Hackers abuse single bit change in Intel CPU register to evade detection
Palo Alto Networks discovers that Trap Flag is being abused to notify malware it is being analyzed


Security researchers have discovered a specific single bit (Trap Flag) in the Intel CPU register that malware can abuse to evade sandbox detection.
According to researchers at Palo Alto Networks’ Unit 42 threat research group, malware can detect whether it is executing in a physical or virtual machine (VM) by monitoring the response of the CPU after setting this single bit.
Malware usually avoids detection by checking if it is being run in a virtualized “sandbox” environment set up to safely analyze potential malware. When the malware finds out it is executing in a virtual machine, it will terminate its execution or provide fake outputs to hide its real intentions.
In this instance, to detect VM use in a sandbox, malware could check the CPU’s behavior after enabling the trap flag. This is the eighth single bit in the EFLAGs register of the Intel x86 CPU architecture.
If the trap flag is enabled before a single instruction is executed, the CPU will raise an exception (single-step mode) after the instruction is completed. This exception stops the CPU execution to allow the exception handler to examine the contents of the registers and memory location. Before allowing code execution to continue, the CPU must also clear the trap flag.
“To determine whether a VM is used, malware can check whether the single-step exception was delivered to the correct CPU instruction, after executing specific instructions (e.g. CPUID, RDTSC, IN) that cause the VM to exit with the TF enabled. During VM exits, the hypervisor – also known as Virtual Machine Monitor (VMM) – will emulate the effects of the physical CPU it encounters,” said researchers.
Researchers also said there was an ongoing cat-and-mouse game between malware authors crafting evasion techniques to prevent effective analysis and sandbox authors researching novel ways to defeat those evasions.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
RELATED RESOURCE
2021 IBM Security X-Force Insider Threat Report
Top discovery methods and recommendations for insider attacks
“This is one of the main drivers that led us at Palo Alto Networks to build our own custom hypervisor for malware analysis. Since we have full control over the software stack, including the virtualization layer, we can react to new and emerging threats,” said researchers.
“In this particular case, once we had identified the issue with the incorrect emulation of the trap flag, our hypervisor team was able to test and deploy a fix.”
Researchers have since been able to fix this evasion problem for any malware sample by deploying this technique.
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
 Laid off Intel engineer accused of stealing 18,000 files on the way out
Laid off Intel engineer accused of stealing 18,000 files on the way outNews Intel wants the files back, so it's filed a lawsuit claiming $250,000 in damages
-
 PowerEdge - Cyber resilient infrastructure for a Zero Trust world
PowerEdge - Cyber resilient infrastructure for a Zero Trust worldWhitepaper Combat threats with an in-depth security stance focused on data security
-
 Redefining modern enterprise storage for mission-critical workloads
Redefining modern enterprise storage for mission-critical workloadsWhitepaper Evolving technology to meet the mission-critical needs of the most demanding IT environments
-
 The business value of storage solutions from Dell Technologies
The business value of storage solutions from Dell TechnologiesWhitepaper Streamline your IT infrastructure while meeting the demands of digital transformation
-
 Cyber resiliency and end-user performance
Cyber resiliency and end-user performanceWhitepaper Reduce risk and deliver greater business success with cyber-resilience capabilities
-
 Intel Alder Lake chips safe from novel exploits following source code leak, experts say
Intel Alder Lake chips safe from novel exploits following source code leak, experts sayNews The mystery surrounding how the code was leaked is a more interesting story, experts told IT Pro, despite others branding the incident "scary"
-
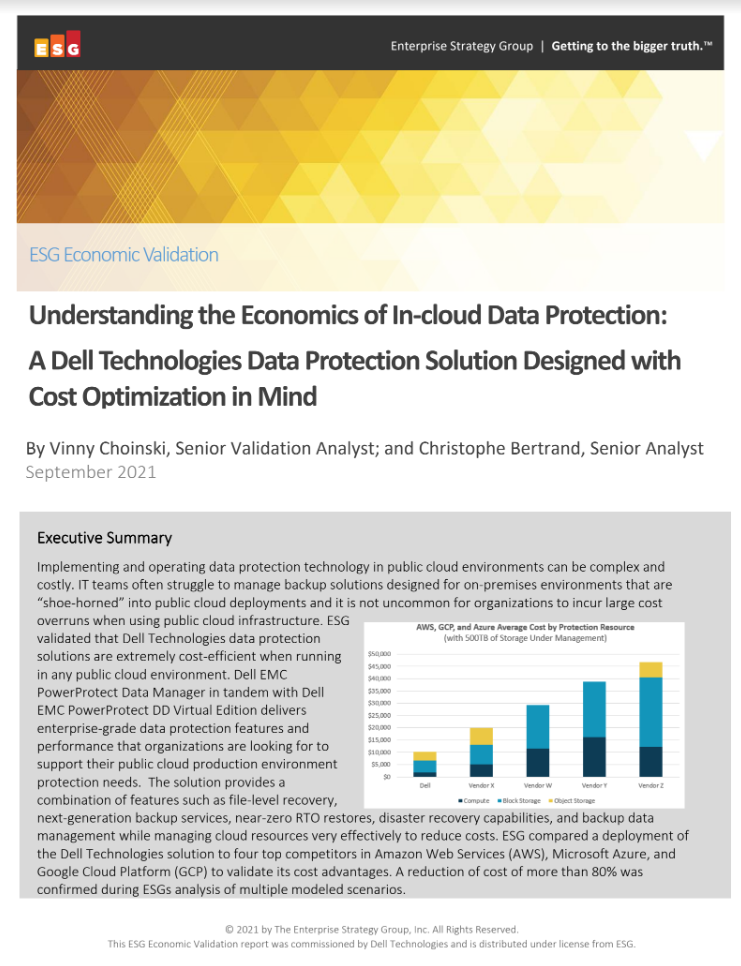 Understanding the economics of in-cloud data protection
Understanding the economics of in-cloud data protectionWhitepaper Data protection solutions designed with cost optimisation in mind
-
 Intel expands its bug bounty program with Project Circuit Breaker
Intel expands its bug bounty program with Project Circuit BreakerNews The initiative aims to address vulnerabilities in Intel’s firmware, GPUs, hypervisors, and chipsets



