Microsoft warns full scope of Ukraine cyber attacks ‘not fully realised’
The company's investigation into the attacks targeting Ukraine revealed atypical characteristics of the "destructive" campaign that disguises itself as ransomware


Microsoft has investigated the cyber attacks in Ukraine and revealed evidence of a targeted malware campaign that disguises itself as ransomware, but offers no recourse for victims to recover their data.
The so-called 'fake ransomware' was examined by Microsoft's Threat Intelligence Center (MSTIC), which concluded that the "destructive malware" was designed to render targeted machines inoperable rather than to attract a ransom payment.
Microsoft's analysis of the malware revealed other inconsistencies between it and traditional ransomware. While a ransom sum and cryptocurrency wallet address are provided, the way in which the malware is designed means victims wouldn't be able to recover their data even if they did pay to $10,000 ransom demanded in the note.
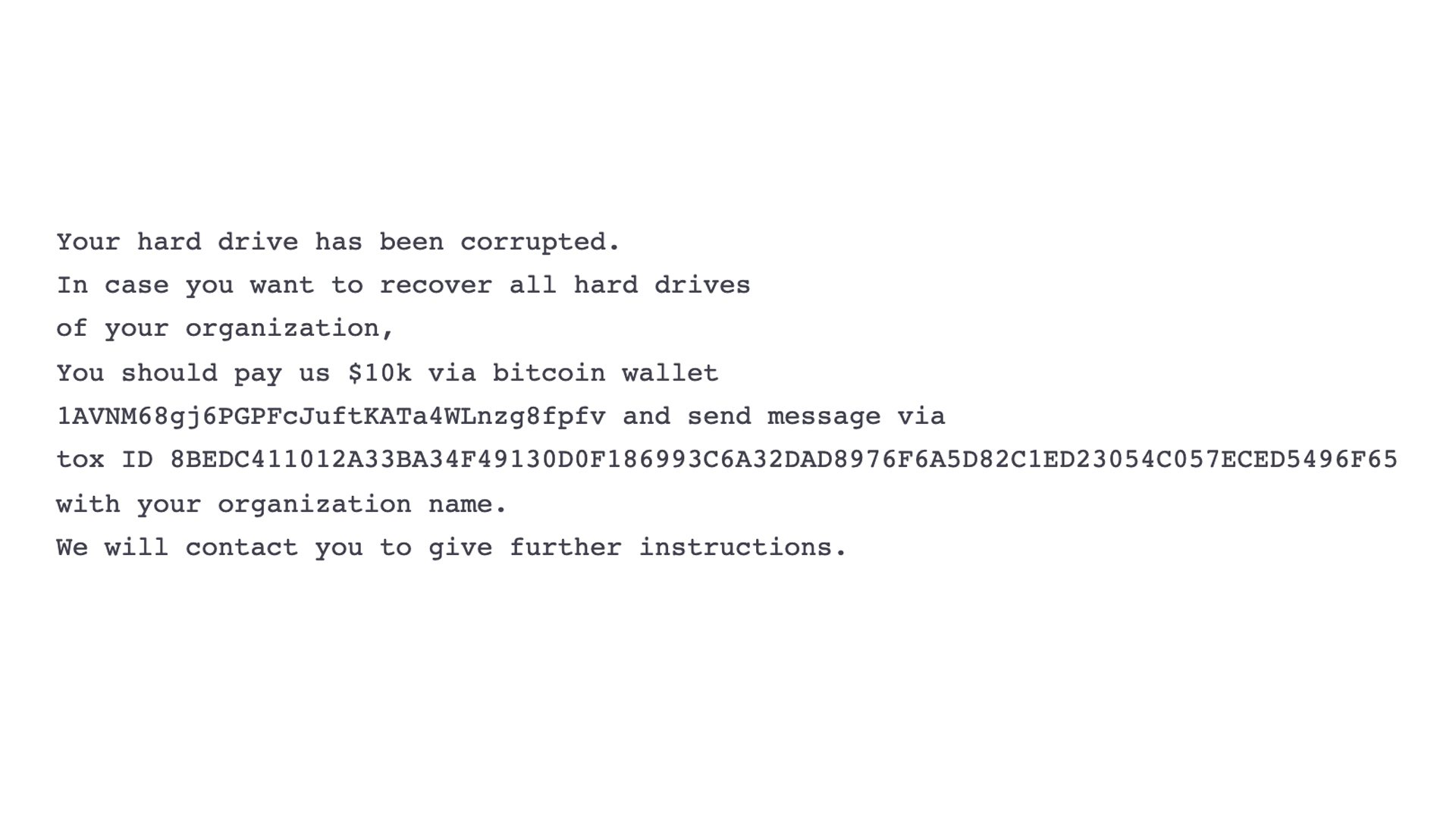
MSTIC said the malware works by overwriting the Master Boot Record (MBR) on victim systems, leaving a ransom note (above). The MBR is the part of a hard drive that tells the computer how to load its operating system.
Overwriting the MBR is not common with financially motivated ransomware operators since a destructed MBR means files are destroyed with no mechanism for recovery. If this were the case with typical ransomware, there would be no motivation to pay.
Other differences between the malware hitting Ukraine and ransomware include a uniform ransom demand - usually these are tailored to each victim, a lack of customer ID number in the note, and the communication method being over the Tox encrypted messaging protocol - usually victims are directed to a dark web site owned by the ransomware operator where they can seek support.
The investigation into the attack is ongoing but MSTIC suggested the current malware infection may continue to spread beyond the "dozens" of machines that are already affected. Said machines span sectors including government, non-profits, and IT organisations.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
MSTIC also said it's currently unsure at what stage in the attackers' operational cycle they're currently or how many other victims there may be across the country, but the scale of the attack most likely isn't fully realised at present.
"Given the scale of the observed intrusions, MSTIC is not able to assess intent of the identified destructive actions but does believe these actions represent an elevated risk to any government agency, non-profit or enterprise located or with systems in Ukraine," said MSTIC in a blog post.
"We strongly encourage all organisations to immediately conduct a thorough investigation and to implement defences using the information provided in this post. MSTIC will update this blog as we have additional information to share."
Geopolitical tensions in the region
RELATED RESOURCE
The revelations shed more light on the issue first reported last week and follow a lengthy period of unproductive talks, held recently in Geneva, between the US and Russia on the topic of Ukraine.
Most recently, Ukraine officials have said they believe Belarus, a close ally of Russia, is behind the wave of cyber attacks on the nation, adding that the malware used bears resemblance to similar strains previously used by Russian intelligence, Reuters reported.
Ukraine and Russia have been locked in a war over territory since 2014 and there are strong fears that Russia, which has amassed troops at the Ukrainian border, may invade Ukraine as a result of the conflict.
Russia is desperately trying to prevent Ukraine from joining European institutions such as Nato, a demand the West rejects. A war between the two nations is not thought to be imminent, but tensions are arguably at the highest they have been in decades.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwise
The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwiseNews Billing itself as the “only place ransomware allowed", RAMP catered mainly for Russian-speaking cyber criminals

