Warning issued over ransomware attacks targeting VMware ESXi servers globally
Businesses have been urged to patch the two-year-old vulnerability amidst heightened ransomware threats


Hundreds of organisations worldwide have been targeted by a hacking campaign exploiting VMware’s ESXi servers to deploy the new ESXiArgs ransomware variant.
French and Italian cyber security agencies issued an urgent warning last week after attackers were found to be actively targeting servers left unpatched against a two-year-old remote code execution (RCE) vulnerability.
Tracked as CVE-2021-21974, the security flaw is caused by a heap overflow issue in the OpenSLP service and can enable an attacker to remotely execute arbitrary code.
VMware confirmed it is aware of exploit reports, adding that it issued a patch in February 2021 upon discovery of the vulnerability. However, the vendor urged customers to immediately apply the patch if the ESXi hypervisor has not yet been updated.
Widespread exploitation
Analysis from ransomware monitoring service Darkfeed found that the spread of the ESXiArgs ransomware is “extensive” and could have affected at least 327 organisations worldwide.
“The most targeted system is from France on OVH cloud and Hetzner hosting,” the service said on Twitter. “But they have hit other hosting and cloud companies around that world.”
In a statement on 3 February, OVH confirmed it was responding to the wave of attacks, adding that its managed cloud service had not been impacted.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
“A wave of attacks is currently targeting ESXi servers,” the company said. “No OVHcloud managed services are impacted by this attack however, since a lot of customers are using this operating system on their own servers, we provide this post as a reference in support to help them in their remediation.”
Royal ransomware
Initial speculation from OVH suggested that this campaign was related to the new Nevada ransomware strain, which first emerged in December last year.
However, reports over the weekend pointed towards the Royal Ransomware strain as a key driver behind the wave of attacks against ESXi virtual machines.
Royal Ransomware started launching attacks in early 2022, with the group made up of previous veterans of the infamous Conti ransomware gang.
The group has accelerated operations in recent months, focusing attacks on US-based healthcare organisations and specifically targeting Linux systems more recently.
Stefan van der Wal, consulting solutions engineer at Barracuda Networks said that the current campaign highlights the critical risk for organisations failing to update software.
