Report: Regulatory and monetary incentives needed to adopt safer programming languages
Companies have been urged to create plans on how they intend to get rid of memory-unsafe code in their products


A new report recommends using regulatory and monetary incentives to encourage the adoption of safer programming languages to build more cyber-secure software.
Estimates made in research carried out by Consumer Reports contended that around 60-70% of browser and kernel vulnerabilities are discovered in codebases largely comprised of C and C++ code - two languages known for poor memory safety.
One of the report's chief conclusions was that monetary or regulatory incentives could be needed to convince an industry notoriously reliant on older, less memory-safe languages to make the switch to newer languages such as Go, Ruby, and Rust.
Both the private and public sectors could also benefit from enacting policies that promote the creation of memory-safe code, the report suggested.
"As much as possible, companies, government organisations, and other entities should commit to using memory-safe languages for new products and tools and newly developed custom components," the report read.
There are numerous barriers to adoption when it comes to memory-safe languages. Government agencies, for example, can't just purchase memory-safe solutions out of the box, the report noted, so the issue also requires strong advocacy from engineers to move towards memory safety as a priority.
"The carrot approach for memory safety may include not just decreased future costs in cyber security, but also reliability and efficiency. Ideally, memory safety will be viewed as a proxy for funded, competent risk management strategy and for software that's currently evolving and malleable."
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Such a transition is likely to take substantial amounts of time given the inherent complexity of rewriting large codebases in newer languages with different functionalities and performance levels, the researchers noted.
Other suggested steps forward the report made included: asking engineers to list memory safety mitigations as part of a software's feature set; training development teams on how to program memory-safe code; and developing public awareness campaigns.
"Languages such as C and C++, which are older than more modern programming languages, lack memory management being built-in," said Eleanor Watson, IEEE fellow, machine intelligence researcher, and AI singularity expert to IT Pro.
"Competent coding of an embedded system with limited updates may be reasonably safe, especially if combined with tools for the formal verification of the system and its functionality. Personally, I feel that the phase-out of memory unsafe programming in applications makes sense, but that there should be different rules for embedded systems which are bounded in a limited range of activity and which require high performance."
What is memory safety?
The US' National Security Agency (NSA) has been vocal on the topic of memory-safe programming languages recently.
In November 2022, it made a public call to move away from languages like C and C++ due to the proportion of exploitable security vulnerabilities being attributed to sub-optimal handling of memory in software.
As yet, the NSA's stance hasn't been enacted in the form of regulation or legislation, but as calls grow for a transition towards safer languages, the report's suggestions could feasibly become reality.
Use-after-free and out-of-bounds read/write bugs are among the most common affecting systems presently and both would be automatically ended by using memory-safe languages, rather than having to rely on a developer to code the necessary safeguards.
"While developers using memory-unsafe languages can attempt to avoid all the pitfalls of these languages, this is a losing battle, as experience has shown that individual expertise is no match for a systemic problem," the report read.
"Even when organisations put significant effort and resources into detecting, fixing, and mitigating this class of bugs, memory unsafety continues to represent the majority of high-severity security vulnerabilities and stability issues.
"It is important to work not only on improving detection of memory bugs but to ramp up efforts to prevent them in the first place."
Barriers to adoption
A number of barriers exist when it comes to transitioning away from older, memory-unsafe languages. The report suggested it all starts with education and the professors in charge of some computer science courses displaying reluctance to transition from C and C++.
"Professors have a golden opportunity here to explain the dangers of C and similar languages, and possibly increase the weight of memory safety mistakes on exercise grading, which proliferate in student-written code just as they do outside of the classroom.
"Another opportunity is to switch languages for part of those courses."
RELATED RESOURCE
The Total Economic Impact™ Of IBM FlashSystem
Cost savings and business benefits enabled by FlashSystem
The researchers conceded that teaching in languages such as Rust could lead to "inessential complexity", so a balance needs to be struck between teaching languages that have real-world value while raising awareness of their dangers and possible alternatives.
This reluctance for change is also replicated in the executive levels of a company where management might not trust new languages or their ability to maintain the same functionality.
“Perhaps the tools are workable but there is the sense that C/C++ equivalents are more reliable or easier to use,” read the report.
There are also inherent challenges when it comes to actually rewriting large and complex codebases in new languages.
Considerations when embarking on such a change include balancing tradeoffs between cost of implementation, runtime performance, toolchain complexity, and overall safety. In some scenarios, factors such as runtime performance may outweigh safety in some organisations, for example.
Zach Marzouk is a former ITPro, CloudPro, and ChannelPro staff writer, covering topics like security, privacy, worker rights, and startups, primarily in the Asia Pacific and the US regions. Zach joined ITPro in 2017 where he was introduced to the world of B2B technology as a junior staff writer, before he returned to Argentina in 2018, working in communications and as a copywriter. In 2021, he made his way back to ITPro as a staff writer during the pandemic, before joining the world of freelance in 2022.
-
 Anthropic says Claude Code can help streamline 'cost-prohibitive' COBOL modernization, but IBM says it's not that simple – 'decades of hardware-software integration cannot be replicated by moving code'
Anthropic says Claude Code can help streamline 'cost-prohibitive' COBOL modernization, but IBM says it's not that simple – 'decades of hardware-software integration cannot be replicated by moving code'News Research from Anthropic claims Claude Code can simplify modernization of COBOL systems
-
 ‘1 engineer, 1 month, 1 million lines of code’: Microsoft wants to replace C and C++ code with Rust by 2030 – but a senior engineer insists the company has no plans on using AI to rewrite Windows source code
‘1 engineer, 1 month, 1 million lines of code’: Microsoft wants to replace C and C++ code with Rust by 2030 – but a senior engineer insists the company has no plans on using AI to rewrite Windows source codeNews Windows won’t be rewritten in Rust using AI, according to a senior Microsoft engineer, but the company still has bold plans for embracing the popular programming language
-
 Using an older version of Python? You’re leaving ‘money and performance on the table’ if you don’t upgrade – and missing out on big developer efficiency gains
Using an older version of Python? You’re leaving ‘money and performance on the table’ if you don’t upgrade – and missing out on big developer efficiency gainsNews New research from JetBrains shows a majority of enterprises are using a version of Python that’s a year or more older – and it's having a big impact on efficiency and performance.
