Encryption-less ransomware: Warning issued over emerging attack method for threat actors
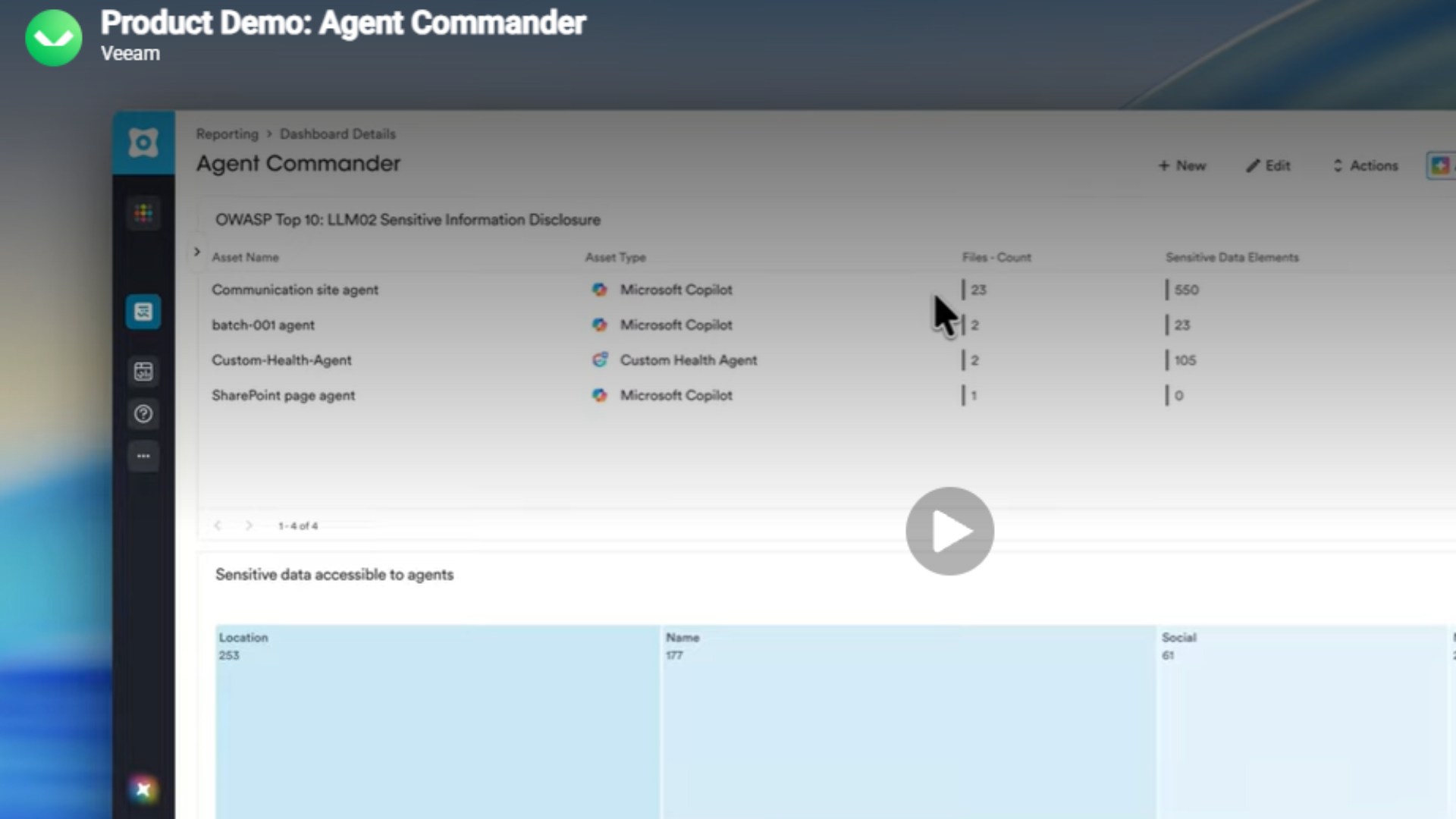
Researchers at Zscaler have observed a marked increase in the frequency of encryption-less ransomware attacks over the last year


Security researchers have issued a warning over the growing threat of encryption-less ransomware amid a period of evolving threats by sophisticated hacker groups.
Analysis from Zscaler revealed there has been a 40% increase in ransomware attacks over the last year and identified encryption-less ransomware techniques as “one of the most noteworthy trends” now observed among threat actors.