RELATED RESOURCE
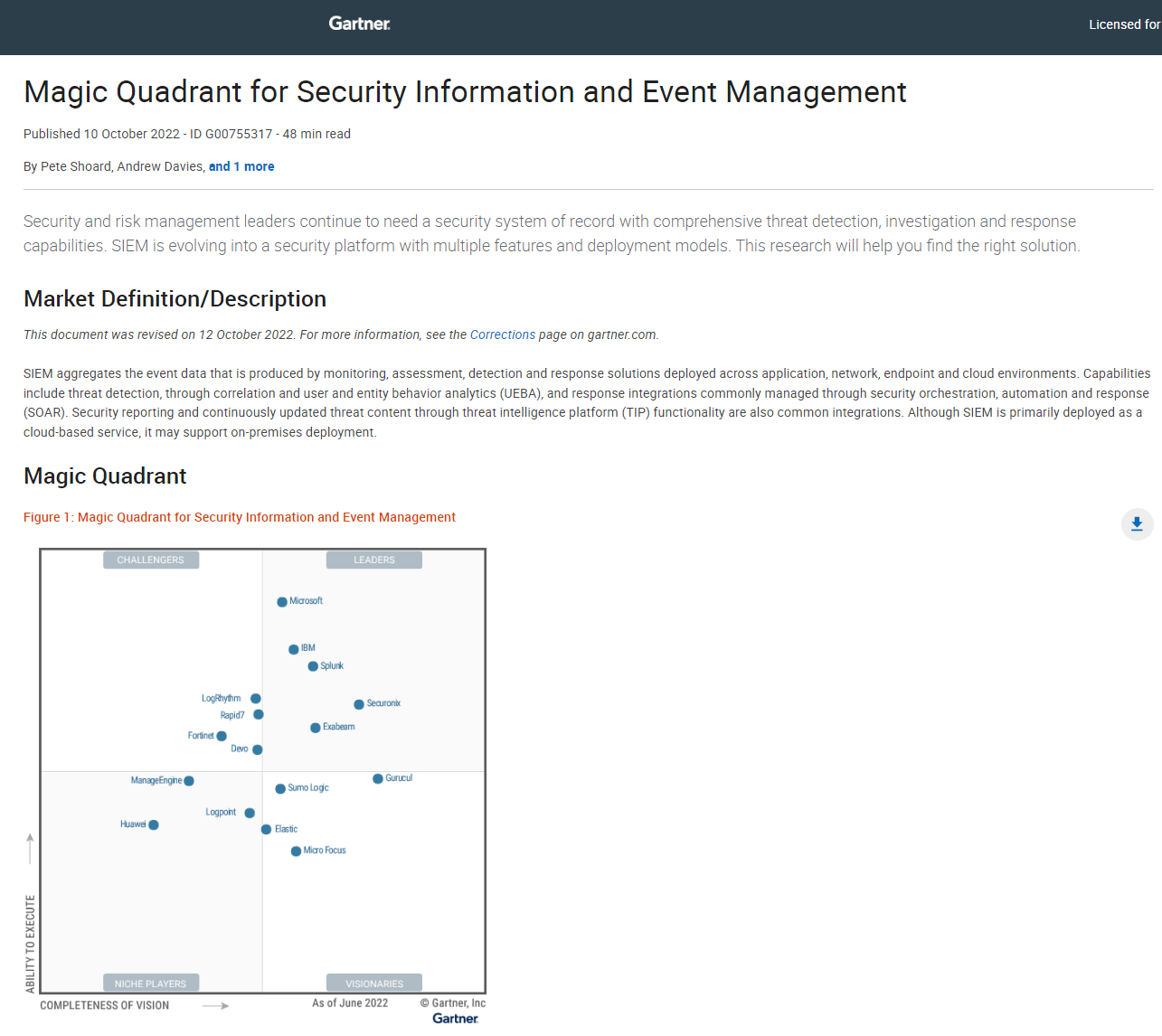
2022 Magic quadrant for Security Information and Event Management (SIEM)
SIEM is evolving into a security platform with multiple features and deployment models
“The reported widespread ransomware attacks against unpatched VMware ESXi systems in Europe and elsewhere appear to have exploited a vulnerability for which a patch was made available in 2021,” he said.
“This highlights how important it is to update key software infrastructure systems as quickly as possible.
“It isn’t always easy for organisations to update software. In the case of this patch, for example, organisations need to disable temporarily essential parts of their IT infrastructure. But it is far better to face that than to be hit by a potentially damaging attack.”
Van der Wal added that virtual machines are becoming an increasingly attractive target for ransomware gangs due to their use in running business-critical services and functions.
“Securing virtual infrastructure is vital,” he said. “It is particularly important to ensure that access to a virtual system’s management console is secured and can’t be easily accessed through a compromised account on the corporate network, for example.”

Ross Kelly is ITPro's News & Analysis Editor, responsible for leading the brand's news output and in-depth reporting on the latest stories from across the business technology landscape. Ross was previously a Staff Writer, during which time he developed a keen interest in cyber security, business leadership, and emerging technologies.
He graduated from Edinburgh Napier University in 2016 with a BA (Hons) in Journalism, and joined ITPro in 2022 after four years working in technology conference research.
For news pitches, you can contact Ross at ross.kelly@futurenet.com, or on Twitter and LinkedIn.
-
 Kaseya shifts from AI ‘insights’ to autonomous action with new agentic platform
Kaseya shifts from AI ‘insights’ to autonomous action with new agentic platformNews The company aims to evolve from its suite of management tools into an autonomous operating system for MSPs
-
 Accenture to roll-out Copilot to 700,000+ staff
Accenture to roll-out Copilot to 700,000+ staffNews Accenture will roll out Microsoft Copilot to nearly three quarters of a million employees after years of testing
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwise
The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwiseNews Billing itself as the “only place ransomware allowed", RAMP catered mainly for Russian-speaking cyber criminals