Toyota customers in Asia & Oceania at risk following recent data leak
The incident marks the third data leak in the space of a year for Toyota


Data belonging to Toyota customers in Asia and Oceania may have been “publicly accessible” between October 2016 and May 2023 due to a cloud misconfiguration, the company has revealed.
In an advisory, the car manufacturer revealed exposed data includes names, addresses, phone numbers, email addresses, vehicle identification numbers, and registration details.
Critical data, such as credit card information, was not exposed in the leak, the manufacturer insisted.
Toyota said the leak was caused by a cloud misconfiguration as a result of human error, adding that the flaw has since been remediated.
“Some of the files that TC (Toyota Connected Corporation) manages in the cloud environment for overseas dealers' maintenance and investigation of systems were potentially accessible externally due to a misconfiguration,” the company said in a statement.
“After this matter was discovered, we took steps to block access from outside the company.”
Toyota did not disclose the exact number of customers affected. It also said a preliminary investigation found no evidence any of the exposed data had been accessed or maliciously exploited.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
“We have also investigated whether, with this incident, there was any secondary use or if third-party copies remain on the internet, and no evidence of such has been found. At present, we have not confirmed any secondary damage,” it said.
Recurring Toyota data leaks
This latest disclosure follows an investigation into a similar data leak in early May in which data belonging to more than 2.15 million customers in Japan was left accessible for nearly a decade.
At the time, Toyota said a worker at the firm was believed to have set a cloud system’s access level to ‘public’ instead of ‘private’, meaning that data pertaining to vehicle locations and identification numbers was exposed.
RELATED RESOURCE
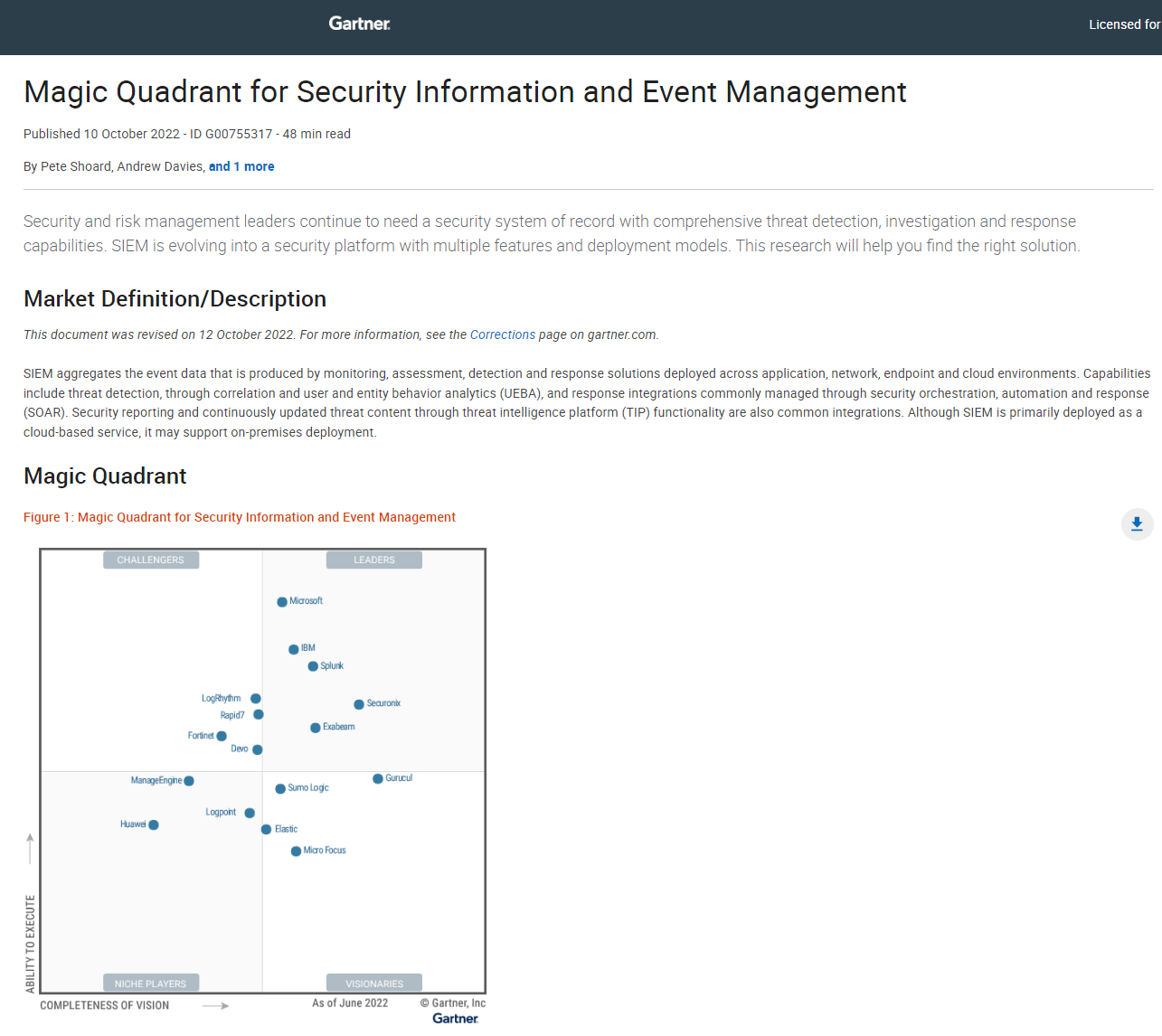
Magic quadrant for Security Information and Event Management (SIEM)
Assessing the current solutions in the market for threat detection, investigation, and response capabilities
This incident sparked a probe at the car manufacturer to improve monitoring of its internal systems and bolster employee data protection practices. Toyota said it has since introduced new rules and processes to monitor cloud configurations across its global operations.
“As we believe that this incident also was caused by insufficient dissemination and enforcement of data handling rules, since our last announcement, we have implemented a system to monitor cloud configuration,” the company revealed.
“Currently, the system is in operation to check the settings of all cloud environments and to monitor the settings on an ongoing basis. In addition, we will work closely again with TC to explain and thoroughly enforce the rules for data handling.”
This is also the third data breach of its kind in the space of a year for Toyota. In October 2022, the manufacturer revealed that data belonging to nearly 300,000 customers was exposed online.
An access key was found to have been left publicly available on GitHub for nearly five years. This particular incident affected Toyota’s T-Connect service and allowed access to a server containing customer email addresses.
The incident prompted Toyota to warn customers that they could face an onslaught of phishing threats in the wake of the leak.

Ross Kelly is ITPro's News & Analysis Editor, responsible for leading the brand's news output and in-depth reporting on the latest stories from across the business technology landscape. Ross was previously a Staff Writer, during which time he developed a keen interest in cyber security, business leadership, and emerging technologies.
He graduated from Edinburgh Napier University in 2016 with a BA (Hons) in Journalism, and joined ITPro in 2022 after four years working in technology conference research.
For news pitches, you can contact Ross at ross.kelly@futurenet.com, or on Twitter and LinkedIn.


