Cybercriminals exploiting 'the human' to steal data
A new McAfee report shows criminals are increasingly targeting the human, rather than the technology, to steal personal data.
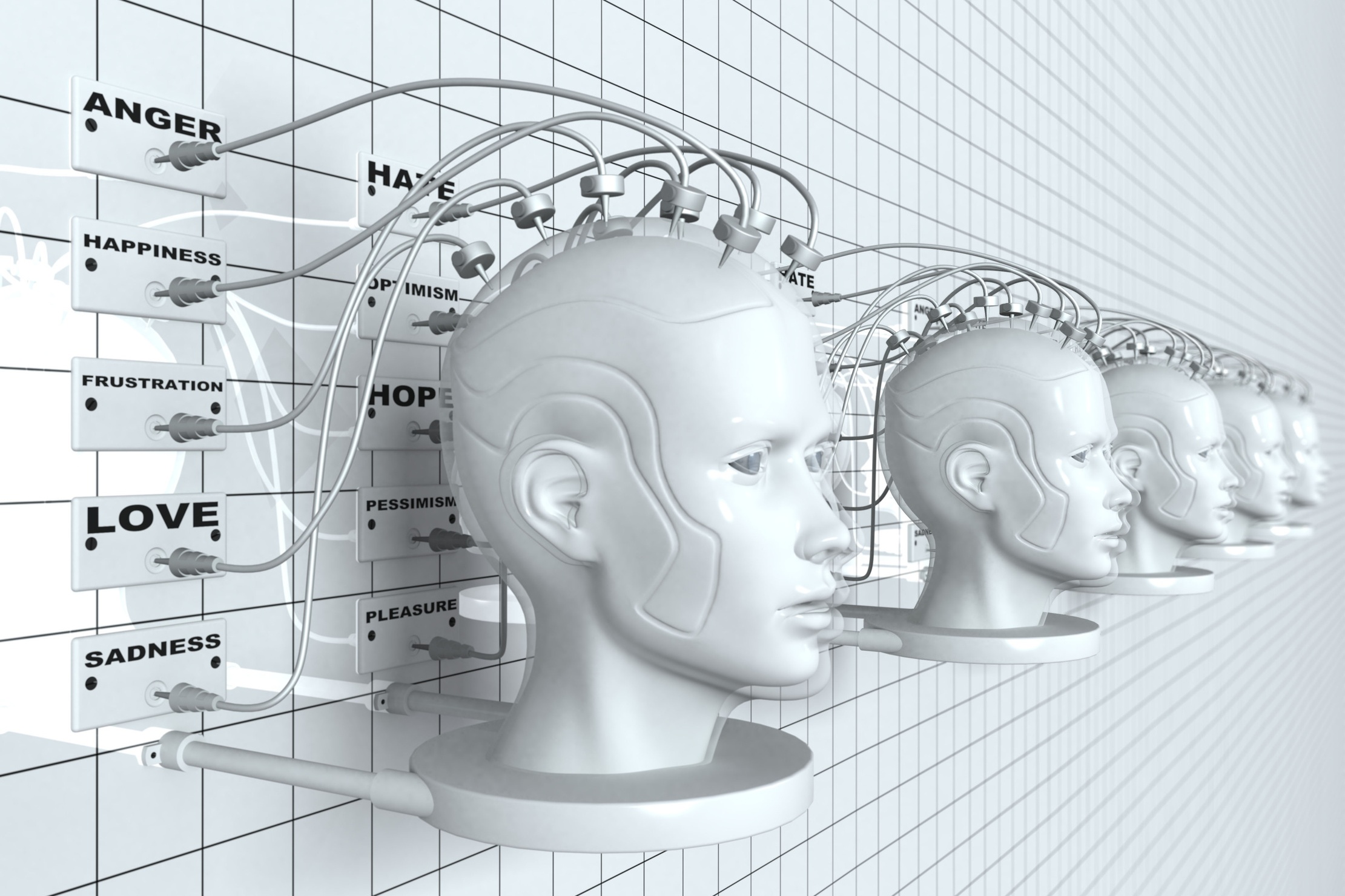
Criminals are increasingly using social engineering to collect personal data from social networking websites, data breaches and other sources according to McAfee.
Its recently released McAfee Security Journal threat report revealed that international experts and McAfee's Avert Labs saw the growing use of social engineering techniques, exploiting human mistakes and weakness rather than having to beat technology.
The Security Journal outlined four major global trends: that the depth of personalised attacks from social networking data would increase, socially-engineered spam would explode in numbers, stock scams would rise and there would be more malicious software which posed as security applications from trusted vendors.
"Cybercriminals are crafting attacks that are virtually impossible for computer users to identify," said Jeff Green, vice president at McAfee Avert Labs. "Phishing scams, e-mail attacks, Trojan horses, and other attacks are so personalised that even someone with the most watchful eye could fall for a carefully socially engineered trap."
As well as updating security technology, McAfee advised that users practiced safe computing and surfing, and to be wary about "too good to be true" offers that came through emails, IMs or social networking messages.
Green added: "It's an easy way for cybercrooks to make money and for spies to steal sensitive data."
McAfee said that in the last six months, scammers have increasingly targeted emotion and curiosity in attempts to steal information, such as with the Olympics, natural disasters and the US presidential election.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
-
 Two US nationals sentenced for role in prolific fake worker laptop farms
Two US nationals sentenced for role in prolific fake worker laptop farmsNews The Americans were raising money for the North Korean regime by allowing fake IT workers to appear as legitimate US-based employees
-
 Beware of emails threatening a code of conduct review
Beware of emails threatening a code of conduct reviewNews A widespread phishing campaign has targeted tens of thousands of employees
-
 Microsoft and NCSC issue alerts over hacker campaigns targeting WhatsApp, Signal messaging apps
Microsoft and NCSC issue alerts over hacker campaigns targeting WhatsApp, Signal messaging appsNews Microsoft warns about a sophisticated attack that starts with WhatsApp messages, while the NCSC says such incidents are on the rise
-
 Is your new hire an AI clone? Microsoft says North Korean hackers are using AI to impersonate job seekers and steal company secrets
Is your new hire an AI clone? Microsoft says North Korean hackers are using AI to impersonate job seekers and steal company secretsNews The groups are increasingly using face-changing or voice-changing software to make their fake identities more plausible
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 Thousands of Microsoft Teams users are being targeted in a new phishing campaign
Thousands of Microsoft Teams users are being targeted in a new phishing campaignNews Microsoft Teams users should be on the alert, according to researchers at Check Point
-
 Microsoft warns of rising AitM phishing attacks on energy sector
Microsoft warns of rising AitM phishing attacks on energy sectorNews The campaign abused SharePoint file sharing services to deliver phishing payloads and altered inbox rules to maintain persistence
-
 Warning issued as surge in OAuth device code phishing leads to M365 account takeovers
Warning issued as surge in OAuth device code phishing leads to M365 account takeoversNews Successful attacks enable full M365 account access, opening the door to data theft, lateral movement, and persistent compromise

