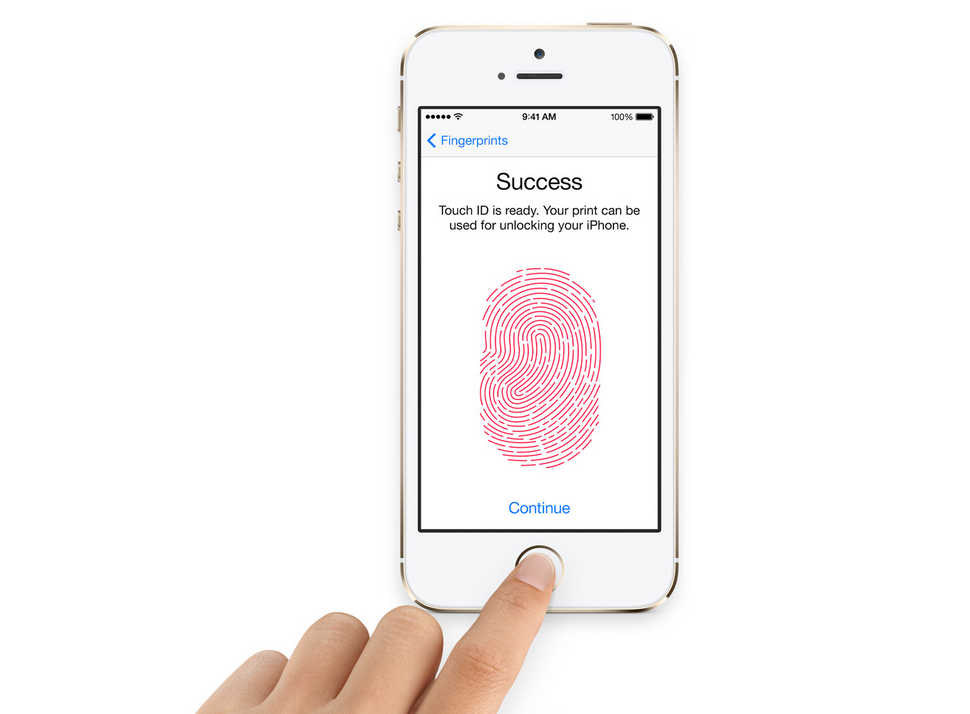
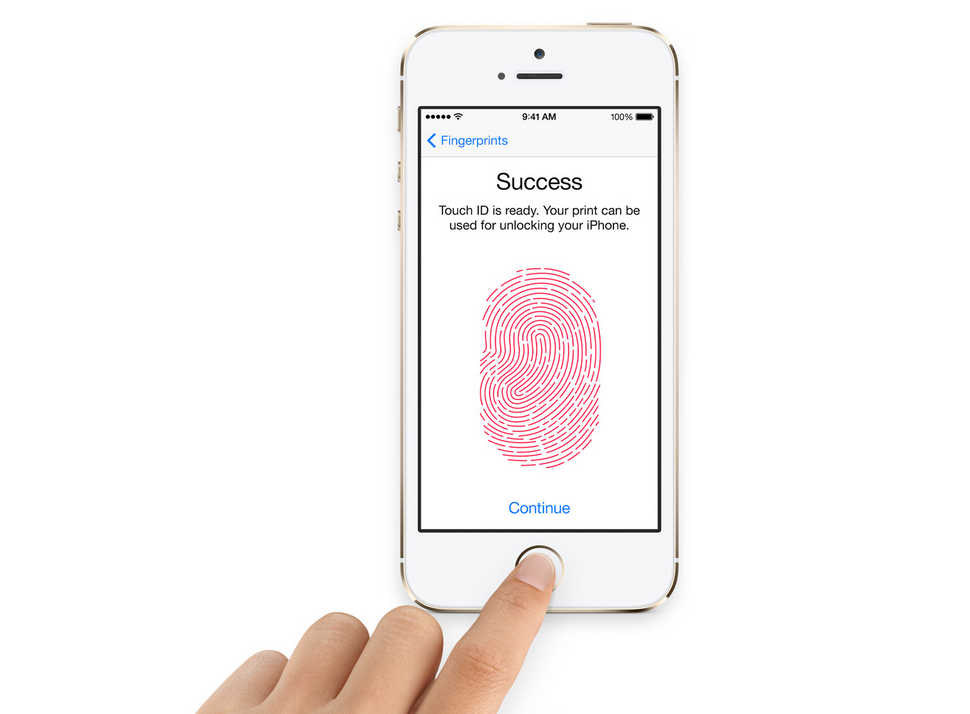
Apple reveals inner workings of iPhone 5s Touch ID scanner
The consumer electronics giant explains how Touch ID keeps users' fingerprints safe.


Apple has published a white paper that reveals exactly how the Touch ID biometric scanner works on its latest iPhones.
The company has shared information regarding how Touch ID keeps biometric data private in an updated security document. It posted the PDF to its iPhones in Business microsite.
The feature works by using what Apple calls a "Secure Enclave". This generates and communicates encrypted temporary information to the rest of the phone, ensuring that fingerprint data is left unexposed to the rest of the system.
Secure Enclave only stores data from scanned prints and not the actual images. With the secure boot process, the Enclave, a co-processor inside Apple's A7 chip, verifies and signs data independently of other iOS software and hardware. Apple said even if a device is compromised the data held in the Secure Enclave is completely inaccessible.
"Each Secure Enclave is provisioned during fabrication with its own UID (Unique ID) that is not accessible to other parts of the system and is not known to Apple. When the device starts up, an ephemeral key is created, tangled with its UID, and used to encrypt the Secure Enclave's portion of the device's memory space," the document said.
"Additionally, data that is saved to the file system by the Secure Enclave is encrypted with a key tangled with the UID and an anti-replay counter."
And while the A7 processor deals with data from Touch ID, this information is encrypted by the scanner, making it unreadable to the rest of the phone. Only Secure Enclave can authenticate the data.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
"It's encrypted and authenticated with a session key that is negotiated using the device's shared key that is built into the Touch ID sensor and the Secure Enclave," the document reads. "The session key exchange uses AES key wrapping with both sides providing a random key that establishes the session key and uses AES-CCM transport encryption."
Researchers at FireEye recently published a post about how keyboard presses, physical button presses, and TouchID interaction can be tracked on iOS devices, even if they are not jailbroken, with a simple monitoring app. The researchers said this information could be used to mount an attack on such a device and get access to the devices's input data.
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
 HSBC to replace passwords with biometric banking
HSBC to replace passwords with biometric bankingNews Voice ID and fingerprints will make log-in processes easier
-
 Apple Touch ID to work with RBS & Natwest mobile apps
Apple Touch ID to work with RBS & Natwest mobile appsNews Banks claim to be first in UK to offer biometric security to customers
-
 iOS 8.1 available to download now: What's new?
iOS 8.1 available to download now: What's new?News iOS 8.1 is finally available to download for free. Here we run through what the latest version of the mobile OS has to offer
-
 Windows 8.1, Voice transcription and Touch ID: IT Pro's web comment roundup
Windows 8.1, Voice transcription and Touch ID: IT Pro's web comment roundupIn-depth Readers not thrilled by Windows 8.1 and security of Touch ID continues to be debated.
-
 How secure is Apple's Touch ID?
How secure is Apple's Touch ID?In-depth We pit the fingerprint scanner against the default 4-digit passcode.


