
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
This automatically-generated transcript is taken from the IT Pro Podcast episode ‘Meet the cyborg hacker’. We apologise for any errors.
Adam Shepherd
Hi, I'm Adam Shepherd,
Connor Jones
And I'm Connor Jones.
Adam
And you're listening to the IT Pro Podcast, where this week we're taking a look at the emerging world of biohacking.
Connor
Now it's probably worth making the distinction between the two types of biohacking there are in the world right now. You know, there is of course, the kind of biohacking reserved for scientists, professional and homebrew, that involves the CRISPR gene editing technology. But this of course, is is an IT podcast and we're most concerned with a form of bio hacking of the cyber kind; you know, the one involving tech baked into the human body.
Adam
Now, since the invention of computer systems, people have been finding ways to break into them and customise their operation to best suit their own needs. In recent years, however, adventurous experimenters have begun exploring how the same principles can be applied to the human body.
Connor
The so called biohackers have explored a number of ways to combine digital technology with flesh and blood, including implantable chips, digitally enhanced prosthetic limbs and much, much more. But what potential advantages does human augmentation hold? And are there any security risks that might be associated with this emerging practice? We're joined today by Len Noe, a technical evangelist, white hat hacker at CyberArk, and self described transhumanist, who's been immersed in this world for a number of years. Len, thanks for joining us.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Len Noe
Thank you guys for having me. It's a pleasure to be here.
Adam
So Len, first of all, you've got a number of, shall we say aftermarket extras? Can you talk about some of the biohacking modifications that you've made yourself?
Len
Well, to be fair, I didn't make them myself. I, the first thing I'm going to say is everything I have, I've done it as safely as humanly possible. I'm not one of those. Do It Yourself guys to do this in your garage.
Adam
Don't try this at home, kids.
Len
Yeah. I mean, there was a time that that was the way it was, but we passed that time, we can actually get some some some safe implants. Yeah, currently, I have eight different microchips with varying degrees of functionality, but predominantly, they revolve around RFID and NFC. I can do redirection tags via NFC, I can also have chips that will handle a lot of physical access cards like MIFARE classics, HID procs one and two, pyramid and dala, I actually have a credit card payment chip in my the top of my left hand, so I can actually do tap to pay with my hand, I have a biosensing magnets so that that one's a lot of fun. It's not really a lifting magnet. But due to the way that the magnet was constructed, it actually gives me the ability to feel electromagnetic currents and electromagnetic fields, kind of like a spidey sense. So yeah, and we can get into it a little later. I'm actually in the working on the second round of my prototypes for my pegleg. Those won't be the standard microchip style things. But that's actually a Raspberry Pi Zero W2 that's been actually loaded with Kali encased in bio encapsulation, and then I'm going to be implanting that in my leg, so that way I can actually take systems into places where you can't, or shouldn't be allowed to take technology. So having it set up to run low energy Bluetooth sweeps along with auto pwns while I'm sitting here talking, so yeah, I kind of have a little bit of a fascination with human upgrades.
Connor
This is already my favourite podcast I've ever done. This is great. Can I just ask what is what is the upside of being able to detect and sense electro magnetic fields?
Len
Well, I'm also very, very passionate about physical pen testing. I'm an avid lock picker. I'm a member of multiple different lock picking clubs. And when you look at physical security, especially around warehouses, how are most of them secured? Magnetic locks, magnetic locks require electricity. So depending on the wiring and the amount of shielding in your your Romex cabling for your electromagnet, I can sit on the outside of your building, run my hands over the wall, and I can actually trace your electrical lines. So at that point, I actually have an idea of where to shim or make, you know, especially if it's a destructive pen test, I can make a small hole and basically clip the electrical wire. And if you know anything about mag locks, especially if you're dealing in like an emergency situation like a fire or a power outage, magnetic locks are automatically designed to actually go into an open state due to an emergency to allow people to get out. So basically the that's one great thing for the magnet. The other thing is it makes a really cool trick at a bar, you can pick up bottle caps and things, you know. And it's, if nothing else, it's a really cool way to get, it's a cool magic trick around young kids too.
Adam
In the immortal words of the Insane Clown Posse: magnets, how do they work?
Len
Why do you have to go there, man? I mean, I'm from Detroit, but I mean, in St. Cloud, we had better musicians, man, let's go with the MC5 or, or the Bay City Rollers. Ted Nugent.
Adam
This is Shaggy 2 Dope erasure, and I will not stand for it. So in terms of some of the other practical use cases that this technology has, aside from the magnets, you mentioned some of the chips that you've been using, particularly the RFID and NFC devices, the contactless payment devices; what other kinds of use cases are there for this technology, either currently, or that you can kind of see emerging in the near future?
