CISA issues fresh orders to polish security vulnerability detection in federal agencies
The move marks the latest step in the cyber security authority's ongoing ambition to minimise the government's exposure to attacks

The US Cybersecurity and Infrastructure Security Agency (CISA) has released a Binding Operational Directive (BOD) aimed at improving Federal Civilian Executive Branch (FCEB) agencies’ awareness of security vulnerabilities that may reside in their IT estates.
The BOD details its goals for building a sophisticated cyber defense in federal information systems. The guidelines further the US' sustained efforts in limiting federal agencies’ exposure to cyber attacks.
A catalog of Known Exploited Vulnerabilities (KEVs) that CISA began compiling back in November 2021 has been consistently updated and mandates FCEB agencies patch against a list of the most-exploited security vulnerabilities.
RELATED RESOURCE
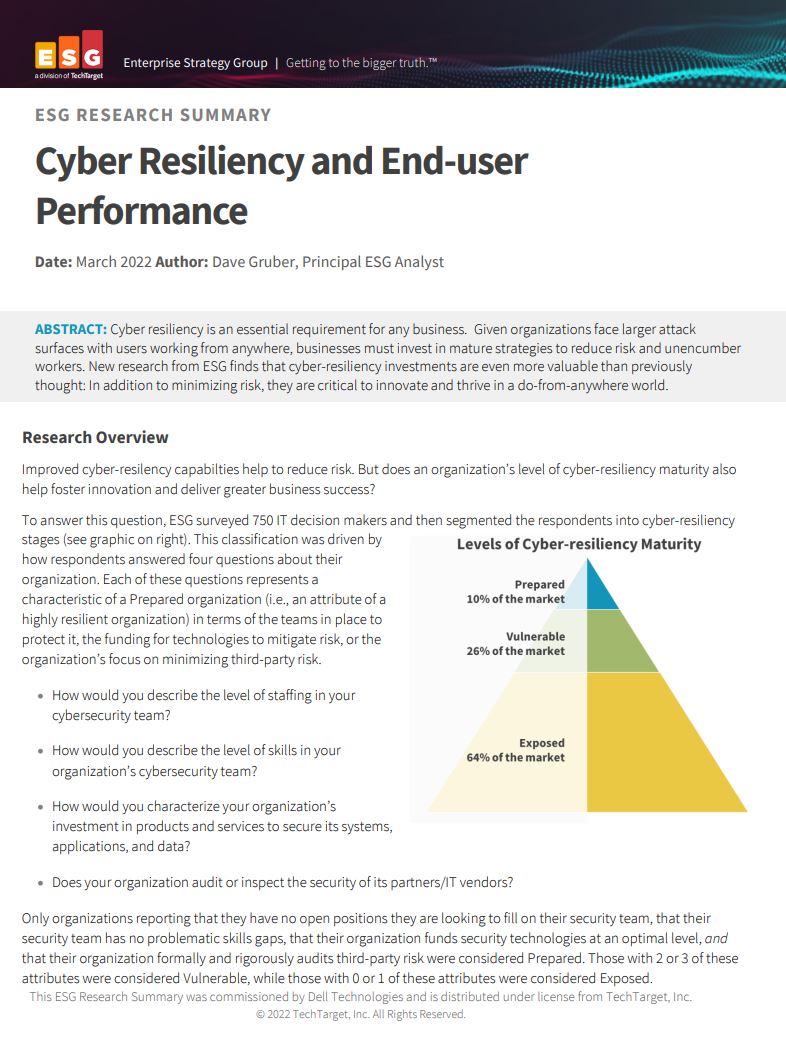
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
“Continuous and comprehensive asset visibility is a basic pre-condition for any organization to effectively manage cybersecurity risk,” the agency said in a public-facing notice.
“Accurate and up-to-date accounting of assets residing on federal networks is also critical for CISA to effectively manage cyber security for the FCEB enterprise.”
By April 3 2023, CISA will require all FCEB agencies to adhere to a number of mandatory cyber security practises such as initiating automated asset discovery every seven days, performing vulnerability enumeration across all discovered assets every 14 days, and uploading vulnerability enumeration results into the continuous diagnostics and mitigation (CDM) agency dashboard within 72 hours of discovery.
Agencies will also be required to initiate on-demand asset discovery and vulnerability enumeration within 72 hours of receiving a CISA request, providing available results within seven days.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The requirements do not apply to statutory national security systems, including certain systems operated by the Department of Defense or the intelligence community.
Per the White House cyber security executive order, federal agencies and CISA will deploy an updated CDM dashboard configuration that will enable analysts to access object-level vulnerability enumeration data by April 3 2023.
Underscoring CISA’s actions, the BOD stated that “within six months of issuance, the agency will publish data requirements for agencies to provide machine-level vulnerability enumeration performance data in a common data schema.”
FCEB agencies will be required to make a progress report at six, 12, and 18-month intervals detailing any dependencies that may prevent them from meeting the Directive's requirements.
-
 nLighten eyes fresh growth under new CEO and CFO
nLighten eyes fresh growth under new CEO and CFONews Dame Dawn Childs and Matthew Harris join the data center provider’s executive team as it looks to meet growing edge infrastructure demand
-
 Managing tech costs in a volatile market
Managing tech costs in a volatile marketITPro Podcast Rising energy prices and sprawling cloud environments make the jobs of CIOs and CFOs harder than ever
-
 Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expect
Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expectNews The Claude Mythos developer is aiming for a more limited approach to cyber tooling for public consumption
-
 Researchers warn millions of RDP and VNC servers are wide open to exploitation
Researchers warn millions of RDP and VNC servers are wide open to exploitationNews Researchers at Forescout spotted millions of RDP and VNC servers exposed online
-
 Brace yourselves for a vulnerability explosion, Forescout warns
Brace yourselves for a vulnerability explosion, Forescout warnsNews AI advances are helping identify software flaws at record pace and scale, but that's not the good news some would think
-
 Ubuntu vulnerability exposes enterprises to root escalation, complete system compromise
Ubuntu vulnerability exposes enterprises to root escalation, complete system compromiseNews The high-severity Ubuntu vulnerability allows an unprivileged local attacker to escalate privileges through the interaction of two standard system components
-
 Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerability
Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerabilityNews Threat actors have been exploiting the vulnerability to achieve root access since 2023
-
 Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourself
Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourselfNews The VS Code vulnerabilities highlight broader IDE security risks, said OX Security
-
 CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaught
CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaughtNews While the CVE figures might be daunting, they won't all be relevant to your organization
-
 Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to know
Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to knowNews Patch Tuesday update targets large number of vulnerabilities already being used by attackers
