Sophos Endpoint Security and Data Protection 9.7 review
Sophos' latest Endpoint Security and Data Protection suite provides a wealth of features for protecting workstation and mobile data. It looks very good value, but managing it all may not be so simple. Dave Mitchell finds out if Sophos has gone a step too far.
The main ESDP software provides an impressive range of data security measures for the price and includes some useful controls for screening applications, data and devices which worked well during testing. If you stick with these alone then management will be fairly easy, even for larger businesses, but adding in the poorly-integrated NAC and SafeGuard components will almost certainly require dedicated support staff to handle them.

Sophos Endpoint Security and Data Protection 9.7
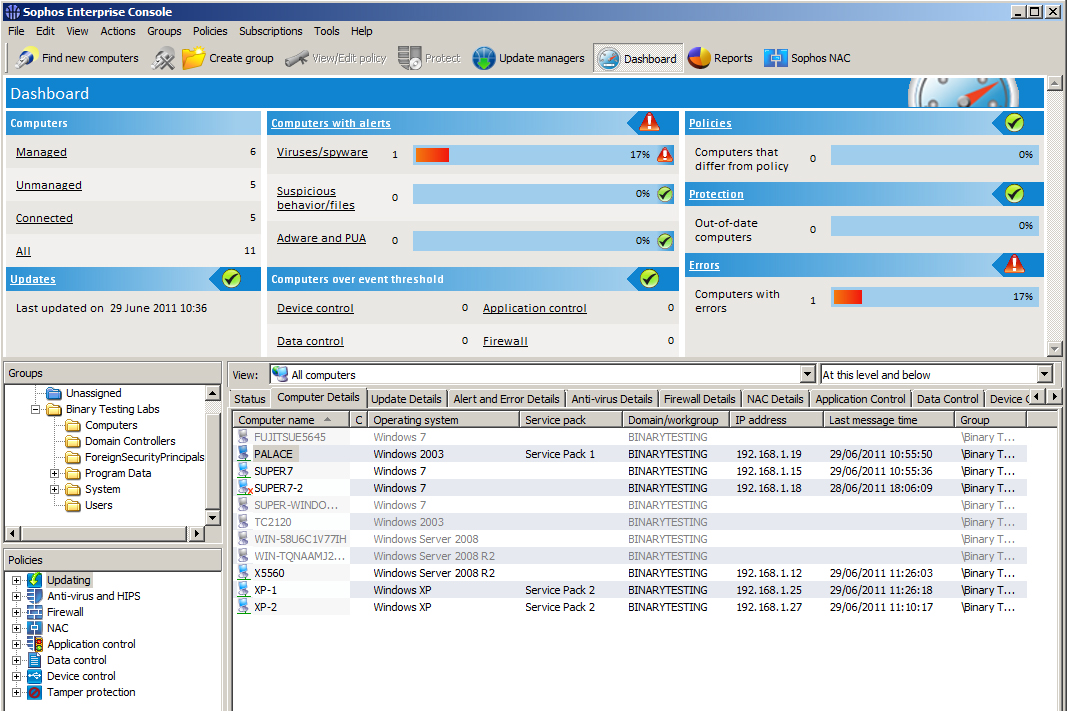
The Enterprise Console provides good access to the main ESDP components and is very quick to post alerts and warnings when vi
A wizard helps to add computers to the console and we had no problems importing our Active Directory Computers container.
