Digital Shadows’ context-based security alerts expand sensitive doc management
New alerts will be part of SearchLight, Digital Shadows’ risk-detection platform

Today, Digital Shadows announced upgraded capabilities for its digital risk-protection platform, SearchLight, to help organizations protect sensitive data from unauthorized access and manipulation.
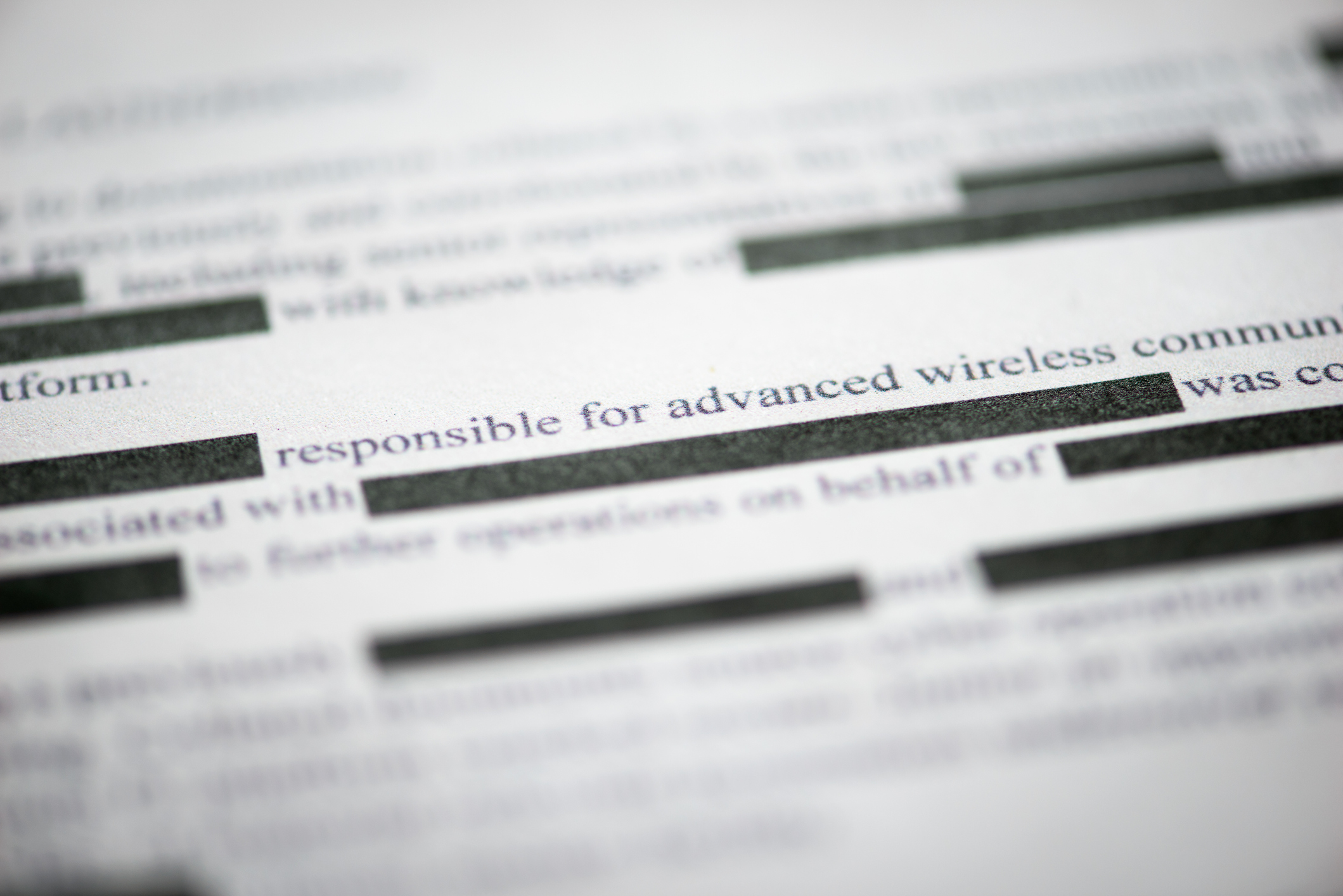
SearchLight already alerts customers about potential sensitive document exposure before they become emergencies. SearchLight currently categorizes documents noted as “sensitive” because they include password-protection, encryption or words similar to “Private and confidential.” These documents may consist of company tax documents, payroll information and proprietary product designs.
According to the press release, starting December 1, SearchLight will gain two new alerts: exposed technical documents (security assessments and product designs) and commercial documents (legal and payroll data). Plus, these documents won’t require protective markings to be identified as sensitive and associated with their organizations, thanks to new contextual analysis.
The ability to consider a document’s context will also help customers understand an alert’s severity. In the case of a leaked technical document, the alert will indicate the compromised file is a product-related document and assign it a visible risk-prioritization score. Because a leaked technical document is extremely sensitive, it will attract a high-risk prioritization score.
Additional context within the alert will include when someone last viewed the document and if it’s still online. Clients can also use domain information and file metadata to identify the original misconfigured file store’s author and creation date.
"Every day more product designs, security assessments, and payroll data are exposed online – and organizations have no idea. We give them new visibility into this problem and provide the best ways to mitigate the risks," said Russell Bentley, VP of product at Digital Shadows.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
-
 Dell PowerRack launches at Dell Technologies World 2026 as a ‘turnkey’ networking, storage, and compute system for AI
Dell PowerRack launches at Dell Technologies World 2026 as a ‘turnkey’ networking, storage, and compute system for AIThe newly announced solution is designed to help organizations get up and running at super speed
-
 Dell unveils Deskside Agentic AI at Dell Technologies World 2026
Dell unveils Deskside Agentic AI at Dell Technologies World 2026News Deskside Agentic AI is the latest in the Dell AI Factory with Nvidia stable, with the company saying it further demonstrates its end-to-end enterprise AI capability
-
 Only ever use black bars to redact text, warns security researcher
Only ever use black bars to redact text, warns security researcherNews Researcher Dan Petro shows how pixelation can be easily reversed using algorithms
-
 Hackers fake DocuSign and offer fraudulent signing methods
Hackers fake DocuSign and offer fraudulent signing methodsNews Criminals impersonate the e-signing company to steal credentials
