Swyx SwyxExpress X20 review
Voice over IP systems can save money and reduce support hassles for time-starved system administrators. Unless it's a Swyx VoIP system, as Andrew Webb and Kat Orphanides discovered in our review.
SwyxExpress was extremely complex to configure, vastly overpriced for what it was, and not very good. It's billed as simple to configure, yet even a veteran sysadmin with both Windows and VoIP system experience would struggle with this device. There are many alternatives out there that are easier to configure and are better value.

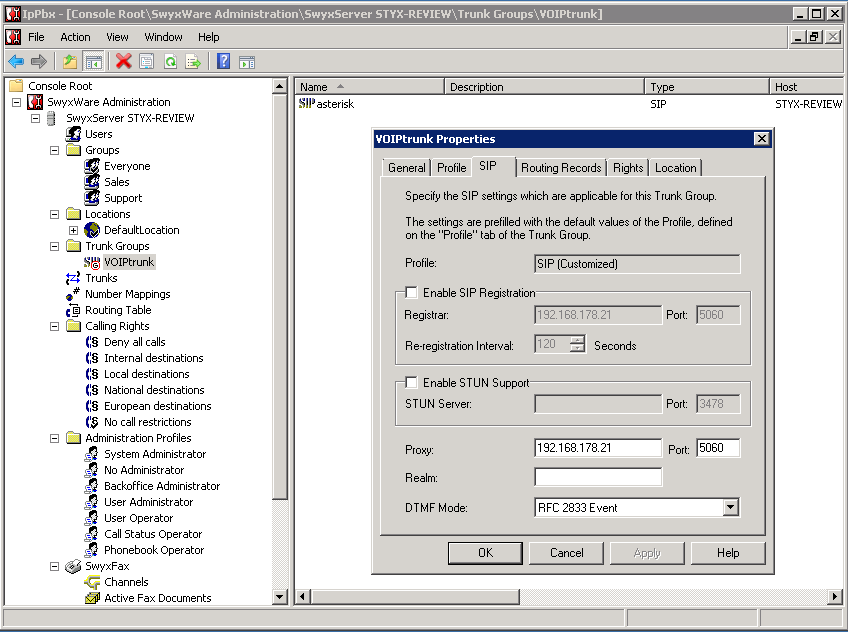
Configuring a trunk group.
Both SwyxWare and the Asterisk server providing the service showed the trunk as down. We eventually traced the problem to the fact that our remote Asterisk server was connected via a VPN which had been set up and started after the Swyx software was already installed. Because of this, Swyx was not listening on the IP address allocated to our VPN, and so couldn't communicate via the VPN.
To get round this issue, we switched to a local Asterisk server, set up with the same test account, and re-configured SwyxWare accordingly. However the trunk failed to register with the account, and was unable to place calls until the Asterisk server was configured to authenticate the incoming connection by source address instead of by SIP registration. This got the trunk working, but only if the Swyx configuration was set to register the SIP connection with the outgoing server. If that option was de-selected, as would be normal with this form of authentication, then the trunk failed again. Trusted source address authentication of this sort is secure and stable, but requires the source to have a static IP address. This won't be an issue for most small businesses, but is worth bearing in mind.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
-
 Salesforce ramps up agentic AI research with new foundry project
Salesforce ramps up agentic AI research with new foundry projectNews Researchers are already working on new tools for agent-to-agent interaction and “ambient intelligence”
By Ross Kelly Published
-
 Google just revised its ‘Q-Day’ timeline: Quantum computers could break existing encryption techniques within three years – and enterprises are nowhere near ready
Google just revised its ‘Q-Day’ timeline: Quantum computers could break existing encryption techniques within three years – and enterprises are nowhere near readyNews Google has warned that “Q-Day”, the point where a quantum computer is powerful enough to crack current encryption techniques, could come as soon as 2029.
By Emma Woollacott Published
-
 Red Hat, Google Cloud eye legacy modernization gains with partnership expansion
Red Hat, Google Cloud eye legacy modernization gains with partnership expansionNews Red Hat wants to make it easier to migrate and modernize applications
By Nicole Kobie Published