Will triple extortion ransomware truly take off?
Operators are now launching attacks with three extortion layers, but there are limitations to this model


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
It would be ideal if ransomware hadn’t evolved since its massive surge in 2015. The sloppy craftsmanship of WannaCry, for example, made the programme fallible, and its operators owed their successes to millions of unpatched systems across the world. Patching, nowadays, is taken more seriously, and can even be automated. Just as defenders have built resistance to some attack methods, ranomware operators have equally improved their proposition; finding new ways to hack, carve, and chisel their way into anything that can reap a financial reward.
WannaCry showed the world how not to write ransomware
The rise of LockBit exemplifies this. Currently the heaviest hitter in the ransomware as a service (RaaS) game, LockBit has announced it will pivot to a triple extortion model for future attacks. This comes only shortly after the emergence of double extortion ransomware. Whether the organisation chooses to make good on this threat remains to be seen, especially given it could be construed as a stroppy retaliation to being knocked offline following the Entrust attack. Regardless, it’s a threat the industry must take seriously as it could represent the next major leap in cyber crime.
What is triple extortion ransomware?
A triple extortion model builds on the popularised double extortion method, whereby a hacker infiltrates a victim’s environment, steals data – usually of a sensitive nature – and then delivers the ransomware payload. The method was developed to combat a rise in organisations simply restoring impacted systems from backups, the industry-advised best practice for ransomware incidents.
Things become more dangerous for an organisation when its data is on the line. Sure, it could recover its systems from backups just fine, but the threat of its data leaking publically opens the victim up to regulatory punishment and reputational damage. This is especially true if the ransomware operator steals personal data, for example.
The dynamic works in the cyber criminal’s favour because it adds a layer of complexity to the incident that further incentivises the victim to pay the ransom, which it could avoid by restoring from backups. This is often deemed preferable to the fear of being sanctioned for violating GDPR or other relevant data protection laws.
Triple extortion takes this a step further by adding another layer. This can manifest in various forms; the first recorded triple extortion case, for example, was launched in 2020 against a Finnish physiotherapy provider, Vastaamo, which saw the attackers extort individual patients whose data they stole from the company. The approach not only pressured Vastaamo to pay the initial ransom but also opened the company up to reputational damage.
Cyber criminals can also pursue triple extortion through other means like how REvil, at its peak, began calling victims’ clients and tipping off the press to their, pressurising victims to pay up fast. Launching distributed denial of service (DDoS) attacks is another option. This is arguably the most aggressive tactic of them all but comes with the obvious drawback of being far more expensive to carry out. Content delivery networks (CDNs) like Cloudflare and Fastly offer effective anti-DDoS protections for businesses, too, so it can seem like overkill.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
In reality, one might argue regulators rarely issue fines to companies that have sustained a leak of data due to double extortion ransomware attacks. Unless the company showed a blatant disregard for data protection in the first place, or failed to implement stronger security measures after the fact, then leniency is applied. Ultimately, it means the double extortion threat isn’t as potent as cyber criminals might think, opening the door for strategies that pack a little more punch.
What is so concerning about triple extortion ransomware?
RELATED RESOURCE
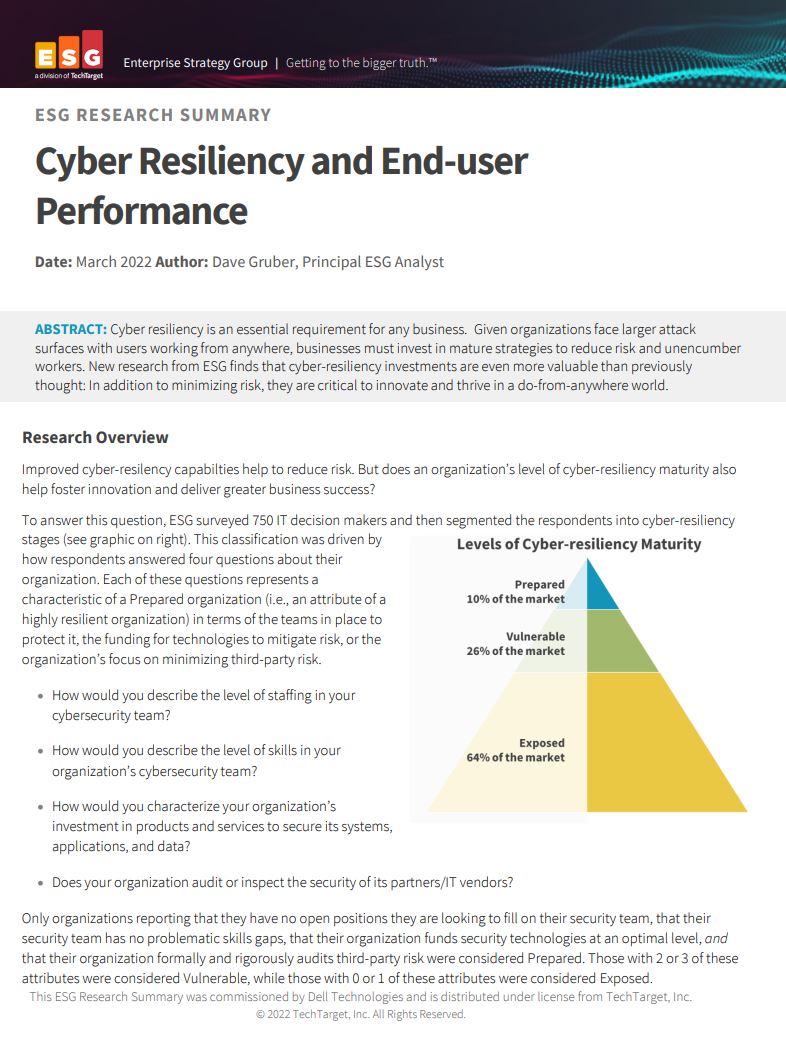
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
Aside from the added threat vector of a DDoS attack, or similar, on top of data exfiltration and file encryption, the main concern for many businesses will be the operational downtime such an attack can cause. Industries like manufacturing and healthcare regularly top the charts of the most-targeted sectors,mainly because of the severe consequences of downtime. Attacks on operation technology (OT) firms, for example, are estimated to cost up to £200,000 an hour, and healthcare organisations unable to access vital systems means patient care suffers.
Another concern is career ransomware criminals will stop at nothing to achieve their extortion ambitions. In ransomware’s infancy – when it was just encryption and extortion – businesses could counter the attack by restoring from backups, although this isn’t always totally effective. Double extortion can be mitigated, again, with backups and perhaps an empathetic response from customers. Other than paying a reputable CDN for top-tier anti-DDoS protection there’s little an organisation can do to stop a triple-layered attack.
“While threat actors finding new ways to extort victims is essentially unsurprising, triple extortion cannot be seen as the point where the threat from ransomware stops evolving either,” said Morphisec, on the trend. “Instead, all it does is warn organisations that once they breach your network, threat actors will stop at nothing to get you to pay up.”
How to defend against triple extortion ransomware attacks
Triple extortion is rarely used due to the added cost and complexity involved in deploying it alongside the ransomware strain. That said, it’s been spotted in the wild before, with REvil among the first to champion the technique. LockBit, too, is committing to it, meaning the potential for triple extortion ransomware to cause significant damage is real.
Successful attacks will likely only be carried out by the most well-equipped ransomware gangs and those with the time, personnel, and cash to meet those resource demands. There are, however, few ransomware outfits capable or willing to go to such lengths, or it would have already been far more popular than it is.
There’s a wider shift at play, too. Ransomware, experts tell IT Pro, is simply the tool used to facilitate the core crime of financial extortion. Be it double or triple extortion ransomware – or if ransomware eventually dies off – financial extortion is here to stay, and the threat businesses should focus on defending against.
“I don’t often make the distinction between double and triple extortion ransomware,” says Charl van der Walt, head of security research at Orange Cyberdefense. “Ransomware, extortion, double extortion, triple extortion – it's incidental to the crime. It'll always continue to evolve as long as the other key elements remain in place.
RELATED RESOURCE