Len
Well, I mean, at this point, it's anything around the contactless technology, we see a lot of NFC used in IoT. You know, when it comes to personal devices, almost every mobile device or tablet that's been released within the last three to five years has NFC capability. And the truth is not a lot of people understand what it is. And the fact that it by its design is an unsecured protocol. You know, the problem when it comes to NFC is we're using application level security to try and lock down an insecure protocol. You know, so anything from, you know, compromising a mobile device through the use of the implants, I mean, one of my favourites is the physical access side of things, you know, and, you know, let me, let me go into this for just a second, if I may, you know, when it comes to our physical access, a lot of places, especially in my tenure, you know, and I've been doing this kind of work for pushing 30 years, only two companies I've ever worked for had any type of multifactor for physical access locations of high, high privilege, you know, data centres, things like that. Most companies will have a single point of access, and it's usually just a bar or a card read, and then the door unlocks. So if we take a look at my implants, and the fact that I have the ability to basically emulate multiple different physical card protocols, here's where it gets funny. If I don't have a copy of a cloned badge, if I don't have a Proxmark, or some type of replay device, if I'm found in a restricted area, the worst you're going to be able to do is trespass me. You're not going to be able to get me arrested, because all I have to do is say, hey, you know the door was open, I'm here looking at the building, I thought this was part of the tour. You know, unlike the days of old, you know, where if I did have that physical piece of evidence that shows how I got in there, then I can be actually looked at as a criminal. So I'm playing a lot in the grey areas. You know, the whole point is the obfuscation. I'm not doing anything that anybody else hasn't done before in a different method, I'm just doing it in a way that would be very, very difficult from a digital forensics or incident response perspective, to be able to actually find that true root cause, on top of the fact that even if they saw some of the bulges in my my skin where I have some of my implants, when it comes to most of the privacy laws in most, you know, first world countries, they're not allowed to actually delve too deeply because it involves my personal medical, the minute it went inside my skin.
Adam
And also, I'd imagine they're not the kind of thing that one would typically notice, unless you knew exactly what you were looking for and where, right?
Len
Exactly. I mean, I've gotten asked a lot of questions in turn over the since I started doing this, like, you know, are these the same chips that I that, you know, are in my dog, are these chips that are in my cat, you know, and in some way the answer's yes. I mean, they all run on the same NFC style protocol. You know, and just like when it comes to a pet, you know, they have those very large wands. So they're gonna they would have to actually try and find the implant, energise the chip, to be able to get a read. Therein lies the same problem when it comes to all augmented humans, in order to be able to detect me and my chips, you would actually have to energise those chips to be able to get a read. So you would need multiple different spectrum analyzers on both high frequency and low frequency. And they would have to be strong enough to energise my entire body in order to for the detection. So from a management or you know, an actual implementation perspective, there is currently no way to actually detect an augmented human with this type of technology inside the body. And that becomes a very large problem for security professionals. And the only way that I can really give as a way to try and combat this is a true defence in depth, and a layered security approach. You know, I've said it a million times, you know, we have no problem putting multifactor authentication in front of all of our privileged data. But we don't do the same thing for our physical locations. And when if there's one person out here, like me, that has the ability to do this, I think that's fact enough that we should be looking at this as a potential threat on a larger scale, and we need to address it accordingly.
Connor
So you can clearly see that there's a real benefit to having sort of, like you said, multi layer security with a biological air to it. And you obviously yourself also, what maybe like 5% technology, both by the amount of things that you've got in you by the sounds of it.
Len
I'm working on it; I'll take 5% is a compliment.
Connor
So what what what attracted you to the world of biohacking in the first place?
Len
Why do you climb a mountain? Because it's there. If anybody wants to take a Google, just google me and you can find a picture; I am, I consider the fact that I have one tattoo, it just starts at my neck and goes all the way to my my, the top of my feet. I do flesh hook suspensions for fun. So when I saw that people were actually implanting technology, it just seemed kind of like the next natural evolution to somebody like me, I considered myself to be a modern primitive for a very, very long time. So as far as I know, I was the first person that had brung the, the idea that these can be used for an offensive purpose to the security community. I know I am not the first guy to ever do this. I'm just the first guy that opened his mouth about it. And I think that goes into just the way that I see the world. I was a black hat for a very, very long time. So when I look, walk into a room, the first thing I see is okay, there are cameras, where's the the exit strategies? You know, if you tell me that this is an NFC chip that can interact with a mobile device, maybe you're going to use it for your digital business card, I'm going to look at that same device and see how can I use this in a way that would suit my purposes?
