Double extortion ransomware pushes average payments close to $1 million
As the average payment approaches the landmark figure, experts reflect on times when the going rate was just $500


The average ransomware payment has risen 71% this year and is close to reaching $1 million, experts have said.
In ransomware cases that have been assisted by incident responders at cyber security company Unit 42 of Palo Alto Networks, the average ransom paid was $925,162 in the first five months of 2022.
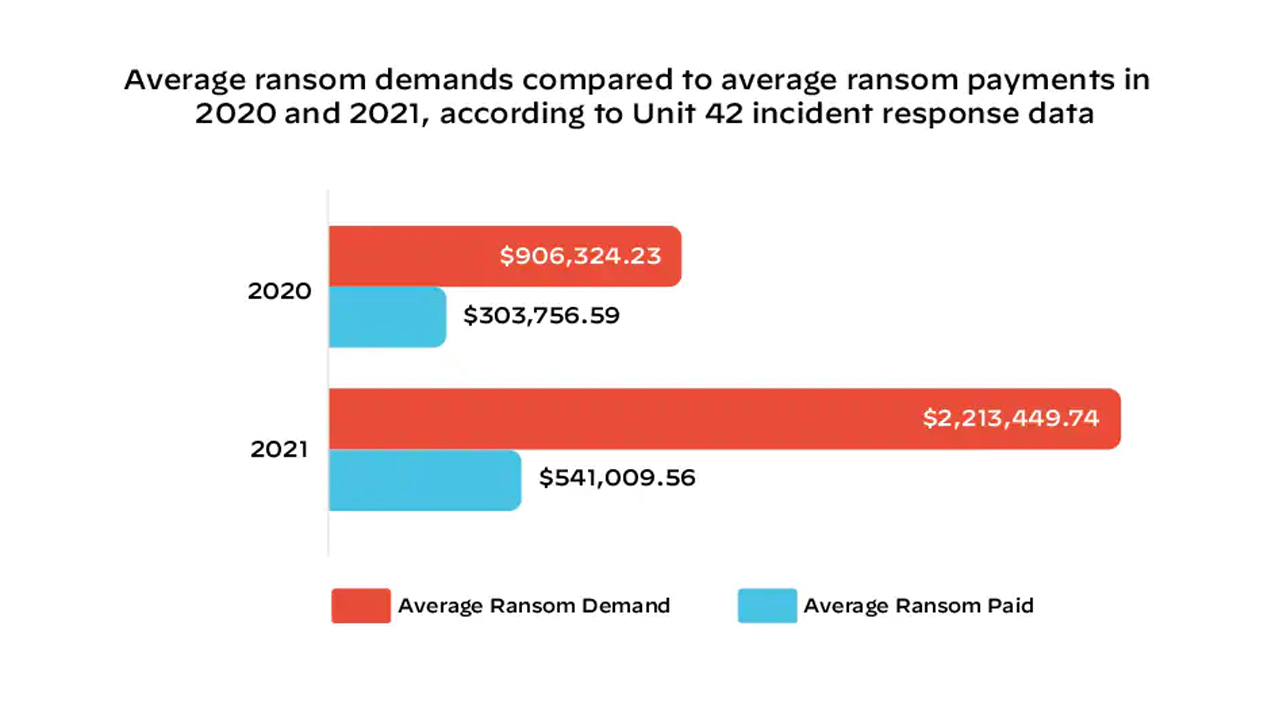
This represents a steep and “startling” rise from figures of previous years when average ransom payments were $541,009 and $303,756 in 2021 and 2020 respectively, said Ryan Olson, vice president of threat intelligence at Unit 42 in a blog post.
As recently as 2016, the company’s incident responders were seeing payments of just $500, and the rise of double extortion models has placed added pressure on organisations to pay ransom demands.
Double extortion ransomware has become a popular operational model in recent years as companies are increasingly vigilant to ransomware attacks and are keeping better backups to avoid having to pay ransom demands.
The model sees attackers infecting a corporate network with ransomware, locking users out of machines as usual, but exfiltrates sensitive data before the infection chain begins, threatening to leak the data if the ransom isn’t paid.
This places additional pressure on companies to maintain their reputation with customers and from a regulatory perspective for companies bound by stringent data protection laws like GDPR.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
“Details of about seven new victims on average are posted each day on the dark web leak sites that ransomware gangs use to coerce victims into paying ransoms,” said Olson. “The rate of double extortion we’ve observed translates into one new victim every three to four hours.
“The cyber extortion crisis continues because cybercriminals have been relentless in their introduction of increasingly sophisticated attack tools, extortion techniques and marketing campaigns that have fueled this unprecedented, global digital crime spree,” he added. “Their ransomware-as-a-service (RaaS) business model has at the same time lowered the technical bar for entry by making these powerful tools accessible to wannabe cyber extortionists with easy-to-use interfaces and online support.”
Unit 42 has observed two instances of multi-million-dollar ransoms being paid this year, driven by the success of the Quantum Locker and LockBit 2.0 ransomware operations.
RELATED RESOURCE
The Total Economic Impact™ of Mimecast
Cost savings and business benefits enabled by using Mimecast with Microsoft 365
FREE DOWNLOAD
Companies that could be put out of business if they don’t pay the ransom will continue to be targeted, the researcher said, and it’s in these cases where the huge ransom demands will again be issued.
Olson cited Costa Rica as an example of how devastating ransomware can still be in 2022, five years on from WannaCry and six years after the average ransom demand was in the region of $500 - a pittance in today’s threat landscape.
The country has declared a state of emergency after it sustained an attack from the Conti ransomware and has since had a second ransomware gang targeting the country, this time focusing on its health service.
According to a separate report from Digital Shadows, the first quarter of 2022 saw a 25% decrease in ransomware activity compared to the previous quarter.
The company said the decrease in activity could be a result of a less prominent threat of the larger, more organised ransomware groups that have shuttered in recent months, such as REvil and BlackMatter.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Ransomware negotiator sentenced for role in major cyber crime group
Ransomware negotiator sentenced for role in major cyber crime groupNews Deniss Zolotarjovs was a key player in a group associated with Conti
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites