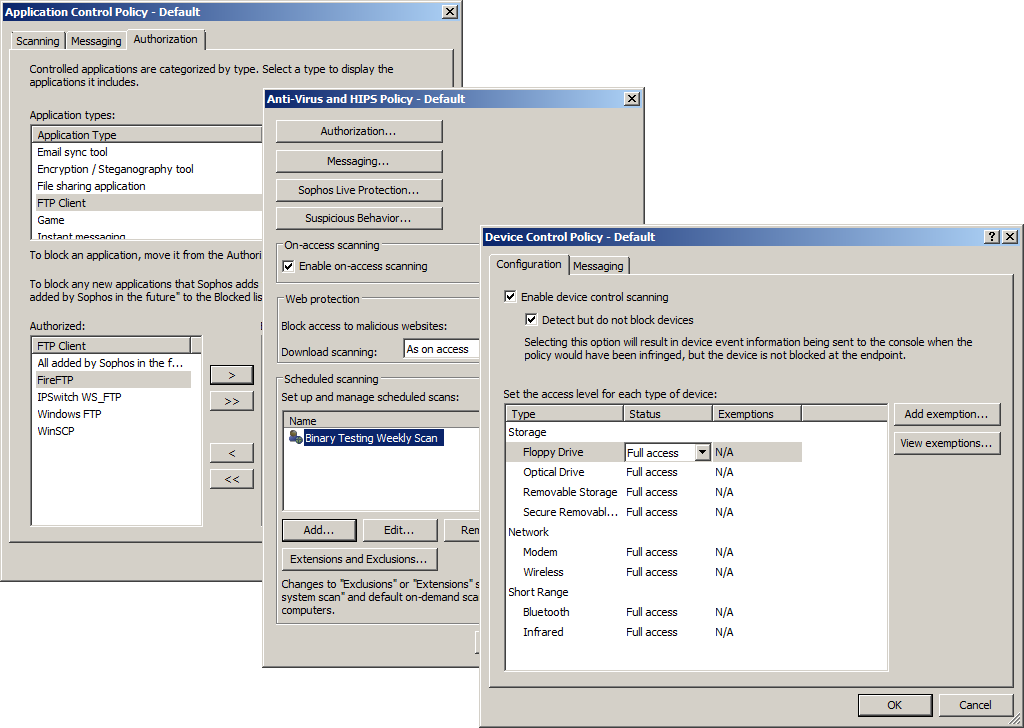
Policies are used for each ESDP component and allow you to control the anti-virus scanner, application usage and access to re
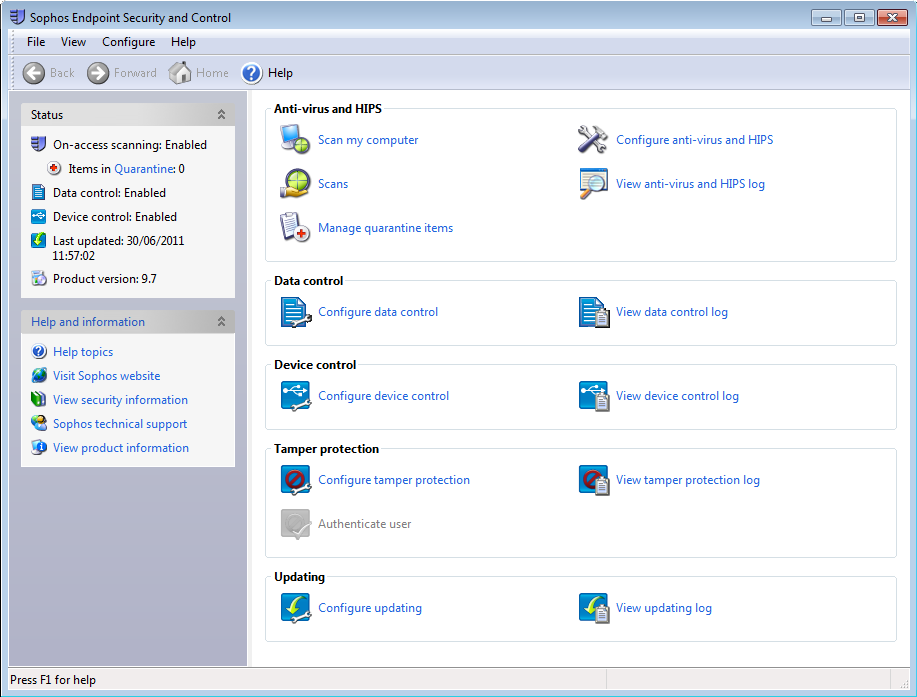
End users can use the local ESDP utility to run their own anti-virus scans, but will require local admin rights to configure
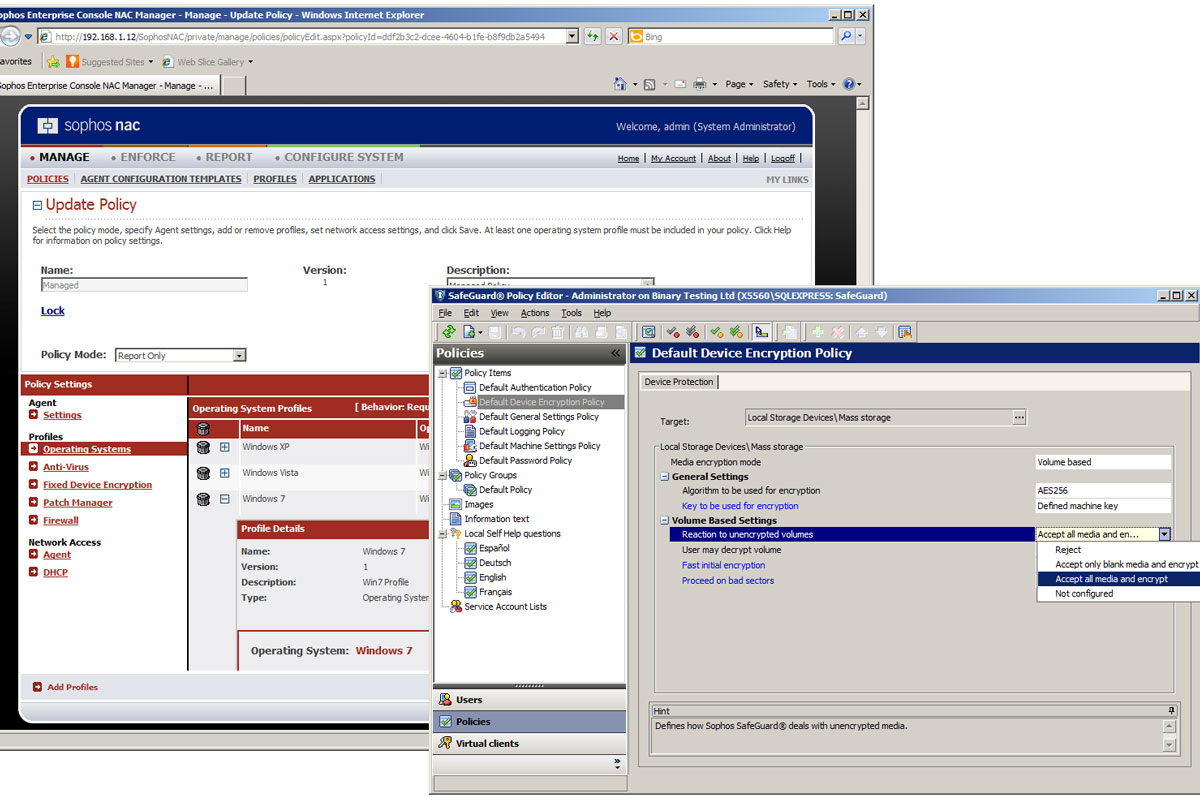
The NAC and SafeGuard components steepen the learning curve as they each have their own policy management consoles.
Best known for its anti-virus software, Sophos also wants to provide full protection for your workstations and its latest Endpoint Security and Data Protection (ESDP) 9.7 software has a veritable feast of security measures. Naturally, its anti-virus