Tresorit Business review: Super-secure shared storage
An emphasis on security makes this cloud service perfect for anyone handling sensitive data

Tresorit may not be able to match the collaboration features of its competitors but it beats them hands-down for security. Its zero-knowledge encryption makes it very easy to deploy and use, the desktop apps are well designed and Tresorit’s Business plan is an affordable option for SMEs.
-
+
Fantastic security and access controls
-
+
Policy-based sharing rules
-
+
Great platform support
-
+
Simple deployment
-
-
Limited collaboration features

Swiss cloud specialist Tresorit takes data privacy and security very seriously. Its file storage and sharing solution encrypts everything at the client, in transit and on its cloud servers - and the company has a strict zero-knowledge policy, which means it has no access to the encryption keys that protect your company's data.
Tresorit's entry-level Small Business plan starts at just two users. It costs £12 per user (if you pay yearly), and each team member gets 1TB of cloud storage, along with file sharing, syncing, collaboration and Outlook integration. We tested the Business plan, which starts at ten users: this includes the same storage allocation, but adds extras such as custom portal branding, access-tracking logs, Active Directory support, remote erasure for mobile devices and password recovery. It's a decent deal at its regular price of £16 per user - and right now it's on offer at half price.
Larger businesses with 100 users or more might want to consider the Enterprise plan instead, which includes a data residency service that allows you to choose from eight global data centres - although this can also be added to the Business plan at an additional cost.