Cyber security in the retail sector
Retailers need to ensure their business operations and internal data aren't breached
Extortion relies on a criminal taking something of value that can be used to extort a victim, he continues, but there are ways of devaluing what a criminal can steal from a business. Making backups of data means victims can decrease the value of the stolen files in a multi-layered extortion attack, but this alone won’t stop the crime.
Criminals will continue to adapt the form of extortion while a host of factors remain in play, says van der Walt. These include the existence of potential victims, there being an easy way to move the paid ransom money out, and the persistence of a robust criminal ecosystem that acts with impunity. Ultimately, you could argue extortion works because the current legislative and regulatory landscape allows it to. Cyber criminals largely act, as van der Walt says, with impunity and without legal or regulatory intervention. So long as this persists, it’s likely cyber extortion will persist.
“So far, we're just seeing slight evolutions in those [extortion] mechanisms – from encrypt, to encrypt and leak, to encrypt and leak and DDoS,” he continues. “I predict somewhere along the line, someone will start coming up with novel forms that we haven't seen before, and I don't know what those are yet.”

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Why storage really matters in an AI-centric world
Why storage really matters in an AI-centric worldDell PowerScale provides the performance and scalability to help enterprises build storage infrastructure for AI
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwise
The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwiseNews Billing itself as the “only place ransomware allowed", RAMP catered mainly for Russian-speaking cyber criminals