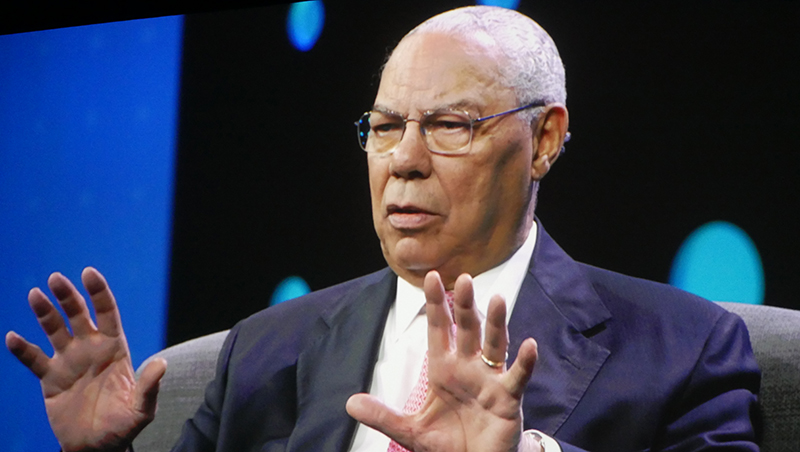
Why Colin Powell no longer trusts email
Former US secretary of state was hacked, despite two-factor authentication

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
Email is an unsecure platform that's impossible to properly protect currently, former US secretary of state Colin Powell has claimed.
The US army general, who served under four presidents, including as secretary of state under the George W Bush administration, used his keynote speech at Citrix Synergy 21017 to admit to having had his emails hacked twice.
"I've been hacked twice and both times ... I've had double factor authentication, I've had all kinds of barriers in the way and they still got in and the forensics guys can't find out why," he told delegates. "So I had to change my lifestyle and go to fax machines, go to texts that are encrypted and use email strictly for housekeeping things.
"They keep giving me new things to do with my emails to protect it, but I no longer have confidence in being able to protect it." Powell didn't say when these hacks occurred nor how successful they were.
Indeed, fax has been the communication method of choice for Powell throughout his career, as he feels it's more secure.
As chairman of the joint chiefs of staff in 1991, he was responsible for the initiation and oversight of Operation Desert Storm. Speaking about when he gave the order to commence the conflict, he said: "We had one of the most perfectly secure means of doing it. Not something you might think of now, but it was the fax machine.
"I had a fax machine in my office, my executive assistant ran it, [my counterpart in the Gulf] had a fax machine in his office and his executive assistant ran it. And by using that secure, covered fax machine I knew that the order only went from one person to one person. It wasn't a cable that could spread around all over the organisation."
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Powell also spoke of the importance of being reasonable and rational when it comes to organisations deciding what information should be kept secret and what should be treated more openly lest it prevent people from doing their jobs.
"One of the challenges we're all facing now [that] I faced when I became secretary of state, is how to make sure you have ... [a] system that is getting [information] to where it has to be when it's needed in order to be actionable," Powell said.
He said it's important to "triage" information treating as secret only the things that need to be secret.
"[You have to] make sure you're not cluttering the whole system by over-classifying things and by making sure that you have a system that will make that differentiation," he said.
Main image credit: Jane McCallion/IT Pro

Jane McCallion is Managing Editor of ITPro and ChannelPro, specializing in data centers, enterprise IT infrastructure, and cybersecurity. Before becoming Managing Editor, she held the role of Deputy Editor and, prior to that, Features Editor, managing a pool of freelance and internal writers, while continuing to specialize in enterprise IT infrastructure, and business strategy.
Prior to joining ITPro, Jane was a freelance business journalist writing as both Jane McCallion and Jane Bordenave for titles such as European CEO, World Finance, and Business Excellence Magazine.
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation