Big zero-day flaw found in Palo Alto security appliance
Vulnerability in GlobalProtect VPN could enable hackers to take control of the security system


Security researchers have said that a zero-day flaw in a security appliance from Palo Alto Networks could affect around 10,000 servers running the product.
Researchers at cyber security firm Randori said that flaw, tracked as CVE-2021-3064, affected PAN firewalls using the GlobalProtect Portal VPN and allowed for unauthenticated remote code execution on vulnerable product installations.
They added that the problem affected multiple versions of PAN-OS 8.1 before 8.1.17. Researchers found numerous vulnerable instances exposed on internet-facing assets, more than 10,000 assets.
“Our team was able to gain a shell on the affected target, access sensitive configuration data, extract credentials, and more. Once an attacker has control over the firewall, they will have visibility into the internal network and can proceed to move laterally,” said researchers.
Researchers developed a reliable working exploit and leveraged the capability as part of their red team products. The flaw was discovered over a year ago.
The bug is a buffer overflow that occurs while parsing user-supplied input into a fixed-length location on the stack. The problematic code is not reachable externally without using an HTTP-smuggling technique, according to researchers.
They added that the exploitation of these together yields remote code execution under the privileges of the affected component on the firewall device. “The smuggling capability was not designated a CVE identifier as it is not considered a security boundary by the affected vendor,” added researchers.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
An attacker must have network access to the device on the GlobalProtect service port (default port 443) to exploit this vulnerability. As the affected product is a VPN portal, this port is often accessible over the internet, said researchers.
Exploitation is difficult but possible on devices with ASLR enabled, which is the case in most hardware devices. On virtualized devices — VM-series firewalls — exploitation is significantly easier due to lack of ASLR and Randori expects public exploits will surface.
“Randori researchers have not exploited the buffer overflow to result in controlled code execution on certain hardware device versions with MIPS-based management plane CPUs due to their big-endian architecture, though the overflow is reachable on these devices and can be exploited to limit availability of services,” they added.
The company said to avoid enabling misuse of the flaw, it will withhold the technical details related to CVE-2021-3064 from public dissemination for 30 days after the publication of the blog post on the subject.
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
 European Commission opens public consultation on draft for high-risk AI guidelines
European Commission opens public consultation on draft for high-risk AI guidelinesNews Guidance aims to help organizations and regulators decide whether their AI products and deployments need to conform to tougher rules
-
 Microsoft reveals Surface Pro and Surface Laptop for Business
Microsoft reveals Surface Pro and Surface Laptop for BusinessNews New 13in Pro and Laptop claim big performance improvements and vast AI capabilities
-
 Okta and Palo Alto Networks are teaming up to ‘fight AI with AI’
Okta and Palo Alto Networks are teaming up to ‘fight AI with AI’News The expanded partnership aims to help shore up identity security as attackers increasingly target user credentials
-

 Sophos XGS 116 review: A small and mighty appliance
Sophos XGS 116 review: A small and mighty applianceReviews This clever and compact security gateway brings outstanding security and remote management features at a tempting price
-

