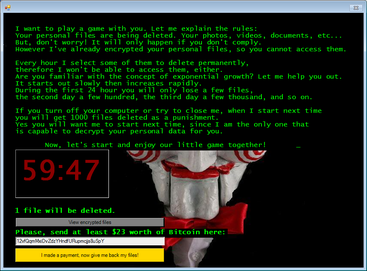
Last week, hackers stole data from Delaware County, Pennsylvania and asked for a $500,000 ransom. New reports claim the county has buckled and will use its insurance coverage to pay the fee and restore the data.
The cyber attack led to the county taking parts of its network offline when it discovered the compromise.
"The County of Delaware recently discovered a disruption to portions of its computer network. We commenced an immediate investigation that included taking certain systems offline and working with computer forensic specialists to determine the nature and scope of the event. We are working diligently to restore the functionality of our systems," said the county.
The county added that the Bureau of Elections and the County's Emergency Services Department were not impacted and were on separate computer networks from The County of Delaware.
“There is no evidence they were impacted by the disruption,” it added. “The County is working to resolve this issue as quickly as possible and will provide updates when they are available. Thank you for your patience as we work to restore the functionality of our systems.”
It is thought that the IP address for the Delaware County attack is tied to the Netherlands, but the attack could have originated elsewhere.
Chad Anderson, senior security researcher at DomainTools, told IT Pro that ransomware authors have increasingly gone after the double extortion attacks for the simple reason that this further encourages their victims to pay.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
“When sitting on a treasure trove of sensitive personal information, attackers know that the looming threat of exposing it on hacking forums gives them more leverage to instigate a payment. This all comes of course with an increasing number of businesses paying, further incentivizing attackers to use this extra leverage,” he said.
Anderson added that governmental bodies and public entities are particularly attractive targets for cyber-crime gangs and nation-state actors because of the financially lucrative or politically sensitive information they hold.
“Government minsters, civil servants and anyone else involved in the process of government need to be especially vigilant to phishing emails – which remain the most popular entry vector for ransomware - and the security measures in place need to be the most stringent available, including user training on the risks and tell-tale signs of a phishing attack and email filtration systems,” said Anderson.
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwise
The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwiseNews Billing itself as the “only place ransomware allowed", RAMP catered mainly for Russian-speaking cyber criminals