Across the year, 25 new ransomware families were identified using either double extortion or encryption-less techniques, highlighting the growing popularity of this method among cyber criminals.
“In 2021, ThreatLabz observed 19 ransomware families that adopted double or multi-extortion approaches to their cyber attacks. This has since grown to 44 ransomware families observed,” the firm said.
Encryption-less ransomware attacks originally began with groups like Babuk and SnapMC, Zscaler’s study said. However, researchers have observed a host of new groups adopting this method, including RansomHouse, BianLian, and Karakurt.
What is encryption-less ransomware?
Encryption-less ransomware attacks differ in technique from traditional methods, whereby threat actors compromise an organization, encrypt data, and demand a ransom for its recovery on the threat of publicly releasing stolen data.
This technique, also known as ‘extortion-only’ attacks, essentially skips over the process of encryption, Zscaler said, while still maintaining the tactic of threatening to leak victims’ data online if they don’t pay.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
RELATED RESOURCE
In doing this, threat actors are able to skip a laborious part of the attack process - encryption - while still achieving the same overall results and often generating larger profits from an attack.
Developing effective encryptor payloads also requires a level of software engineering expertise that may dissuade cyber criminals from considering ransomware operations.
“This tactic results in faster and larger profits for ransomware gangs by eliminating software development cycles and decryption support,” Zscaler said.
Among the most prolific groups currently employing this attack method is BianLian, according to research from LogPoint.
Analysis of the hacker group’s operations in recent months shows that it has pivoted away from double extortion methods due to the emergence of publicly available decryptor tools, such as those released by Avast.
“Upon the public release of a decryptor from Avast in January 2023, the group resorted to an intensified extortion-only modus operandi, with no system encryption,” the security firm said.
Other groups known to have employed an extortion-only model in recent years include LAPSUS$ and the infamous Cl0p ransomware outfit.
During the GoAnywhere breach, Cl0p deviated from its traditional double extortion tactic and opted for a pure extortion attack.
It was also observed employing the pure extortion method during the MOVEit breach earlier this month which is believed to have affected numerous other organizations in what is the second major supply chain attack of the year.
Hackers ‘flying under the radar’ with encryption-less ransomware
Deepen Desai, global CISO and head of security research at Zscaler, said the growing trend of encryption-less ransomware techniques is enabling threat actors to operate unseen and often with impunity.
“Ransomware authors are increasingly staying under the radar by launching encryption-less attacks which involve large volumes of data exfiltration,” he said.
Although victims are still severely impacted by these attacks and incur significant financial burdens, the technique is often harder to detect and receives less attention from authorities because they do not lock files and systems.
Similarly, this method results in less downtime for affected organizations faced with a lengthy recovery process.
This lesser rate of disruption means that victims are less likely to report incidents, Zscaler warned.
“Encryption-less extortion attacks tend to not disrupt their victims’ business operations - which subsequently results in lower reporting rates.”

Ross Kelly is ITPro's News & Analysis Editor, responsible for leading the brand's news output and in-depth reporting on the latest stories from across the business technology landscape. Ross was previously a Staff Writer, during which time he developed a keen interest in cyber security, business leadership, and emerging technologies.
He graduated from Edinburgh Napier University in 2016 with a BA (Hons) in Journalism, and joined ITPro in 2022 after four years working in technology conference research.
For news pitches, you can contact Ross at ross.kelly@futurenet.com, or on Twitter and LinkedIn.
-
 New ransomware threat group, The Gentlemen, has become one of the most active ransomware operators, accounting for 10% of all attacks
New ransomware threat group, The Gentlemen, has become one of the most active ransomware operators, accounting for 10% of all attacksNews NTT researchers warn that the RaaS group is leveraging SystemBC malware to establish covert tunnelling, evade detection, and support rapid lateral movement across enterprise environments
-
 Instructure chose to a pay ransom following the Canvas cyber attack – research shows more than half of security leaders would follow suit
Instructure chose to a pay ransom following the Canvas cyber attack – research shows more than half of security leaders would follow suitAnalysis Opting to pay ransoms creates huge risks for enterprises – you’re relying on the word of criminals
-
 Ransomware negotiator sentenced for role in major cyber crime group
Ransomware negotiator sentenced for role in major cyber crime groupNews Deniss Zolotarjovs was a key player in a group associated with Conti
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Cyber resilience tunnel vision is leaving enterprises open to external threats
Cyber resilience tunnel vision is leaving enterprises open to external threatsNews Many enterprises are overlooking supply chain risks as part of their cyber resilience strategies