 WatchGuard Firebox M290 review: Stiff security at a great price
WatchGuard Firebox M290 review: Stiff security at a great priceReviews The Firebox M290 delivers an incredible range of gateway security measures priced right for SMBs
-
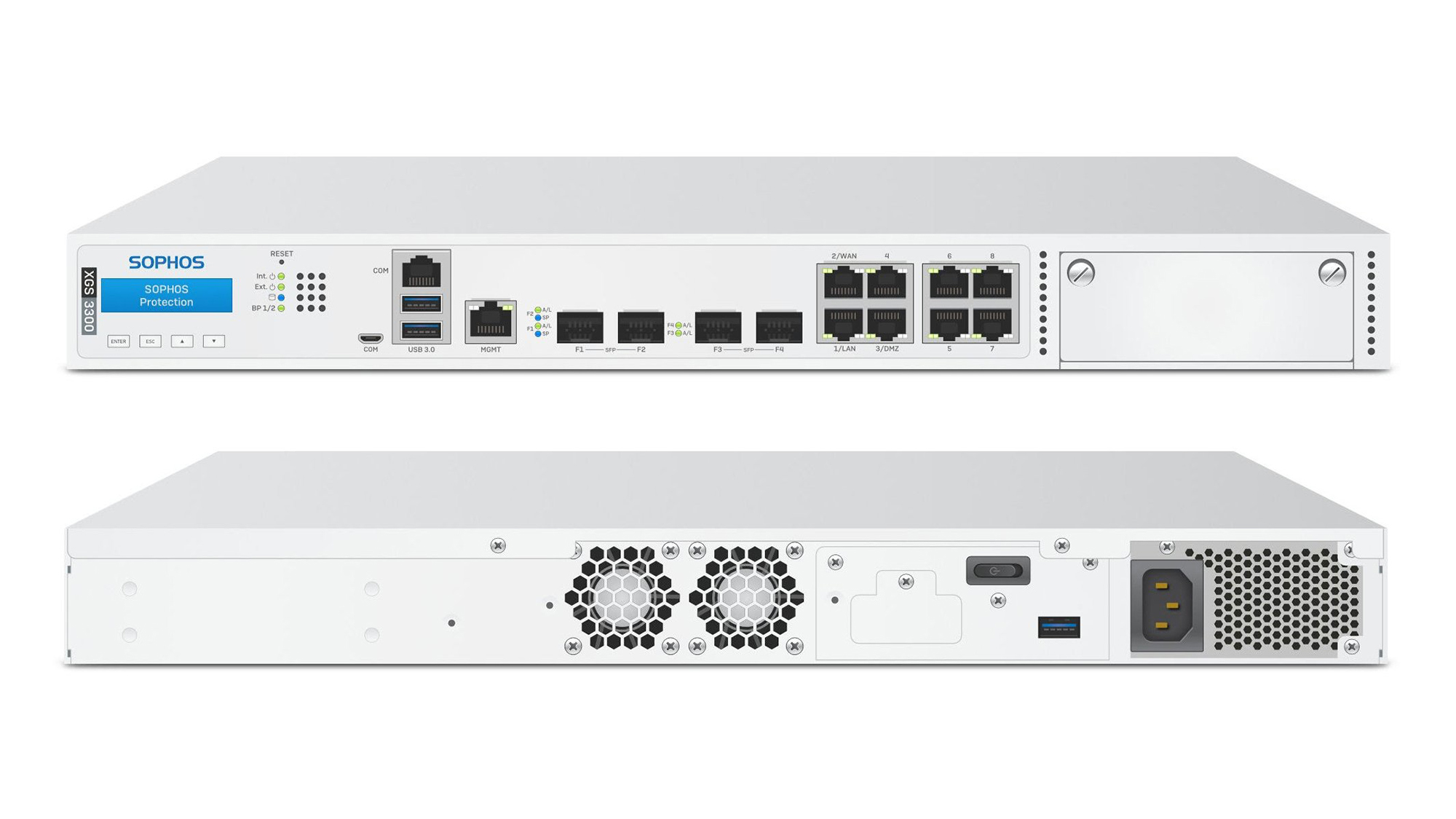
 Sophos XGS 3300 review: Xstream firewall performance
Sophos XGS 3300 review: Xstream firewall performanceReviews A powerful firewall appliance combining hardware acceleration with a vast array of security measures
-

 Ubiquiti Networks UniFi Dream Machine Pro review: All the security you need in one handy box
Ubiquiti Networks UniFi Dream Machine Pro review: All the security you need in one handy boxReviews An affordable security gateway that can take care of a wide range of security needs
-
 SonicWall warns of imminent ransomware campaign on VPN hardware
SonicWall warns of imminent ransomware campaign on VPN hardwareNews Current and legacy secure VPN appliances under attack now
-
 Zyxel USG Flex 100 review: Flexible gateway security
Zyxel USG Flex 100 review: Flexible gateway securityReviews Perfect for SMBs, with the promise of cloud management coming soon
-
 Veritas Access Appliance with IBM Spectrum® Protect
Veritas Access Appliance with IBM Spectrum® ProtectWhitepapers Backup, archive, and long-term retention solution

