Why the Space Force wants white hats to attack a satellite
Authorities hope the first-of-its-kind competition could bring benefits to the cyber sector
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
A US space launch is a very high-security affair. Systems are locked down, many of the staff hold national security clearance, and the rocket and its payload are carefully protected.
But when SpaceX launched its CRS-28 resupply mission to the International Space Station (ISS) in June, it did so carrying a special satellite that the US military was actively encouraging people to hack.
Run by the US Space Force, Hack-a-Sat was essentially a game of Capture the Flag. Organizers tasked ethical hackers with flexing their skills to break into a satellite and discover a special code, in a race against four other competing teams. The military hopes that this will also help raise awareness around cyber threats to space hardware.
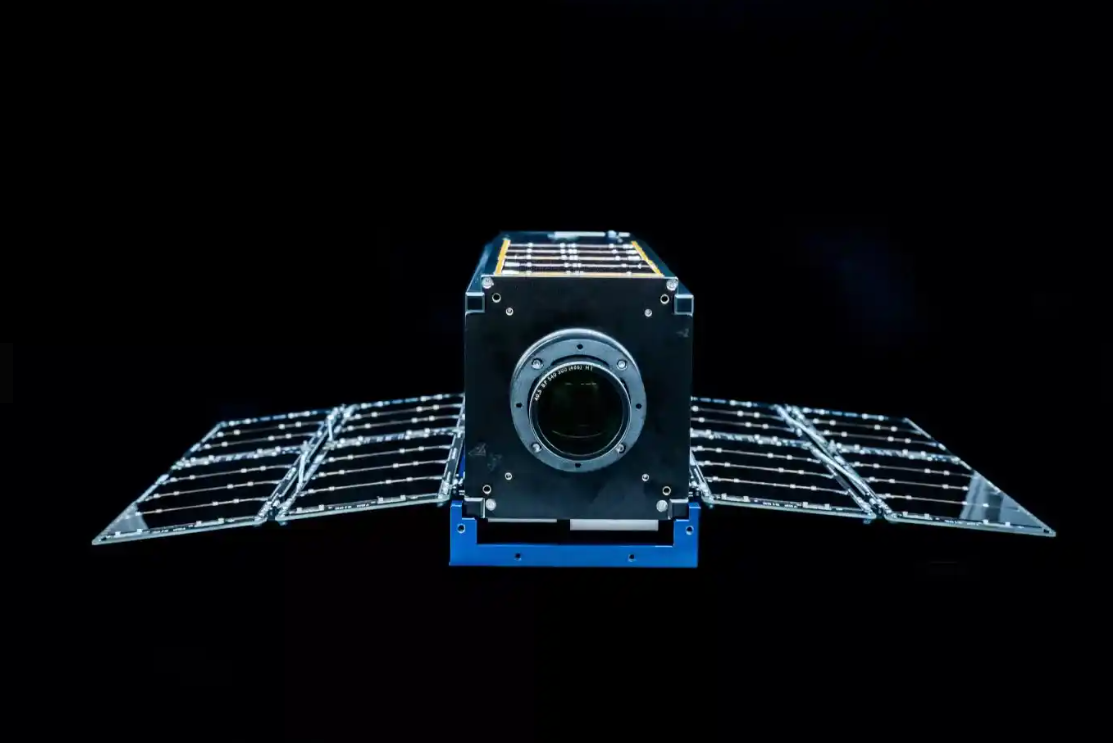
The diminutive 34 x 11 x 11cm “cube” satellite is named Moonlighter and was deployed into low Earth orbit after about a month aboard the ISS, and was the target in this year’s Hack-A-Sat competition.
The event brings skilled cyber enthusiasts together to build enthusiasm for careers in the sector and specifically attract raw talent to the field of cyber security for vital communications satellites.

The event brings skilled cyber enthusiasts together to build enthusiasm for careers in the sector and specifically attract raw talent to the field of cyber security for vital communications satellites. This could help protect government assets from a new generation of threat actors, and address the ongoing cyber skills deficit.
“They started to go and ask all the different organizations within the government and military saying, ‘Hey, can you let these hackers, these top cybersecurity enthusiasts, go and hack into your systems?’, and their first response was, ‘Absolutely not. No way’,” says Captain Kevin Bernert, the Space Force’s Hack-A-Sat program manager.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
But Captain Bernert’s team persisted. In the first few years, the competition was run on virtual machines (VMs) down on Earth, or actual space hardware planted firmly on the ground. This year, Moonlighter was actually put orbit where it patiently waited to be hacked.
RELATED RESOURCE