Adam
So let's talk about some of those methods, then some of those ways in which this technology could potentially be used to target businesses. You've spoken already about some of the offensive applications of the magnets you have, for example, but what about some of the, for example, the NFC and RFID chips?
Len
Sure. NFC, you know, like I said, it's pretty much a standard protocol on most modern mobile devices and tablets. The abilities through NFC can be anything from transferring, beaming a file, it could you can use it to set up a Wi-Fi network, you can use it to redirect. I mean, we've seen all kinds of different possibilities. So the way that I've redirected those, I released three different attacks at RSA two years ago. The first one was called Flesh Hook. Flesh Hook is a redirect. Yeah, I made the exploits. I got to name them. That's one of the benefits. So essentially, what that one was, is I would I've set up a BeEF server. And you know, for any of the newbies out there that don't remember the good old days of BeEF, BeEF is the browser extension exploit framework. This is the website that, you know, we've all heard the rumours of the minute you log into this website, the bad guys are in your system. Yeah, that's BeEF. So it's a little bit of a social engineering play. You know, I'd walk up Hey, Adam, man, check this out, dude. Let me see your phone. I found this amazing new video on YouTube. I want to show you. As soon as I can get the device in my hand, if you have NFC turned on, the large flexNExT implant that's in the top of my right hand will actually have enough distance on the antenna that it'll actually read through the actual meat of my hand. I can hold the phone in the correct orientation. It will pop up a redirector where I'm going to just send you to a video, but the minute your browser hits that website, the Java code in the HTML page is actually going to hook the browser and then I have access to the entire BeEF suite. So I can do on device spear phishing attacks, I can geolocate your device, access the cameras, I can use DNS enumeration if you're on a local network or a corporate network, I can do domain identity, subdomain identification and enumeration. Anything that I could even think of. The other one was called leprosy. Again, my attack, I named it. Leprosy doesn't really work as well against iOS devices. But when it comes to Android, once again, you know, this one is a little bit easier. Adam, oh my god, man. You know, I'm over here in the UK with you, you know, my phone died. My wife, I was just on the phone with my wife. She told me something happened to my grandson, man, can I borrow your phone for just a second? You know, of course, you know, you know, yeah, here, dude, call your wife. And again, the URL that's been programmed into the NFC chip, points to a web location where I've got an infected APK that was created with MSF Venom or, you know, a Cobalt Strike beacon. At this point, you know, it's Oh, my God, you know, let's be honest, who remembers my who remembers phone numbers anymore? What's my wife's phone? What's the country code for the United States? Plus one. Okay. So I can go through this big rigmarole of trying to remember a phone number, when actually what I'm doing is installing that APK. And as soon as I'm done, it's like, oh, shit, I can't remember the phone number man here, I'm gonna just go plug my phone in. But at this point, I have a reverse TCP connection back to the device, I can set up persistence, I can get a shell. I mean, at that point, it's whatever I want. And the third one was called handshake. You know, they're all you know, biologically related names. What can I say? And, you know, at that one, you know, I can use a Proxmark, any type of card skimmer I want, get your badge information, write it down onto one of my chips. And if we're in one of those single point access situations, I'm in your privileged locations on prem. And once again, the problem is there's zero indications of compromised to any one of these different attacks.
Connor
I think judging by mine and Adam's reactions after the first question we came in with, and we're just like grinning like Cheshire cats, right? I think we can speak for the both of us saying we're so excited just to hear about this kind of thing, because it's not something we hear about a lot. So with that in mind, then, how many black hats like your former self, are using this in the wild or starting to think about using it in terms of real world attacks?
Len
Okay, this is one of the hardest questions to answer in regards to doing conversations like this. I can tell you this with 100. There, there are some facts that I can give you with 100% certainty. Within the United States, one of the biggest distributors for microchip implants is a company called DangerousThings.com. Within Europe, there is a company called KSEC, K-S-E-C. So I am, I spoke with the CEO of Dangerous Things, a gentleman by the name of Amal. And from him, I was able to gain the fact that Dangerous Things has sold close to about 300,000 implants. I was actually back in y'all's neck of the woods last weekend up in Newcastle, where I actually got to meet Kai from KSEC. And between the two of us we basically came up with an estimation of between four hundred and six hundred thousand implants have been shipped. How many of those implants were actually, have actually made their way inside of a human body? We don't know, but I can tell you this much. I know that I'm using it. I know of quite a few people who are on red teams that are using this technology. We have not found any indications from any type of incidents that have actually happened in the wild where implants were shown to be the root cause, but at the same time, how would you be able to determine that, you know, and therein lies the problem. We may have, I mean, we've seen, you know, breach reports where NFC or RFID were included in the evaluation in terms of cause of breach, but without actually getting access to an individual to find out if they were actually augmented, it could have been a card, it could have been an implant, we don't know. Because, as I said before, there's really no way to determine any type of augmented human with current technology.
