Bluetooth advocacy group warns of critical encryption exploit
The vulnerability allows third-parties to overwrite the key used to establish a link between two devices

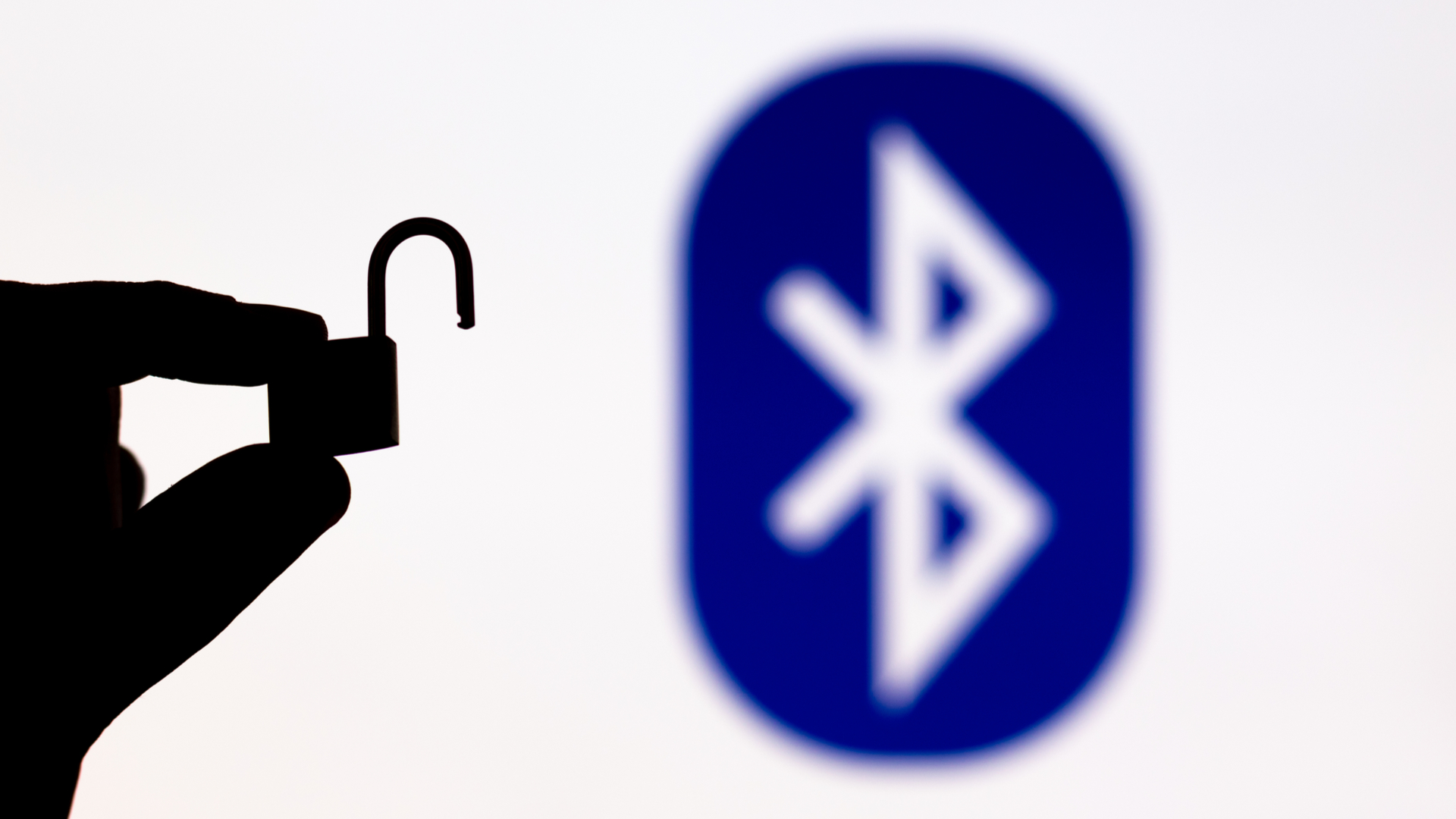
Certain configurations of Bluetooth 4.2 to 5.0 on dual-mode devices contain a flaw that could allow hackers to conduct 'man in the middle' (MITM) attacks or overwrite encryption keys.