-
 ‘It’s far from showing its age’: Java might’ve just turned 30, but it’s still going strong and here to stay
‘It’s far from showing its age’: Java might’ve just turned 30, but it’s still going strong and here to stayNews With Java celebrating its 30th anniversary, we look at the rise of the programming language and what the future holds.
-
 Python’s popularity shows no signs of fading – here’s why software developers love it
Python’s popularity shows no signs of fading – here’s why software developers love itNews Python remains highly popular among developers for a number of key reasons, experts told ITPro.
-
 Oracle Java pricing concerns could spark a developer exodus
Oracle Java pricing concerns could spark a developer exodusNews Oracle Java users have raised concerns over pricing, with many considering switching to open source options.
-
 Python just brushed past JavaScript to become the most popular programming language on GitHub – and a key factor is that AI developers love it
Python just brushed past JavaScript to become the most popular programming language on GitHub – and a key factor is that AI developers love itNews The meteoric rise of Python shows no sign of stopping
-
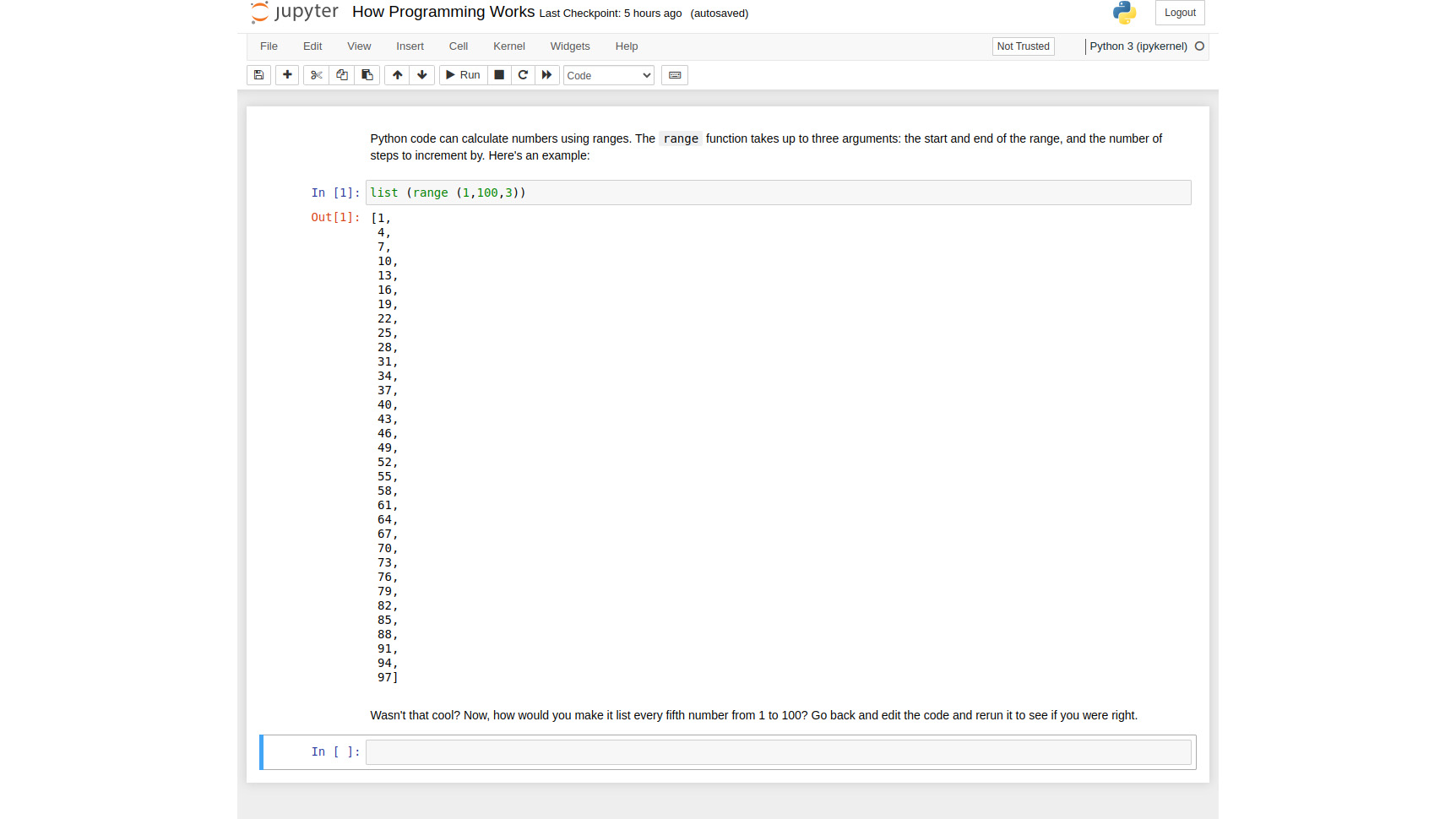 JupyterLab review: A powerful tool for documenting your data science journey
JupyterLab review: A powerful tool for documenting your data science journeyReviews Literate programming toolkit takes dynamic code documents to new heights