Adam
And if yourself and, you know, a significant amount of other red teamers are using this technology and are interested in this technology, it's a fairly safe bet that black and grey hat actors are also interested in it and are deploying it in the wild, you know, it's not, it's not that much of a logical leap.
Len
No, and that's the way I see it. If once I actually brought this to the out at RSA, I knew this was going to open the door and somebody who is going to read this and there's going to be some black or grey hat somewhere that goes, Hey, this is a new vector. And due to the you know, the privacy laws and everything else, this becomes a much safer road to try and travel if you're going to try and do offensive type activities.
Adam
So let's talk about some of the practicalities of this, then, cause this is a very kind of new, very emerging field. Have you experienced any challenges with biohacking and with your implants, you know, other than getting through airport security, which I can imagine is just a barrel of laughs.
Len
Okay, well, you brought it up - the airport is the number one question that I get.
Adam
I'm not surprised.
Len
You want, would you like me to tell you how I walk, how I get through an airport?
Adam
Absolutely.
Len
I put one, the left foot in front of the right and then I repeat. That's it.
Adam
No. Does it, do none of them come up on the scanners?
Len
All right, let's talk about the two different types of metal detectors for two seconds. We have the magnetometer which is just kind of the archway you walk through. There is not enough combined metal in all of my implants to actually trigger a magnetometer. I'm going to carbon date myself here; before my my career in IT, you know, almost 30 years ago, I used to do the job of the TSA before there was a TSA and airport, airport security was still privatised. And don't quote me on this, but I if I remember correctly, the magnetometers would not trigger unless you had a combined metallic weight of at least a .22 calibre bullet. So I mean, if you think about it, when you walk through a metal detector, if you have like a necklace on with a gold charm, it doesn't go off, if you have earrings in, it won't go off. Now, I'm not saying that they couldn't change the sensitivity of the magnetometers to where they would detect it. But they would get so many false positives, trying to check people into an airport that it would be an unusable control. Same with the metal detectors. When you think about my implants, most of them are actually silicone, you know, with the exception of the copper antennas on the larger flexible main membrane implants or the bio magnet, which is a iron core wrapped in titanium, but that's less smaller than the size of a pea. So even if I'm doing you know, the X ray metal detector, doesn't show up, I can walk straight through, the magnetometer will not trigger. So that to me kind of says something about what we're dealing with in terms of airport security. But, you know, we can do a different talk on that one another day.
Adam
That's quite a scary prospects in some ways, particularly if you're trying to defend against these types of attacks.
Len
Yeah, I mean, thankfully, at least at this point, there's not a lot in aeroplanes that are relying on RFID or NFC, you know, but if I can get that pegleg you know, where I actually have a full Linux system, then yeah, that is something that could potentially interact with the Wi-Fi entertainment system on the plane, I mean, it opens a whole lot of different vectors at that point.
Adam
But even beyond air travel, if airport security - which is, I would argue, among the most stringent kind of security, you know, scanning in terms of concealed objects and devices - If it can get past airport gate security, then security in and out of a building or or complex doesn't really stand a chance for detecting this kind of stuff, does it?
Len
Not even, not even a little bit. You know, one one thing that I, just cause you guys are are a lot of fun, and I think you guys will get a kick out of this. I think everybody is familiar with the drug smelling dogs that are used by the authorities.
Adam
Yes.
Len
Well, one of the, they actually have a new type of canine that is being released to help military and law enforcement. And they're actually technology sniffing dogs.
Adam
No.
Len
Yes, you can look them up. So these are not used in the same way that narcotic sniffing canines are in terms of they don't use them to be able to get an arrest. They don't bring them up and smell somebody and go, okay, yeah, we've got you, we're going to take you away. They're used more in the post arrest investigation point. They're used a lot with human trafficking, child predators, things like that; people that would actually store illegal data on hard drives, in technology. So if someone gets arrested, they'll get a search warrant, they run the dog around the house looking for hard drives, thumb drives, you know, anywhere that they may have, you know, tried to store illegal and illegal things. I found out that one of the law enforcement agencies that is close to me here in Texas, actually recently got one of these drugs, these key technology smelling dogs. So after, you know, sending an email to the police department going, No, I am not crazy. Yes, I have implants. And here's here's my CV. So you can see I'm a real person, and I'm not messing with you. I'm interested in information about this dog. And after they researched me, they're like, okay, apparently cyborgs are a real thing. They became really open to, you know, having conversations, and I've actually been invited to go up to the Dallas Police Department. And we're going to see if Remi, the technology dog, is able to sniff any of the implants that I have. Because that would actually be probably one of the first ways to try and detect somebody of augmented nature. And the one point that I wanted to point out, and since you guys are definitely geeks, and take that as a hardcore compliment, if you think back to the Terminator movies, where, you know, wherever the resistance was right at the entrances, they always had the guys with the dogs, because they could smell the technology. And I just start to wonder is this going to be a situation where life imitates art or art imitates life? I don't know which, but I'm really excited to get up there. Due to my travel schedule, it's been a little difficult, but I'm hoping to be up there sometime towards the middle of November. And you know, maybe I'll drop you a line and let you guys know how it turns out.
