GitHub alerts users to active phishing campaign
The attack revolves around counterfeit CircleCI notifications urging users to accept updated terms of use and privacy policy

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
GitHub has notified its users of a phishing campaign active since 16 September.
The bait in the seemingly persuasive phishing campaign is an email that mimics notifications from continuous integration and delivery platform CircleCI.
RELATED RESOURCE
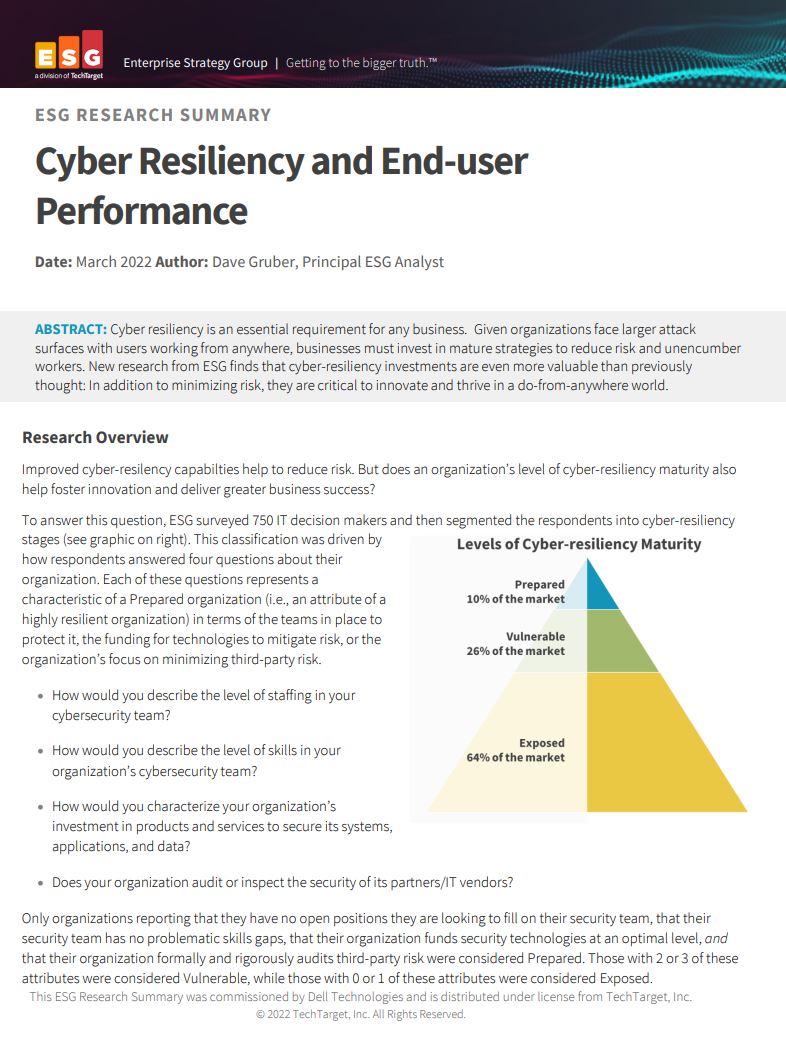
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
Specifically, the fake email coerces recipients to accept updated “user terms and privacy policy” by signing into their GitHub accounts again through CircleCI.
“As part of our integration with GitHub, we are updating our Terms of Use and Privacy Policy to provide greater transparency about how CircleCI uses your information, as well as how cookies are used to make our services more convenient and effective,” the email reads.
By relaying credentials through reverse proxies, the threat actors attempted to steal GitHub account credentials, including two-factor authentication (2FA) codes.
However, GitHub assured accounts protected with hardware security keys for multi-factor authentication (MFA) are not susceptible to the attack.
“While GitHub itself was not affected, the campaign has impacted many victim organizations,” GitHub informed in an advisory on Wednesday.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Corroborating GitHub’s alert, CircleCI took to its forums to warn users that the platform would never ask users to enter credentials to view changes in its terms of service.
“Any emails from CircleCI should only include links to circleci.com or its sub-domains,” stated CircleCI in its notice.
“If you believe you or someone on your team may have accidentally clicked a link in this email, please immediately rotate your credentials for both GitHub and CircleCI, and audit your systems for any unauthorized activity,” added the company.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 Brace yourselves for a vulnerability explosion, Forescout warns
Brace yourselves for a vulnerability explosion, Forescout warnsNews AI advances are helping identify software flaws at record pace and scale, but that's not the good news some would think
-
 Ubuntu vulnerability exposes enterprises to root escalation, complete system compromise
Ubuntu vulnerability exposes enterprises to root escalation, complete system compromiseNews The high-severity Ubuntu vulnerability allows an unprivileged local attacker to escalate privileges through the interaction of two standard system components
-
 Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerability
Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerabilityNews Threat actors have been exploiting the vulnerability to achieve root access since 2023
-
 Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourself
Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourselfNews The VS Code vulnerabilities highlight broader IDE security risks, said OX Security
-
 CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaught
CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaughtNews While the CVE figures might be daunting, they won't all be relevant to your organization
-
 Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to know
Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to knowNews Patch Tuesday update targets large number of vulnerabilities already being used by attackers
-
 Experts welcome EU-led alternative to MITRE's vulnerability tracking scheme
Experts welcome EU-led alternative to MITRE's vulnerability tracking schemeNews The EU-led framework will reduce reliance on US-based MITRE vulnerability reporting database
-
 Veeam patches Backup & Replication vulnerabilities, urges users to update
Veeam patches Backup & Replication vulnerabilities, urges users to updateNews The vulnerabilities affect Veeam Backup & Replication 13.0.1.180 and all earlier version 13 builds – but not previous versions.