Ransomware activity falls 25% in Q1 2022
The drop in ransomware has been attributed to larger ransomware gangs being less active compared to the end of 2021


The number of ransomware attacks dropped significantly during the first quarter of 2022, according to new research published this week.
Ransomware is still one of the biggest cyber security threats businesses are facing, but the number of organisations named in ransomware attacks has fallen 25.3% compared to Q4 2021.
A total of 582 organisations were named by ransomware groups on their sites this quarter, according to Digital Shadows, which conducted the research.
The security company said the decrease in activity can be attributed, in part, to a less prominent threat of larger ransomware groups so far this year.
Conti, one of the most prolific ransomware groups of recent years, was found to have claimed 31.8% fewer victims compared to the previous quarter. The PYSA group has so far listed no new corporate victims in 2022.
The same can’t be said for the operators of LockBit 2.0, though. The group has been highly active this year, claiming the majority of ransomware victims, Digital Shadows said.
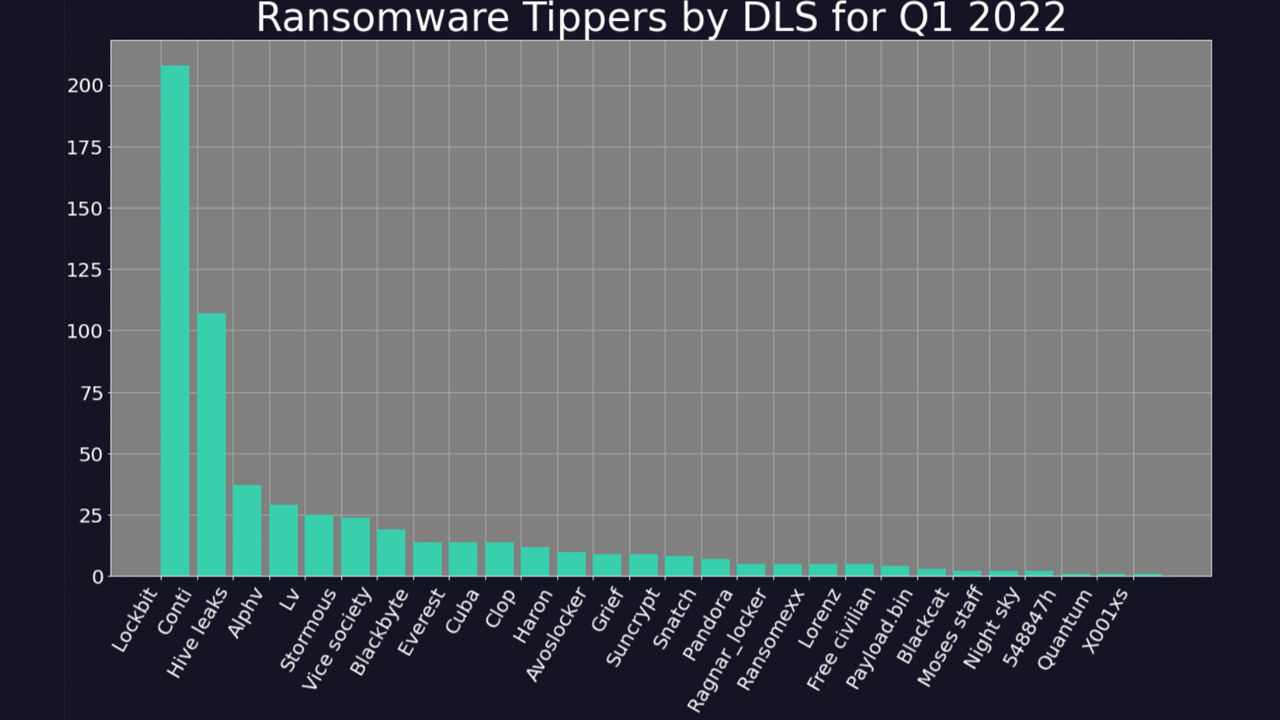
Conti is still the second-most active group of the year, according to the security company’s data, with both it and LockBit 2.0 accounting for more than half of all ransomware success so far this year.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Ransomware groups have also changed their strategy in recent months, as the national security agencies of the US, UK, and Australia have noted.
Cyber criminals are shifting away from the ‘big game hunting’ approach to ransomware after the double extortion model became popularised with attacks on larger businesses in 2020.
Ransomware groups are now shifting their focus to medium-sized companies after a string of high-profile attacks throughout 2021 led to heightened international pressure to disrupt and unearth ransomware groups like REvil, which was behind the supply chain attack on Kaseya.
Despite the first quarter of 2021 showing signs of a slower ransomware market, cyber criminals have been hard at work in other areas.
Conti’s lack of action could have been affected by a Ukrainian security researcher leaking the group’s tools and internal communications in retaliation for the group’s public support of Russia’s invasion of Ukraine.
The invasion has also spurred cyber attackers from across the world to help support the fight against Russia in cyber space. Distributed denial of service (DDoS) attacks are among the most common types of cyber attacks being launched against Russia, at the command of Ukraine’s IT Army.
Anonymous has also claimed to have successfully executed a number of attacks against Russia since the war started, including injecting footage from inside Ukraine to Russian television streams.
The LAPSUS$ hackers were among the most prominent cyber criminals of the year so far and were at first confused with a ransomware gang, but later analysis of its attacks showed the group operated on a pure extortion model.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Enterprises flock to AI PCs amid sharpened workforce productivity focus
Enterprises flock to AI PCs amid sharpened workforce productivity focusNews Leaders are adopting AI PCs to stay competitive and improve employee productivity
-
 Google Cloud is more confident than ever in its AI strength, from hardware to software
Google Cloud is more confident than ever in its AI strength, from hardware to softwareOpinion With a commitment to interoperability and open data connections, Google Cloud is daring its customers to find a more comprehensive AI suite on the market
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwise
The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwiseNews Billing itself as the “only place ransomware allowed", RAMP catered mainly for Russian-speaking cyber criminals