Adam
Yeah, absolutely. I'm going to ask the obvious question, how can dogs smell technology? How can anyone smell technology?
Len
Okay. Just like the they've taught the dogs to be able to detect specific narcotics, you know, heroin, cocaine, marijuana, things like that. They actually have taught them to key in on specific components that are used in the creation of technology. The name is triphenylphosphine oxide.
Adam
Oh, wow.
Len
So they found one very, very specific element that is used in the creation and manufacture of technology circuit boards, hard drives, and they basically train these dogs to hit on that one specific compound. I don't know if they'd be able to smell it through the skin. I don't know. But I still think it's going to be one hell of an interesting experiment.
Connor
Hmm. Yeah, definitely. And you get to hang out with more dogs as well. So that's a win win, really, and especially in my eyes. So in terms of getting this tech into the mainstream then, because obviously, I'm just from hearing you for the past half hour, I'm super excited about it, and I'm probably not going to be alone. So say further down the line that this kind of stuff does reach consumers, the everyday consumer that is, what are the limitations you can imagine a potential regulator seeing, you know, for example, can can realistically we actually have Internet facing machine augmentations of the kind like your like your peg leg, or is that is that a hacking risk waiting to happen?
Len
Um, well, I mean, let's be honest, you know, we can talk about QR codes and they are hacking risks waiting, just waiting to happen, and we see those on buses and trains, and taxi cabs. I don't think honestly, the imposed threat of any technology is going to stop someone from using it if there is the potential for a monetary gain. So to answer your original question, there is a lot of implants going out right now that I see is going to probably help break that stigma barrier. One of them, like I said, is the Walletmor chip that I have in my right hand, it's an actual credit card. So I can do tap to pay. I think, right now, the idea of implants is still, like you said, it's very, very fringe. And you everybody looks at me like I'm some kind of a terminator half the time. I mean, my friends shut their Bluetooth and their Wi-Fi off, the minute I walk into a room. All I want to do is just look at him when I leave and go, I'd be back. But another one that I see that's really made an impact is there's the ability, if you drive a specific model Tesla, you can get an implant and you can programme your valet key onto an implant. And you can basically just jump in your Tesla and you can drive. I think as we see a lot more of these types of implants and technologies that people can actually find a legitimate day to day use for is going to help with the concept of adoption and understanding and acceptance. Right now, there's like I said, 400,000 to 600,000 potential augmented humans out there. I see it moving beyond just the microchip concept, especially with a lot of the advancements we're seeing around graphene batteries. The big issue when it comes to any type of implant is outside of anything that's considered biomedical, there's no internal power for anything yet. And even when it comes to the pegleg, that I'm planning on putting in myself, it uses an indirect power receiver to actually power the device, but there's no battery in it. Because to charge something generates heat. So I think we're right at the precipice of you know, a whole new set of things that could be potentially coming out. I did a keynote in Newcastle over the weekend, and the title was Resistance is futile, we're already Borg. And in that talk, I just brought up some of the stuff that's actually already out there that people may not even be aware of. We've got spinal implants that are, you know, returning motility, to paralysed people, we have ocular implants that are working on giving sight to the blind, we're able to use DNA as a storage medium, and one gramme of DNA could potentially hold over seven terabytes worth of data with a retention period of over 100 years. So we are right on the cusp of so many different technological breakthroughs that cross that human technology barrier, that I think that you know, in terms of what we're going to see in the relatively near future is going to really be up to the order in which these discoveries are made.
Adam
So speaking of future technology, and just going back to the kind of Tesla use case you mentioned a little earlier, just as a brief digression. What do you think is the kind of feasibility of projects like Neuralink and other brain computer interfaces?