Known as BLURtooth, the vulnerability assigned CVE-2020-15802 can be found on devices supporting both Bluetooth Basic Rate/Enhanced Data Rate (BR/EDR) transportation methods as well as Low Energy (LE) connections.
Although an alert, published by Carnegie Melon University, doesn't specify which particular devices are affected, a number of widely-available dual-mode devices fall into the bracket, including the Dynabook Portégé X30L-G business notebook, the Nokia 5.3 smartphone, and the Sonos Move wireless speaker system.
The flaw lies in the pairing mechanism in these dual-band Bluetooth devices, with the vulnerability allowing third-parties to overwrite the key used to establish a link between two devices. The vulnerability, and the group of viable attacks, categorised as BLUR, was first discovered by academics with École Polytechnique Fédérale de Lausanne (EPFL) and Purdue University.
“The researches identified that CTKD, when implemented to older versions of the specification, may permit escalation of access between the two transports with non-authenticated encryption keys replacing authenticated keys or weaker encryption keys replacing stronger encryption keys,” according to the Bluetooth Special Interest Group (SIG).
BLURtooth mainly affects devices that use the Cross-Transport Key Derivation (CRKD) mechanism for Bluetooth pairing. The fault may allow an attacker to reduce the strength of the encryption key, or overwrite an authenticated key with an unauthenticated key in order to gain access to profiles or services.
To conduct successful attacks, a hacker must be within wireless range of a vulnerable Bluetooth device that supports CTKD connections and supports pairing either with no authentication or no access restrictions on pairing.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
An attacker spoofing another device’s identity may bond with the vulnerable device and derive a key through the CTKD mechanism that overwrites a pre-existing encryption key of much greater strength. In doing so, the attacker can access authenticated services, or conduct a MITM attack in future between devices that were previously bonded.
BLURtooth is the latest serious Bluetooth vulnerability to be recognised by the Bluetooth SIG in recent months after the organisation was forced to update the core specification following the discovery of BIAS in May 2020.
Also centred on devices using BR/EDR, the Bluetooth Impersonation Attacks (BIAS) flaw allowed attackers to break security mechanisms and impersonate one device in a pair after a bond has been established.
RELATED RESOURCE
The State of Email Security 2020
Email security insights at your email perimeter, inside your organisation, and beyond
BIAS can also work in conjunction with other attacks, such as the Key Negotiation of Bluetooth (KNOB) attack, which allowed hackers to brute force watered-down encryption keys and intercept data transmitted between devices.
Bluetooth SIG has recommended that potentially vulnerable devices should be updated with the restrictions placed on CTKD, as mandated by the Bluetooth Core Specification version 5.1 and beyond.
The details of the vulnerability are also being relayed to members of the organisation, which includes hundreds of device manufacturers, with these members encouraged to rapidly integrate any patches as and when they become available.

Keumars Afifi-Sabet is a writer and editor that specialises in public sector, cyber security, and cloud computing. He first joined ITPro as a staff writer in April 2018 and eventually became its Features Editor. Although a regular contributor to other tech sites in the past, these days you will find Keumars on LiveScience, where he runs its Technology section.
-
 Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expect
Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expectNews The Claude Mythos developer is aiming for a more limited approach to cyber tooling for public consumption
-
 Researchers warn millions of RDP and VNC servers are wide open to exploitation
Researchers warn millions of RDP and VNC servers are wide open to exploitationNews Researchers at Forescout spotted millions of RDP and VNC servers exposed online
-
 Brace yourselves for a vulnerability explosion, Forescout warns
Brace yourselves for a vulnerability explosion, Forescout warnsNews AI advances are helping identify software flaws at record pace and scale, but that's not the good news some would think
-
 Ubuntu vulnerability exposes enterprises to root escalation, complete system compromise
Ubuntu vulnerability exposes enterprises to root escalation, complete system compromiseNews The high-severity Ubuntu vulnerability allows an unprivileged local attacker to escalate privileges through the interaction of two standard system components
-
 Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerability
Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerabilityNews Threat actors have been exploiting the vulnerability to achieve root access since 2023
-
 Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourself
Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourselfNews The VS Code vulnerabilities highlight broader IDE security risks, said OX Security
-
 CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaught
CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaughtNews While the CVE figures might be daunting, they won't all be relevant to your organization
-
 Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to know
Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to knowNews Patch Tuesday update targets large number of vulnerabilities already being used by attackers