software is at the top of the list, but ESDP partners this with firewall, intrusion prevention plus controls for removable devices, data and applications and tops them off with NAC (network access control) and disk encryption.
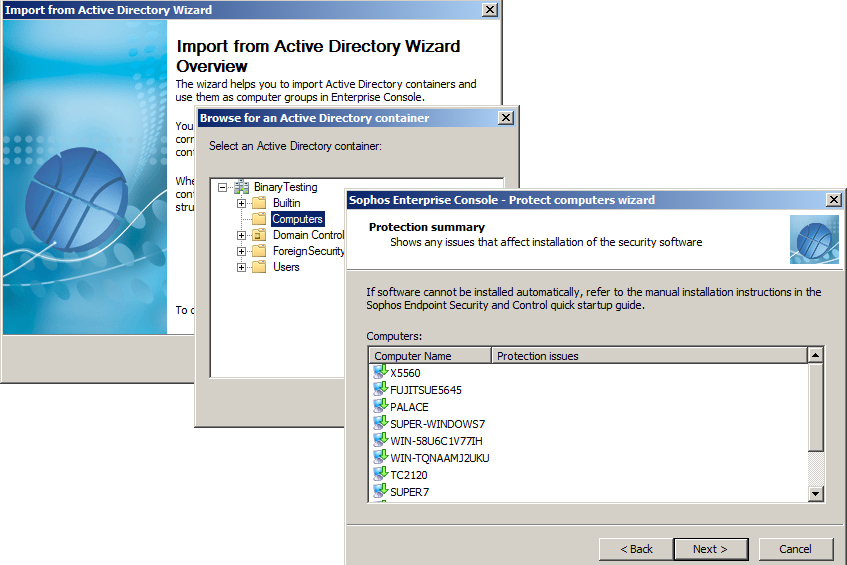
Sophos provides an import wizard that works directly with Active Directory
We found installation initially straightforward as you load the Enterprise Console on a designated management system and then introduce your client systems to it. Sophos provides an import wizard that works directly with Active Directory and we had no problems selecting the AD Computers container and adding all our Windows XP, 7, Server 2003 and Server 2008 R2 systems to the console.