Len
Oh, you brought up Neuralink, if everybody's familiar with Neuralink, but nobody's familiar with the other company. I'm very, very interested in BCI. Brain computer interfaces, especially for disabled and locked in individuals, I think it's going to be crucial. I just watched an amazing documentary on my way back from Newcastle. Dr. Phil Kennedy, the name of the documentary was called Father of the cyborgs. Dr. Phil Kennedy was actually one of the he's a neurosurgeon. And he actually was the first individual to implant brain computer interfaces into paralysed people. You know, so everybody wants to talk about Neuralink, but they don't want to talk about all the other ones. Another really big player in the BCI field is Synchron. And they're already in human trials. So I think that the idea of BCI is definitely something that's going to happen. But at the same time, all of these new technologies they do will have, you know, an underlying firmware. You know, and one of the things that I'm trying to look at in regards to this, the melding of technology and humanity is as security professionals, we already know there are going to be attack vectors there and we need to be talking about those now. You know, the attacks we see today, the vectors may have changed, but at the core, every single attack today is the same attack that it's been for the last 20 years. I mean, they're looking for credentials, I'm looking for data, I'm trying to exfiltrate things, or I'm going to ransom you, you know, the end game is going to be the same; how we get there may be different. And if we think about all this new advancements in technology, and just that crossover, what happens when ransomware starts affecting Bluetooth or internet enabled bio implants, you know, what happens if I'm, my pacemaker gets a ransomware, then it's an a real ransom at that point. You know, and, you know, we keep running towards the technology and trying to, you know, make ourselves more than human, which is absolutely the core of, you know, the trans human movement. But one thing that I've said all along, and I even started the conversation with you guys today is, it needs to be done safely. And when we look at everything that's coming up, honestly, in my opinion, the end game is still identity, you know, and being able to maintain our individual identity as we become something potentially more than human. And as such, I think our identities, our personal information, you know, identity is going to become the new security. Because once the lines between an individual and the tech stacks that they're interfacing with, you know, gets either faded or removed completely, the only thing left is the individual and the individual identity of the person that's making those interactions.
Connor
So just to round things off, then looking at the long term, what kind of potential benefits might be out there for technologists or IT professionals, you know, outside of red teams and perhaps even security, who want to explore biohacking as the practice itself matures?
Len
Well, again, you know, that's like, in my opinion, that's like asking someone how, how do you want to utilise a laptop or a mobile device? I mean, these microchips were never designed to be used necessarily as offensive tools. But if you look at things like Mimikatz, which is every hacker's favourite LDAP tool, it was, it's originally designed as a an LDAP auditing tool. Any tool this, regardless of what its intended purpose was, can be reused and misconfigured and used as a weapon. So I guess I, you know, not to try and blow off your question. But I guess it depends on really, what are they trying to do? You know, it could be something, I mean, I have no doubt that maybe we're going to start seeing the ability to do OTP. If you're not familiar with it, there's an amazing ecosystem out there. It's called the VivoKey. And this is an implant, the VivoKey architecture will actually allow for one time, you know, MFA OTP, where you're actually going to validate via an implant with an app on your phone, you know, so that's a potential security advancement moving forward, it could be something as simple as using your, your chip, almost kind of like a Fido chip, where you're going to scan your implant to access your computer, again, I would still want to password in there, don't like single points of failure as from a security perspective, you know, maybe you're gonna put your, your badge for work on your chip, and you're just not going to, you know, that way you can badge in. Not everything around implants, or implanted technology is a black art, for the lack of a better term, you know, they can be used just to make people's lives a little simpler. But one of the quotes that I love to use in pretty much every single time I talk is in from my personal experience, things that make life easier, rarely make them safer. So we have to, we are the security professionals, we're the ones that you know, have to warn the masses, we're the ones that have to take care of our employees. So it's up to us to understand what these kinds of threats are, and build that layered security approach and that defence in depth, so that these types of people, people such as myself, are left sitting at the door going well, I managed to hit the badge reader, but I still don't know the key, you know, our data, our physical locations, privilege is privilege, I don't care if it's physical, I don't care if it's digital, you know, and we are the ones that have been empowered by our companies to be the gatekeepers in the security for these types of things. And we need to do our job and be aware that people like me exist and build a strategy around that knowledge to be able to stop people like me.
Adam
Well, while we could spend all day digging into the intricacies of biohacking, sadly I'm afraid that's all we've got time for this week.
Len
Aww.
Adam
I know, I could spend the rest of the afternoon talking about this. But our thanks once again to cyberArk's Len Noe for joining us.
Len
It was absolutely my pleasure, guys. I really enjoyed talking to you. Maybe we can do it again sometime.
Adam
Yeah, absolutely.
Connor
Sounds great. You can find links to all of the topics we've spoken about today in the show notes and even more on our website at ITpro.co.uk.
Adam
You can also follow us on social media as well as subscribe to our daily newsletter.
Connor
Don't forget to subscribe to the IT Pro Podcast wherever you find your podcasts. And if you're enjoying the show, leave us a rating and a review.
Adam
We'll be back next week with more insight for the world of IT. And until then, goodbye.
