'Systemic ID problems for 10 million Australians’ after Optus breach, warns minister
The telco giant's response to its 22 September breach has brought on harsh criticism, and the company has now handed over its breach investigation to Deloitte

Australian telecoms giant Optus has been subjected to heavy criticism by the Australian government for its handling of a data breach that saw 10 million accounts affected.
Optus, a subsidiary of Singapore-based telco giant Singtel, is itself Australia’s second-largest telco. On 22 September, the firm reported that the data of 10 million accounts had been affected by a data breach, but that mobile network and broadband services were unaffected.
RELATED RESOURCE

CIO Priorities: 2020 vs 2023
Zero Trust, SaaS Security, and its impact on SD-WAN being a priority
It subsequently warned 10,200 customers that their Medicare records were included in a cache that a hacker was attempting to hold to ransom online. On Sunday, however, officials within the Australian government warned that the company was still falling short of its obligations to customers in the wake of the breach.
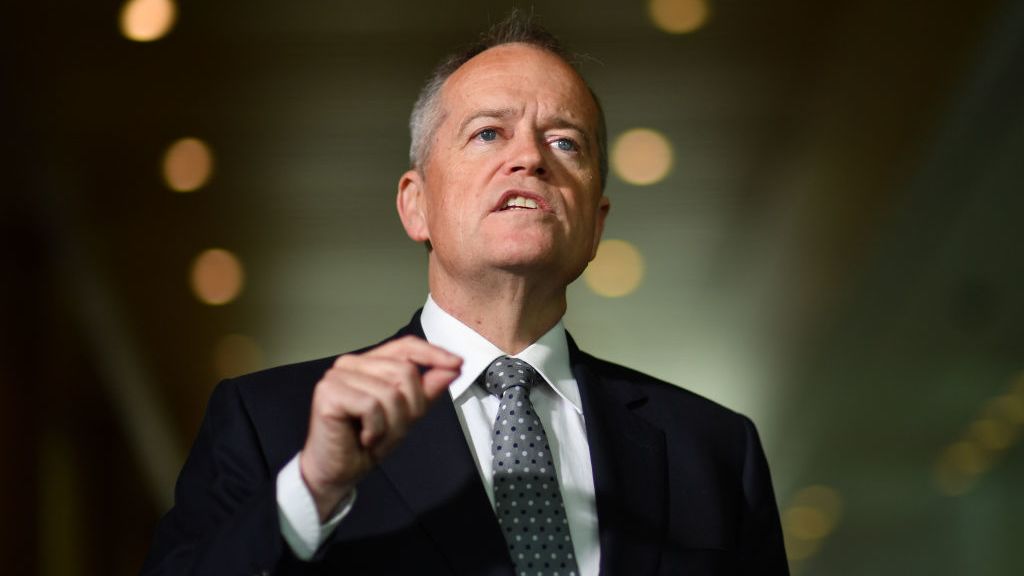
"We call upon Optus to understand that this breach has introduced systemic problems for 10 million Australians in terms of their personal identification," stated government services minister Bill Shorten at a press conference.
"We know that Optus is trying to do what it can, but having said that, it's not enough," Shorten said. "It's now a matter of protecting Australians' privacy from criminals."
Shorten also stated that the firm had been too slow to provide the government with insight into which customers had their Medicare and social service information stolen. As long as five days after the breach, no such information had been received.
The company has since identified that 2.1 million customers had had ID exposed in the breach, including Medicare card information. The Guardian reported that Optus has now commissioned Deloitte to carry out an independent review of the breach.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
In the days following the attack, Australian prime minister Anthony Albanese stated that he would look to change privacy rules in the country, with the aim of better protecting citizens’ financial information in the event of a similar breach in the future.
As is required in the UK and EU, Australian companies have to report a data breach within 72 hours of discovering a breach has occurred, with any delays requiring adequate justification. This is a result of the Notifiable Data Breach (NDB) scheme, an amendment to the Privacy Act 1988, and failure to comply can result in a fine.
“This review will help ensure we understand how it occurred and how we can prevent it from occurring again. It will help inform the response to the incident for Optus,” Optus CEO Bayer Rosmarin in a statement, speaking on the ongoing Deloitte review.
“This may also help others in the private and public sector where sensitive data is held and risk of cyber-attack exists. I am committed to rebuilding trust with our customers and this important process will assist those efforts.”
Uber launches infosec hiring spree after attributing breach to LAPSUS$ American Airlines hit by data breach General Data Protection Regulation (GDPR)
The precise manner through which the attack was carried out, or by whom, is still unknown. Although data had originally been posted online with a ransom demand in the wake of the attack, this was later pulled from the hacker forum on which it had been listed.
Early reports suggested that the attacker's IP address suggested a European origin, but this remains unconfirmed and hackers can hide IP addresses with relative ease.
"We should not be in the position that we're in, but Optus has put us here," stated Home Affairs Minister Clare O'Neil.
"It's really important now that Australians take as many precautions as they can to protect themselves against financial crime."
Data breaches can seriously affect a company’s reputation, leading to decreased trust from its customers going forward, and handling a breach properly can be key to company image as well as avoiding legal trouble. In July, Uber’s former chief security officer was made to face wire fraud charges over his alleged involvement in the attempted coverup of its 2016 hack, which saw the details of 57 million drivers and users exposed.

Rory Bathgate is Features and Multimedia Editor at ITPro, overseeing all in-depth content and case studies. He can also be found co-hosting the ITPro Podcast with Jane McCallion, swapping a keyboard for a microphone to discuss the latest learnings with thought leaders from across the tech sector.
In his free time, Rory enjoys photography, video editing, and good science fiction. After graduating from the University of Kent with a BA in English and American Literature, Rory undertook an MA in Eighteenth-Century Studies at King’s College London. He joined ITPro in 2022 as a graduate, following four years in student journalism. You can contact Rory at rory.bathgate@futurenet.com or on LinkedIn.
-
 Latitude Financial's data policies questioned after more than 14 million records stolen
Latitude Financial's data policies questioned after more than 14 million records stolenNews Some of the data is from at least 2005 and includes customers’ name, address, and date of birth
-
 Latitude hack now under state investigation as customers struggle to protect their accounts
Latitude hack now under state investigation as customers struggle to protect their accountsNews The cyber attack has affected around 330,000 customers, although the company has said this is likely to increase
-
 IDCARE: Meet the cyber security charity shaping Australia and New Zealand's data breach response
IDCARE: Meet the cyber security charity shaping Australia and New Zealand's data breach responseCase Studies IDCARE is recruiting a reserve army to turbocharge the fightback against cyber crime not just in the region, but in the interests of victims all over the world
-
 Australia commits to establishing second national cyber security agency
Australia commits to establishing second national cyber security agencyNews The country is still aiming to be the most cyber-secure country in the world by 2030
-
 Medibank bleeds $26 million in cyber costs following hack
Medibank bleeds $26 million in cyber costs following hackNews The company believes this figure could rise to $45 million for the 2023 financial year
-
 TikTok's two new European data centres to address data protection concerns
TikTok's two new European data centres to address data protection concernsNews The company is under pressure to prove its user data isn’t being accessed by the Chinese state
-
 Cyber attack on Australia’s TPG Telecom affects 15,000 customers
Cyber attack on Australia’s TPG Telecom affects 15,000 customersNews It is the third cyber attack on a major Australian telco since October
-
 Telstra blames IT blunder for leak of 130,000 customer records
Telstra blames IT blunder for leak of 130,000 customer recordsNews Australia’s biggest telco said that the error was due to a mismanagement of databases and not a cyber attack