Discover how the encrypted threat landscape has changed over time
DOWNLOAD NOW
It’s a real test for the competitors, as there are specific difficulties that we don’t need to deal with down on Earth. “With space vehicles orbiting the Earth at high speeds, you only have a certain amount of opportunities to make contact with that vehicle,” says Bernert.
Hackers trying to send a command package, for example, might not know if it was successfully executed until the next time they can make contact. Other challenges include limited bandwidth and tricky power management. Hackers must be careful about how much energy their code uses on a device powered by only a solar panel.
Would-be attackers also need to take into account complex orbital mechanics to establish a connection with their target. Other aspects of the competition will be more familiar.
“It's still essentially a computer,” says Bernert. “You still have to apply all the cyber security principles. Now, it's just in a more rigorous domain.”
Cyber attack innovation
To communicate with the satellite in orbit, teams will use the same ground stations that are used for ordinary satellites. Moonlighter has been sandboxed so that even though the satellite is in space, nothing too dramatic can be compromised.
“It works just like any other satellite would work in Low Earth Orbit,” says Bernert. “We don't have a propulsion system on it, so they won't be able to just send it off into deep space or into the Earth's atmosphere.” The satellite also has a built-in “reset” button that the military can use to restore the sandbox to a blank slate.
The competition is as realistic as possible and the organizers urge teams to pick members who have skills in the different disciplines such a complex hacking task requires, including radio communications, exploit development, satellite operations. and astrophysics.
Bernert is confident that by tapping into this “untraditional” pool of individuals, the task can be solved in innovative ways. But even with the right people, winning the competition will require an effective strategy.
“We let the competitors get creative with how they want to go about denying or degrading their competitors' satellites, but we also give them the opportunity to have game theory get involved,” says Bernert, describing how teams will have to choose between playing aggressively, to capture their opponents’ flags, or as in a real cyber-conflict, choosing to play more defensively to protect their own.

Even after the winners have been crowned and the Moonlighter satellite has been successfully compromised, the real-world stakes of the competition remain very much front of mind for those participating. Bernert’s hope, and that of Space Force, is that this can put threats to critical infrastructure in context.
“People are realising that it's not just limited to specific nations with large military budgets – it's becoming a lot more proliferated and more accessible to everybody,” he says.
“With that, obviously, comes the need to make sure that systems that are now being procured and launched in rapid quantities are cyber secure, because so much of our lives for pretty much everybody across the globe is tied directly to safe satellite vehicle operations.”
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 OpenAI to pay up to $20k in rewards through new bug bounty program
OpenAI to pay up to $20k in rewards through new bug bounty programNews The move follows a period of unrest over data security concerns
-
 New ‘DarkBit’ ransomware gang shuts down Technion, demands $1.7 million ransom
New ‘DarkBit’ ransomware gang shuts down Technion, demands $1.7 million ransomNews A politically charged ransom note suggests DarkBit are one of the newest hacktivist gangs to emerge in recent months
-
 Research: Luxury cars and emergency services vehicles vulnerable to remote takeover
Research: Luxury cars and emergency services vehicles vulnerable to remote takeoverNews A "global API issue" has been highlighted through months-long research into brands such as Ferrari and Mercedes-Benz, leaving owners open to hacking, account takeovers, and more
-
 Podcast transcript: Meet the cyborg hacker
Podcast transcript: Meet the cyborg hackerIT Pro Podcast Read the full transcript for this episode of the IT Pro Podcast
-
 The IT Pro Podcast: Meet the cyborg hacker
The IT Pro Podcast: Meet the cyborg hackerIT Pro Podcast Resistance is futile - offensive biotech implants are already here
-
 SpaceX bug bounty offers up to $25,000 per Starlink exploit
SpaceX bug bounty offers up to $25,000 per Starlink exploitNews The spacecraft manufacturer has offered white hats immunity to exploit a wide range of Starlink systems, with a dedicated report page
-
 Nomad happy to forgive hackers if they return 90% of $190 million that was stolen
Nomad happy to forgive hackers if they return 90% of $190 million that was stolenNews The crypto bridge is offering 'white hat hackers' a 10% bounty following the attack earlier this week
-
 HackerOne employee fired for using position to steal bug bounties
HackerOne employee fired for using position to steal bug bountiesNews The threat actor was identified by their duplicate data, which they were trying to pass off as their own for financial gain