Connor
Bye.
ITPro is a global business technology website providing the latest news, analysis, and business insight for IT decision-makers. Whether it's cyber security, cloud computing, IT infrastructure, or business strategy, we aim to equip leaders with the data they need to make informed IT investments.
For regular updates delivered to your inbox and social feeds, be sure to sign up to our daily newsletter and follow on us LinkedIn and Twitter.
-
 Market volatility is exposing weak partnerships across the channel
Market volatility is exposing weak partnerships across the channelIndustry Insights Strong partner ecosystems resist economic turbulence through versatility, skills, and adaptable technology
-
 Google Cloud Next 2026: all the live updates as they happen
Google Cloud Next 2026: all the live updates as they happenLive blog ITPro is on the ground at Google Cloud Next 2026, to cover all the latest announcements from the day one keynote
-
 Pentesters are now a CISOs best friend as critical vulnerabilities skyrocket
Pentesters are now a CISOs best friend as critical vulnerabilities skyrocketNews Attack surfaces are expanding rapidly, but pentesters are here to save the day
-
 Cyber professionals call for a 'strategic pause' on AI adoption as teams left scrambling to secure tools
Cyber professionals call for a 'strategic pause' on AI adoption as teams left scrambling to secure toolsNews Security professionals are scrambling to secure generative AI tools
-
 Bugcrowd’s new MSP program looks to transform pen testing for small businesses
