Portugal government cyber attack allegedly leaks "hundreds" of classified NATO documents
Reports in Portugal have suggested the classified files were lifted by specially designed bots and have now been found for sale online


The Portuguese government’s department of defence (DoD) has reportedly been the subject of a ‘significant’ data breach involving the theft of NATO documents.
According to local media, “hundreds” of documents sent to Portugal’s officials by NATO have been found for sale on the deep web and the General Staff of the Armed Forces (EMGFA), the department that was attacked, only found out after US intelligence informed them of their discovery.
The US made direct contact to Portugal’s prime minister António Costa in August, informing him of the NATO documents it found for sale online, according to Diário de Notícias (DN) which first reported the story.
IT Pro has contacted the EMGFAfor confirmation of the reports and further details, but neither organisation responded.
"We do not discuss alleged leaks of classified information," said a NATO official to IT Pro. "Portugal is a valued NATO ally, which makes important contributions to our shared security."
Sources speaking to DN said the EMGFA has conducted a comprehensive audit of its IT systems and identified the computers from which the NATO documents were stolen.
The department concluded that rules surrounding the secure transmission of classified documents had been broken.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
RELATED RESOURCE
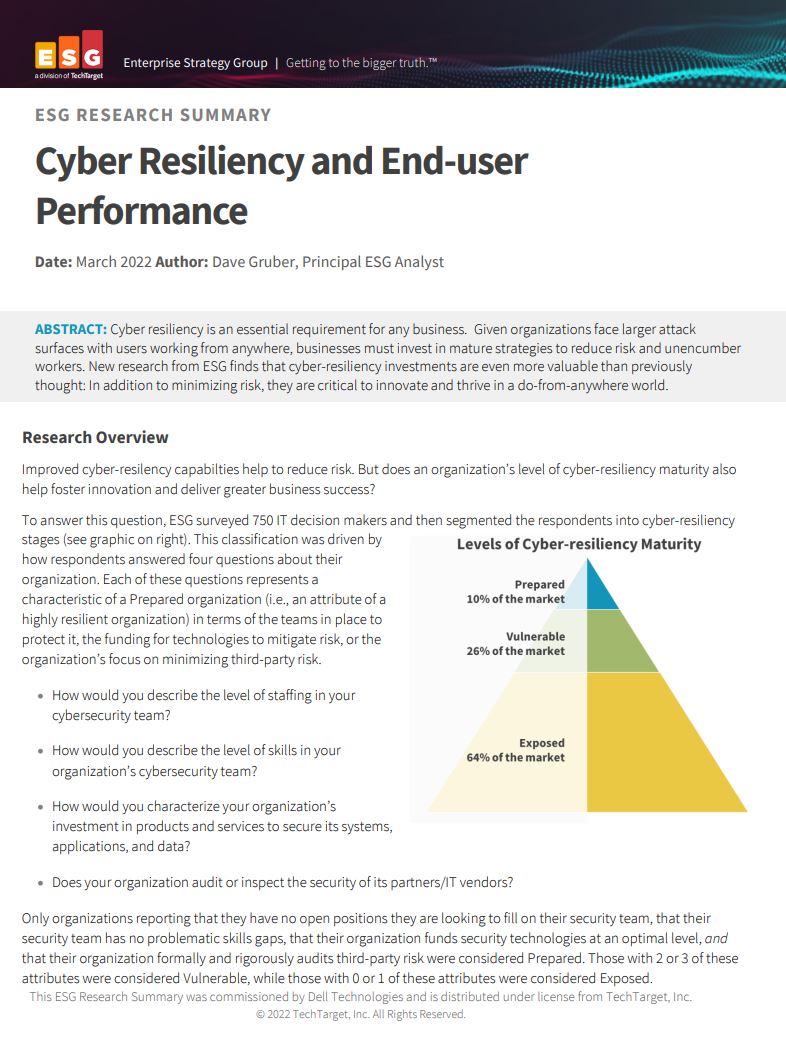
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
Unsecured channels were used to receive and forward the documents when the Integrated System of Military Communications (SICOM) should have been used, the report stated.
“The exchange of information between allies in terms of information security is permanent at the bilateral and multilateral levels,” said a spokesperson for prime minister Costa.
“Whenever there is a suspicion of compromise of cyber security of information system networks, the situation is extensively analysed and all procedures aimed at enhancing cyber security awareness and the correct handling of information to deal with new types of threat are implemented.
“Disciplinary and/or criminal law automatically determines the adoption of appropriate procedures."
Other DN sources said the cyber attack itself was “prolonged in time and undetectable”. The sources also said the attackers use specially crafted bots to search for the specific type of documents that were ultimately exfiltrated.
IT Pro has requested additional detail about the attack from official sources and will update if they surface.
The US declined to confirm the reports to DN, saying it does not comment on intelligence matters.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Compromised open source package pushed malicious Elementary CLI release to developers
Compromised open source package pushed malicious Elementary CLI release to developersNews The open source Elementary CLI tool has more than one million monthly downloads
-
 Everything you need to know about the GitHub Copilot pricing changes
Everything you need to know about the GitHub Copilot pricing changesNews GitHub Copilot pricing changes mean users will be charged based on consumption, rather than a set number of credits