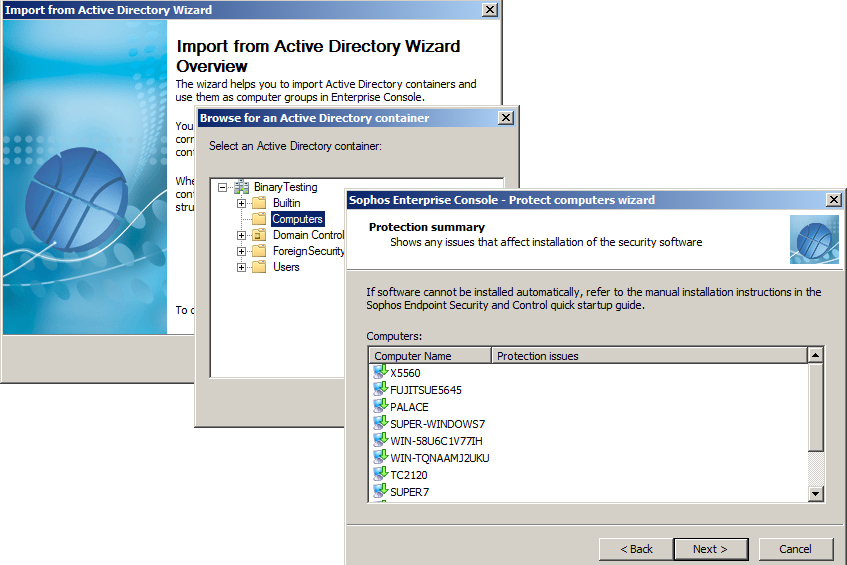
A wizard helps to add computers to the console and we had no problems importing our Active Directory Computers container.
To deploy the agent you select all required systems from the lower pane in the console and choose the Protect Computer menu option. Before doing this some work was needed on our Windows 7 systems as we had to enable the remote registry service, turn off UAC completely and modify the advanced share settings as instructed in the manual.
You can choose which components to install on clients and we opted to leave Sophos' firewall out of the equation as the lab's gateway security appliance does a good enough job for our LAN-based systems. Once the agent had been installed, each system was added into a new group in the console ready to receive its instructions.
Policies are used to control endpoints and ESDP comes with a complete set of predefined ones. These should cover most eventualities, but you can create custom policies and assign them to selected groups.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
An update policy is enabled by default and defines how often group members receive software updates. Other active policies cover anti-virus, intrusion prevention and the firewall. Policies for application, device and data control and tamper protection are disabled by default.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.
-
 AI might help speed up software development, but 81% of devs now spend more time reviewing code – and it’s creating an ‘invisible work’ trend that’s pushing teams to the limit
AI might help speed up software development, but 81% of devs now spend more time reviewing code – and it’s creating an ‘invisible work’ trend that’s pushing teams to the limitNews While AI is improving productivity and efficiency, many developers are caught up in a vicious cycle of code reviews and bug hunting
By Ross Kelly Published
-
 Equinix expands Fabric Geo Zones in data sovereignty drive
Equinix expands Fabric Geo Zones in data sovereignty driveNews The firm says it can provide the first network-level, sovereignty enforcement layer that operates across interconnected clouds and providers
By Emma Woollacott Published
-
 'This is a practical step that paves the way for a better service for taxpayers': HMRC pens £175m deal with Quantexa in data modernization push
'This is a practical step that paves the way for a better service for taxpayers': HMRC pens £175m deal with Quantexa in data modernization pushNews The UK AI unicorn will work to improve HMRC’s core data infrastructure
By Rory Bathgate Published