Bugcrowd’s new MSP program looks to transform pen testing for small businessesNews Cybersecurity provider Bugcrowd has launched a new service aimed at helping MSP’s drive pen testing capabilities - with a particular focus on small businesses.
-
 Building a new approach to security with the next generation of penetration testing
Building a new approach to security with the next generation of penetration testingSponsored Combining human-led testing with continuous automated scanning can elevate your security regime
-
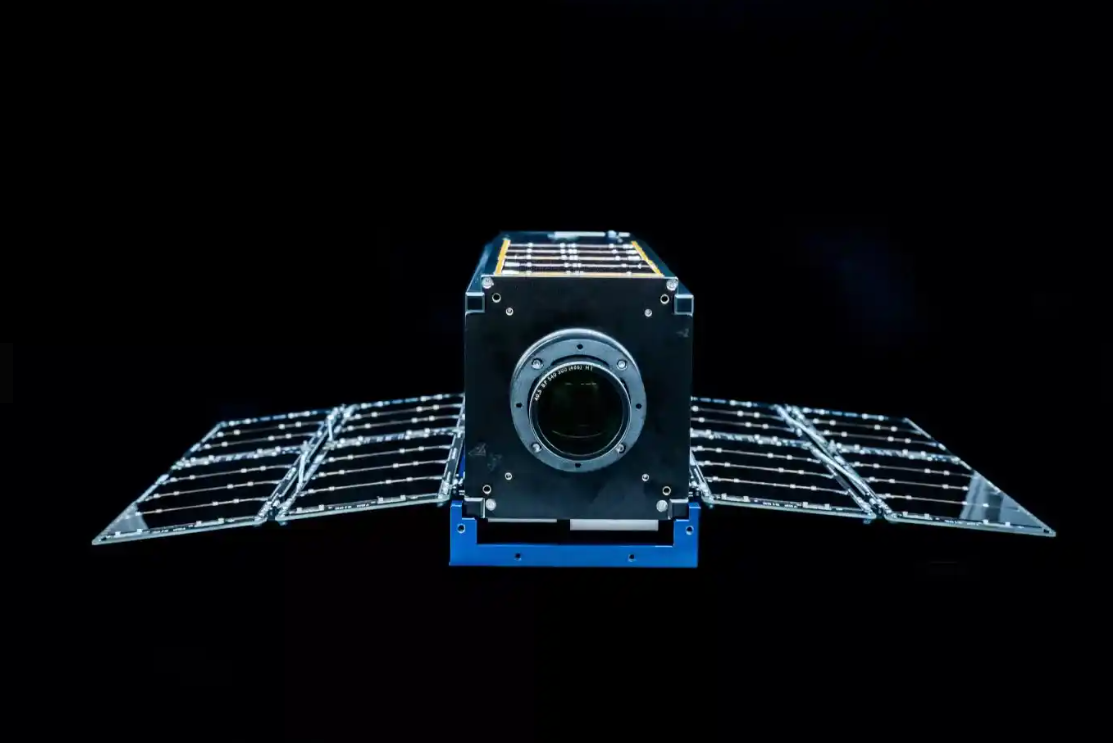 Why the Space Force wants white hats to attack a satellite
Why the Space Force wants white hats to attack a satelliteCase study Authorities hope the first-of-its-kind competition could bring benefits to the cyber sector
-
 OpenAI to pay up to $20k in rewards through new bug bounty program
OpenAI to pay up to $20k in rewards through new bug bounty programNews The move follows a period of unrest over data security concerns
-
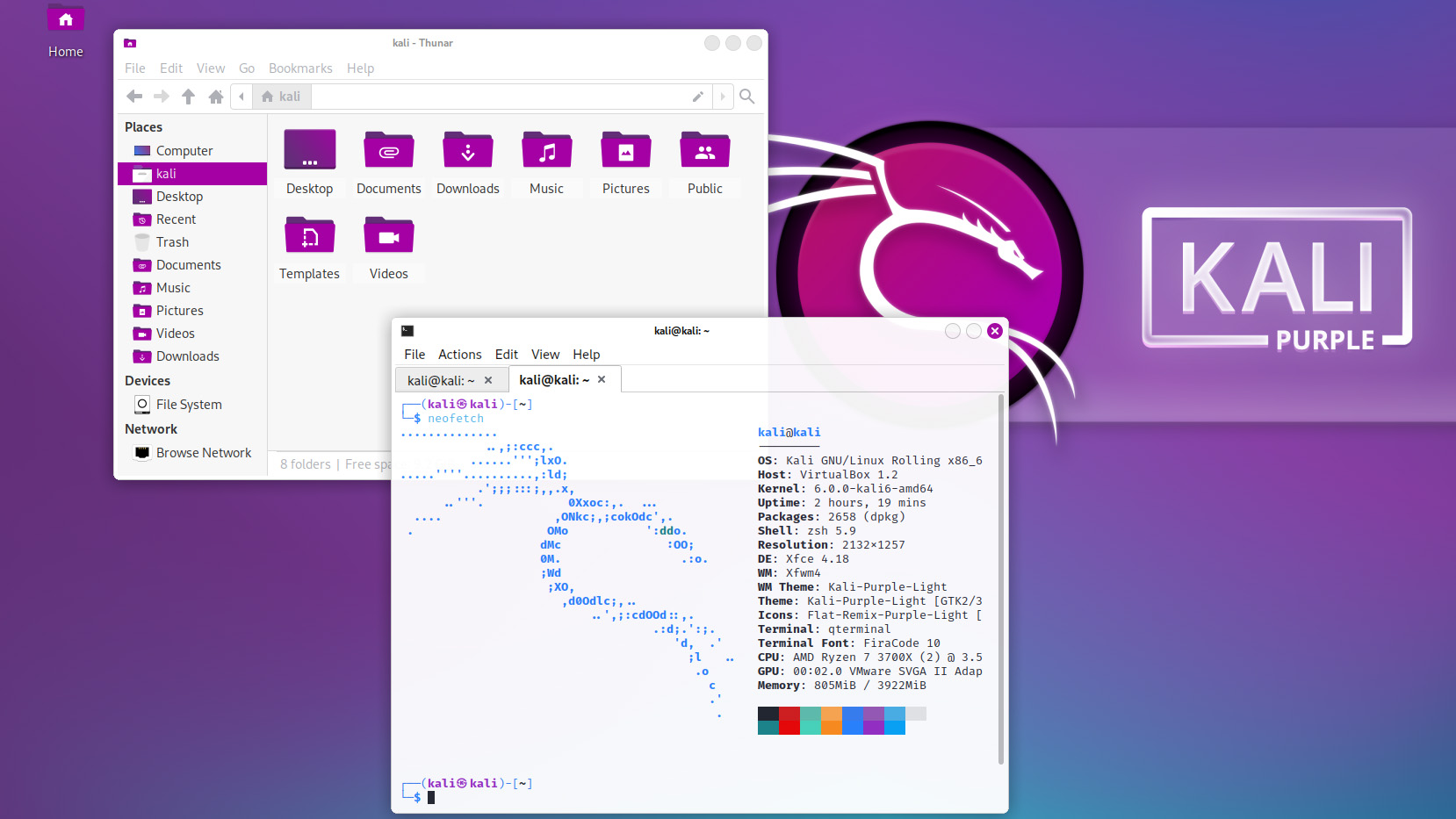 Kali Linux releases first-ever defensive distro with score of new tools
Kali Linux releases first-ever defensive distro with score of new toolsNews Kali Purple marks the next step for the red-teaming platform on the project's tenth anniversary
-
 New ‘DarkBit’ ransomware gang shuts down Technion, demands $1.7 million ransom
New ‘DarkBit’ ransomware gang shuts down Technion, demands $1.7 million ransomNews A politically charged ransom note suggests DarkBit are one of the newest hacktivist gangs to emerge in recent months

