Keylogger discovered in hundreds of HP laptops
HP patches touchpad driver, but hackers could exploit flaw to spy on users
More than 450 HP laptop models have a keylogger hidden away in a driver, forcing HP to issue patches for the affected devices.
The keylogger, found in Synaptics' touchpad software, is disabled by default, but hackers could potentially enable it if they had access to a computer by elevating user privileges, said Michael Myng, the researcher who discovered the flaw.
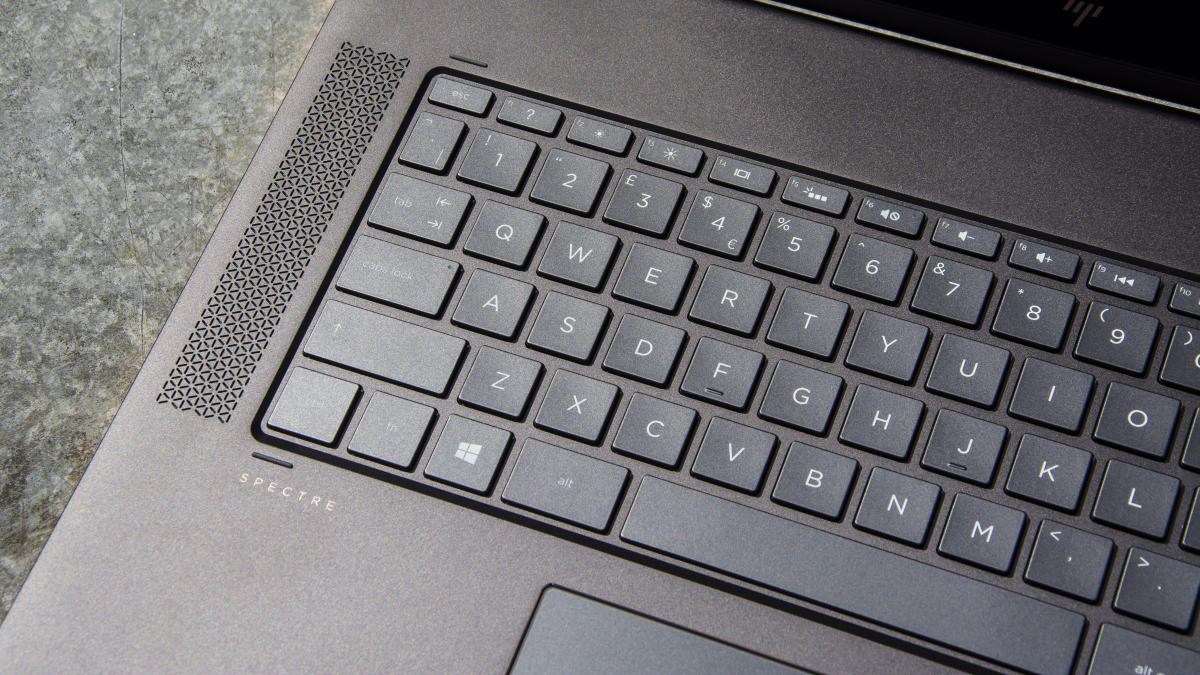
Commericial workstations, consumer laptops and other HP products contain the flaw, including Spectre devices, Pavilion devices, ZBooks and others.
"A potential security vulnerability has been identified with certain versions of Synaptics touchpad drivers that impacts all Synaptics OEM partners," an HP statement on its security bulletin read.
"A party would need administrative privileges in order to take advantage of the vulnerability. Neither Synaptics nor HP has access to customer data as a result of this issue."
Myng discovered the issue when trying to control the backlighting of an HP keyboard, noticing a format string for a keylogger when looking through the keyboard driver. Unable to find an HP laptop to test his findings, he contacted HP directly.
"They replied terrificly [sic] fast, confirmed the presence of the keylogger (which actually was a debug trace) and released an update that removes the trace," he said.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
HP claims the keylogger in Synaptics' touchpad was created to debug errors. If activated however, a hacker could track every letter a laptop user typed.
Worth updating with a quick line - they say sorry and working on updating drivers with a patch, don't give people admin access in the meantime
A Synaptics spokesperson apologised for the error and advised users to change their admin settings to prevent anyone taking advantage of the flaw before it's fixed.
"Synaptics is working closely with our PC customers to update drivers and to deploy them to address security concerns," they said. "Synaptics also recommends using best practices by restricting admin access to any system as anyone with this level of access can potentially install malware or other anti-privacy software irrespective of whether the debug tool is on or off."
They added: "In our new normal of heightened concern for security and privacy, Synaptics would like to apologise for any concerns that our debug tool may have raised. We have a path to immediately address this issue and other security concerns should they arise."
A keylogger was also discovered in Synaptics subsidiary Conexant's audio drivers, also installed in HP laptops, back in May.
An HP spokesperson said: "HP was advised of an issue that exists with Synaptics' touchpad drivers that impacts all Synaptics OEM partners. HP uses Synaptics' touchpads in some of its mobile PCs and has worked with Synaptics to provide fixes to their error for impacted HP systems, available in the security bulletin on HP.com. HP has no access to customer data as a result of this issue."
Picture: HP Spectre x360/Credit: IT Pro
-
 Kaseya shifts from AI ‘insights’ to autonomous action with new agentic platform
Kaseya shifts from AI ‘insights’ to autonomous action with new agentic platformNews The company aims to evolve from its suite of management tools into an autonomous operating system for MSPs
-
 Accenture to roll-out Copilot to 700,000+ staff
Accenture to roll-out Copilot to 700,000+ staffNews Accenture will roll out Microsoft Copilot to nearly three quarters of a million employees after years of testing
-
 Brace yourselves for a vulnerability explosion, Forescout warns
Brace yourselves for a vulnerability explosion, Forescout warnsNews AI advances are helping identify software flaws at record pace and scale, but that's not the good news some would think
-
 ‘It’s not a good look for the PC ecosystem as a whole.” HP to make fix for TPM vulnerability an industry standard
‘It’s not a good look for the PC ecosystem as a whole.” HP to make fix for TPM vulnerability an industry standardJust announced TPM Guard offers important protection against device data theft when attackers gain physical access
-
 Ubuntu vulnerability exposes enterprises to root escalation, complete system compromise
Ubuntu vulnerability exposes enterprises to root escalation, complete system compromiseNews The high-severity Ubuntu vulnerability allows an unprivileged local attacker to escalate privileges through the interaction of two standard system components
-
 DIY hackers are turning to ‘flat-pack’ malware components to speed up attacks and cut costs
DIY hackers are turning to ‘flat-pack’ malware components to speed up attacks and cut costsNews While these malware campaigns are very basic, researchers noted “they still work”
-
 Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerability
Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerabilityNews Threat actors have been exploiting the vulnerability to achieve root access since 2023
-
 Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourself
Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourselfNews The VS Code vulnerabilities highlight broader IDE security risks, said OX Security
-
 CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaught
CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaughtNews While the CVE figures might be daunting, they won't all be relevant to your organization
-
 Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to know
Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to knowNews Patch Tuesday update targets large number of vulnerabilities already being used by attackers