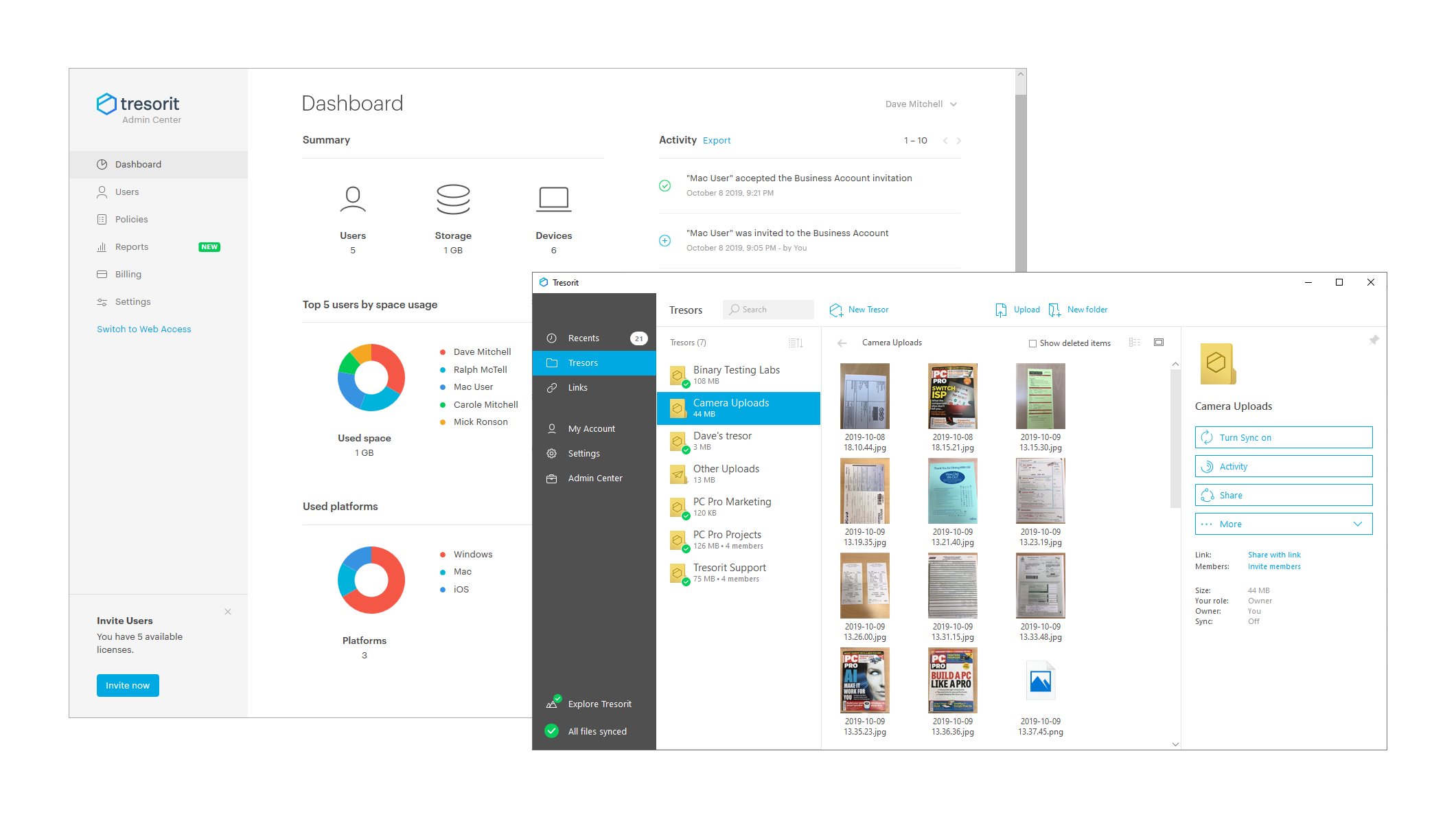
Tresorit's Admin Center cloud portal opens with a dashboard showing a summary of users, storage usage and devices, along with graphs of the top five users and platforms. From the portal, you can also configure various security policies, including two-factor authentication, login timeouts and expiration times on file-sharing links, as well as blocking web browsers from storing login credentials.
Adding users is simple: as usual, you can send invitations by email directly from the admin portal, which include a download link for the Tresorit client app. Users can access their account from Windows, Mac, Linux, mobile devices or the web portal, although for enhanced security you can restrict them to specific platforms - or block local syncing altogether, so that they can only access their files in the cloud.
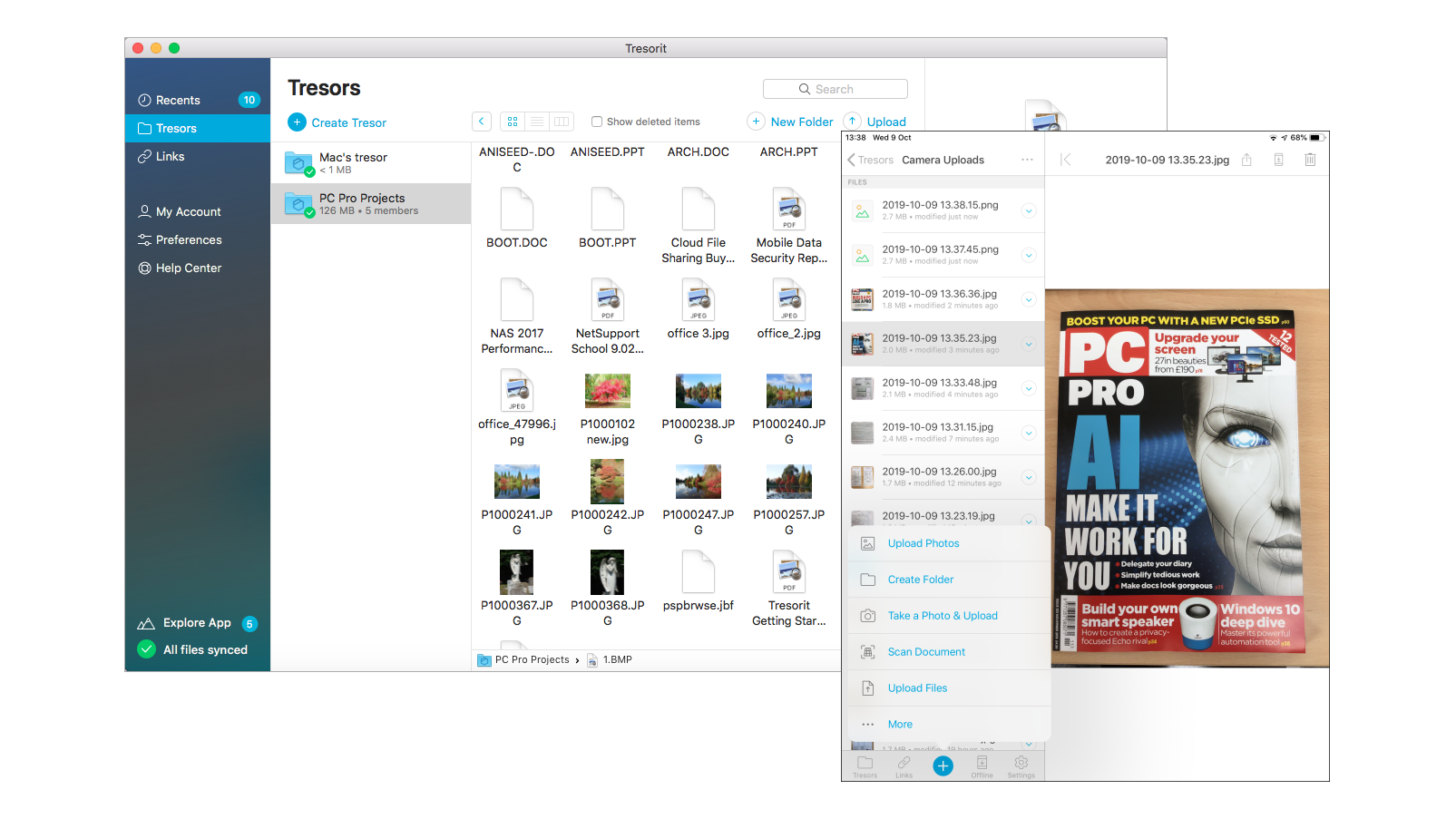
We tried out the client on both Windows 10 and macOS systems and had no problems. Installation on the Mac is particularly nicely handled: the DMG package is placed conveniently in the Applications folder and installed with two mouse clicks.
When you first open the desktop app, your first personal "Tresor" is automatically created - that being the company's moniker for a secure encrypted folder. Users can create as many additional Tresors as they wish, and policies determine who they can share them with.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The sharing process itself is easy: users simply select team members from their contact list, and choose whether they want them to have manager, editor or viewer access. If permitted, users can also generate links to share files with third parties that don't have a Tresorit account. A lot of thought has clearly gone into the security side of this: sharers can set a link expiry date and download limit, as well as enforcing password protection and requiring the recipient to verify their email address.
Another neat feature is the new editing badge, which indicates when shared documents are being edited. If a team member tries to access a file while someone else is working on it, they will get a warning.
The iOS and Android mobile apps add a useful document-scanning function. We used this on our iPad to take snaps of documents and save them as PDFs, which were then promptly encrypted and sent directly to our cloud account in a single action.
Other cloud file-sharing solutions offer more extensive collaboration tools, but if security is a priority then Tresorit is an excellent choice. It's easy to deploy and manage, it offers first-rate access controls and right now the Business plan is particularly good value.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.
-
 Dell PowerStore Elite unveiled at Dell Technologies World 2026
Dell PowerStore Elite unveiled at Dell Technologies World 2026News The new platform is described as "the biggest leap forward" in PowerStore's history
By Jane McCallion Published
-
 British public deeply fearful of AI – with one-in-five even thinking it will lead to civil unrest
British public deeply fearful of AI – with one-in-five even thinking it will lead to civil unrestNews Research by King's College London suggests people think AI's impact will be worse than a normal recession
By Emma Woollacott Published
-
 What makes a successful AI scale-up?
What makes a successful AI scale-up?News Barclays Eagle Labs lists its top 100, and finds the UK in a very promising place
By Emma Woollacott Published

