Royal Mail ransom note leaked, LockBit’s role remains uncertain
The prolific ransomware operation has denied involvement but researchers remain sceptical


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
After having been linked with the “cyber incident” affecting the UK’s Royal Mail Group, the LockBit ransomware operation has denied its members were behind the assumed attack.
Ransom notes began printing at Royal Mail’s sorting office in Mallusk, Northern Ireland, on Thursday evening revealing threats of data leakage if a ransom wasn’t paid, the Belfast Telegraph reported.
Images of the ransom note, which claimed to be authored by the operators of LockBit Black - the gang’s third version of the ransomware (also known as LockBit 3.0) that shares code with Black Matter’s payload - were shared widely throughout the evening.
The note claimed Royal Mail’s data were “stolen and encrypted”, and that it would be published on its deep web-based leak site if the ransom was not paid.
Also included were two URLs that led to online portals through which the hackers could be contacted, and a decryption ID to enter once one of the contact sites were accessed.
The URLs are thought to be the same as those found on the ransom note received by the André Mignot hospital in Versailles last month.
The attack forced patients to be moved and was later attributed to LockBit Black ransomware, however, the decryption IDs were not issued by LockBit itself in this case.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Per a report from Bleeping Computer, which contacted LockBit, the ransomware gang has denied involvement in the attack on the British multinational postal company.
RELATED RESOURCE
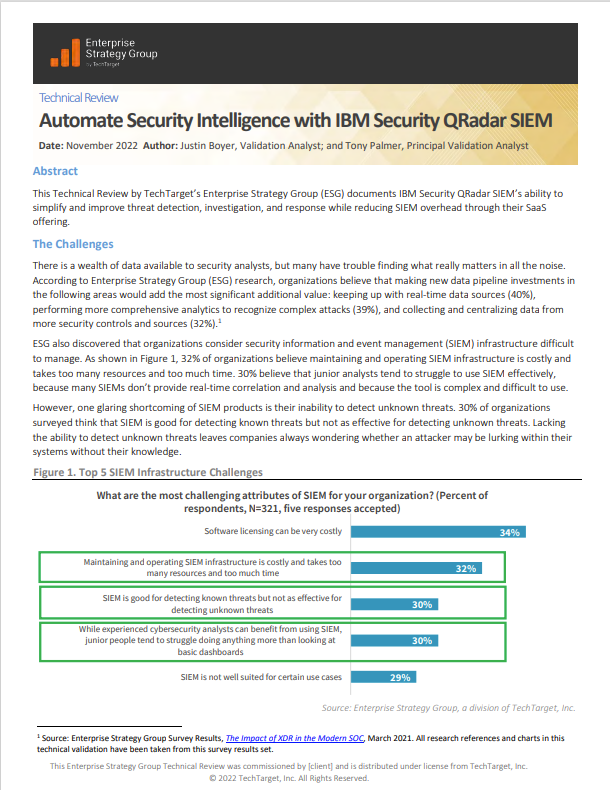
Automate security intelligence with IBM Security QRadar SIEM
Simplify and improve threat detection, investigation and response with reducing overheads
Security researchers have raised questions over the legitimacy of LockBit’s denial.
The builder for LockBit Black was leaked in September by a group which claimed to have hacked LockBit’s servers.
This means that hackers, in theory, don’t need to be official ‘affiliates’ of LockBit’s ransomware as a service (RaaS) programme in order to launch attacks using its software.
However, the contact URLs supplied in the note directed to LockBit’s website and the decryption ID initially worked, but after the ransom note was leaked, researchers have reportedly said the ID is no longer valid.
If the decryption ID did work at some point in time, as one expert confirmed, it could either mean LockBit actually did conduct the attack, or an unaffiliated attacker launched the ransomware while also having privileged access to LockBit’s official website so they could create a negotiation chat portal for Royal Mail.
Asked for confirmation of the leak’s legitimacy, the UK’s National Cyber Security Centre (NCSC) and Royal Mail both told IT Pro that they would not be disclosing any details at the time of writing.
The National Crime Agency (NCA), also involved in the ongoing investigations, did not respond to requests for comment.
What is the “cyber incident” at Royal Mail?
Royal Mail confirmed on Wednesday evening that it was suffering the effects of a “cyber incident” which continues to ‘severely disrupt’ the international shipping branch of its business.
“We are temporarily unable to despatch items to overseas destinations,” read its incident update page. “We strongly recommend that you temporarily hold any export mail items while we work to resolve the issue. Items that have already been despatched may be subject to delays. We would like to sincerely apologise to impacted customers for any disruption this incident is causing.”
Very few details of the incident have been revealed other than that the NCSC and NCA are involved in the investigation, and the Information Commissioner’s Office (ICO) has also been informed.
Royal Mail has never described the incident as an ‘attack’ and all parties involved have yet to confirm that the incident is ransomware in nature.
“We are aware of an incident affecting Royal Mail Group Ltd and are working with the company, alongside the National Crime Agency, to fully understand the impact,” the NCSC said in a brief official statement.
As of Friday, Royal Mail’s overseas shipping processes remain severely disrupted.
IT Pro will continue to report on the story as it develops.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwise
The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwiseNews Billing itself as the “only place ransomware allowed", RAMP catered mainly for Russian-speaking cyber criminals