Flappy Bird clone hacking plans revealed
The hack was planned by the same group who stole photos of celebrities from iCloud

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
A group of hackers who stole naked photos of more than 100 female celebrities planned to carry out another attack using a cloned version of Android game Flappy Bird.
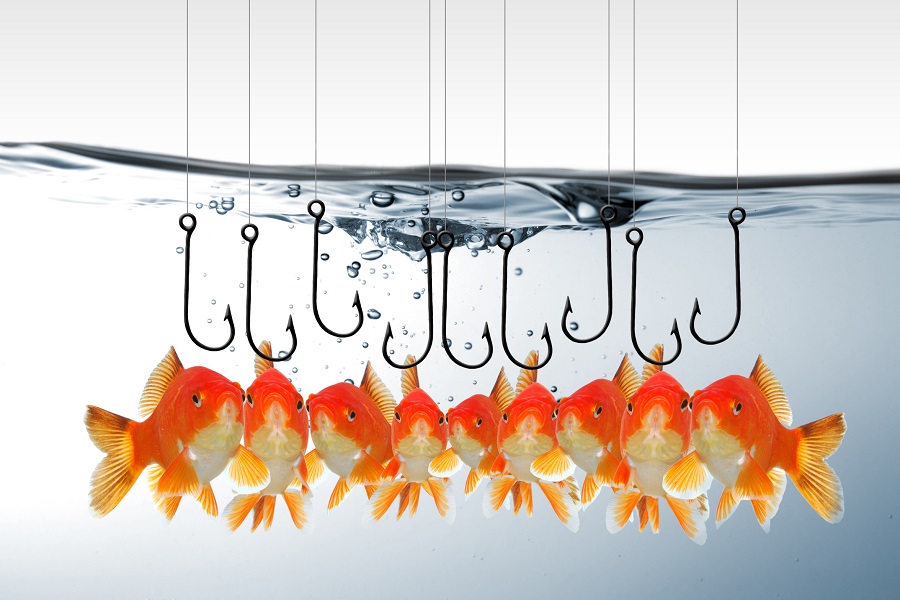
The clone included malware that could be used to maliciously gather photos of users and send them to a remote location for distribution in the same way they managed to leak pictures from celebrities' iCloud accounts last week.
The hackers thought they would be able to take advantage of users automatically accepting the permissions when they install an app from the Play Store.
The ring also thought it would be able to download the pictures before Google noticed and blocked the app.
The plans were revealed on image board AnonIB, part of 4chan, where the celebrity photos were being offered for sale.
A security researcher discovered the post on the leak site in July, which boasts a user only needs to use the app once to get the photos.
However, it seems as though the poster was a little concerned about getting their existing developer account blocked. After explaining what he hoped to do, they said: "It's a violation of a google play developers license to publish sneaky apps like that, and I REFUSE to risk my license over it.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
"...If any kind anons want to help me get the thing paid for, I will post any wins obtained in this thread. I will link the app's store entry here, you get girls to download and play it ONCE, and you'll get all the win you wanted, if it was there," the post said.
In July, it was revealed a new remote access Trojan malware could be used to hack and target mobile banking data, SMS messages and contact lists on Android phones.
Although there's no evidence to suggest it could steal photos, it is able to install malicious app updates, steal and send SMS messages.

Clare is the founder of Blue Cactus Digital, a digital marketing company that helps ethical and sustainability-focused businesses grow their customer base.
Prior to becoming a marketer, Clare was a journalist, working at a range of mobile device-focused outlets including Know Your Mobile before moving into freelance life.
As a freelance writer, she drew on her expertise in mobility to write features and guides for ITPro, as well as regularly writing news stories on a wide range of topics.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 iCloud hack: could phishing scheme have been behind nude celebrity photo leak?
iCloud hack: could phishing scheme have been behind nude celebrity photo leak?News Pennsylvania man pleads guilty to accessing hundreds of accounts
-
 Reddit vows to take down revenge porn posts
Reddit vows to take down revenge porn postsNews Social forum will pull nude pictures if victims say they were posted without consent
-
 Bogus iCloud log-in page fools Chinese Apple users
Bogus iCloud log-in page fools Chinese Apple usersNews Probably not looking for nude celebs this time
-
 Google threatened with legal action over naked celeb photos
Google threatened with legal action over naked celeb photosNews The company didn't react fast enough to take the pictures down, according to lawyer
-
 Lessons the enterprise can learn from the iCloud photo leak
Lessons the enterprise can learn from the iCloud photo leakIn-depth iCloud security isn't the problem, argues Davey Winder. Lack of knowledge about how to implement it is
-
 Apple denies iCloud hack resulted in leaked celebrity photos
Apple denies iCloud hack resulted in leaked celebrity photosNews iPhone maker responds to reports an iCloud hack led to the leaking of private celebrity pictures online
-
 iPhone & iPad users held to ransom by Apple ID hackers
iPhone & iPad users held to ransom by Apple ID hackersNews Hackers demand $100 to unlock devices they've seized, but Apple denies iCloud hack is to blame
-
 Amazon and Apple users told to wipe credit card data in wake of iCloud hack
Amazon and Apple users told to wipe credit card data in wake of iCloud hackNews Varonis warns end users to step up their credit card security following Mat Honan's password hack.