Business email compromise attacks are evolving, but what can be done about it?
As business email compromise attacks have become more sophisticated, organizations have been forced to adapt tactics in defense

Business email compromise (BEC) attacks have been a common attack vector for almost as long as the technology has been around, and experts continue to rank it as one of the biggest threats facing businesses today.
BEC attacks account for the lion’s share of cyber attacks, according to research from Arctic Wolf Labs, which found email-based attacks outnumber ransomware by a factor of 10. Software company Tripwire’s annual report on BEC activity also found email-based attacks constituted 99% of all reported threats, with the FBI’s cyber unit estimating BEC attacks accounted for $2.7 billion in adjusted losses annually.
Businesses lost a total of $51 billion to BEC attacks over the last decade, per Cloudflare research published in 2023, eclipsing the ill-gotten winnings of ransomware groups.
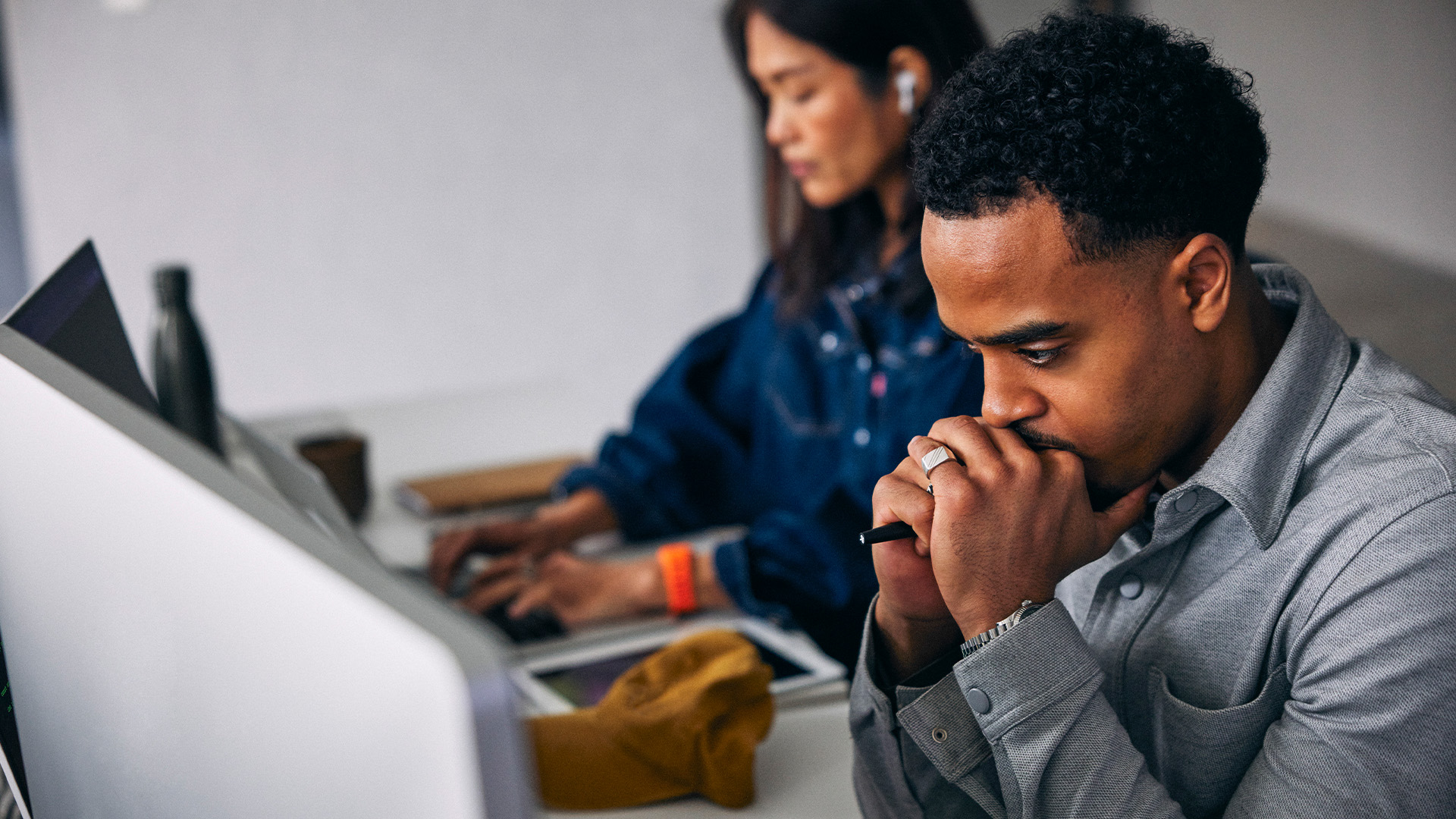
Speaking to ITPro at CPX 2024, Gil Friedrich, VP of Email Security at Check Point says targeting users via email is a popular attack vector for threat actors as it requires relatively few resources compared to other methods of entry.
“Every business is a little different but I think what is common to all businesses is that very often this [email] is where the hackers would start,” Friedrich explains. “This has to do with the fact that email is very unique, in that it’s open to everyone … you can reach anyone in the organization so it makes it very tempting to use”.
Business email compromise attacks are evolving
With the transition toward cloud-based IT infrastructure, new opportunities have arisen for attackers to escalate their attacks once they have compromised an account, which is now connected to more components across the network.
Speaking at a security roundtable at CPX 2024, Christophe Leirens, senior manager of Toyota Europe’s cyber security team describes the scale of the threat BEC attacks now pose to his organization.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
“Email is still the number one attack vector – on a monthly basis there are about 30 million malicious emails that we have to block,” Leirens states, adding that safeguarding its email system has been a top priority for the company.
The sheer scale of BEC attacks in recent years has also prompted somewhat of an evolution as well. Friedrich broke down what he characterizes as the three generations of BEC attacks that have followed the cloud explosion of the 2010s.
First up is BEC-1 attacks which were essentially traditional phishing attacks that sought to gain access to a corporate network via an individual email account, impersonating a colleague or another organization, for example.
“When it started, email security was pretty open, you could send emails to anyone, impersonating an organization or CEO. The checks were very weak and so there was the temptation with the move to the cloud to take over your account and then leverage that in different ways of monetization.”
RELATED WHITEPAPER

As default security solutions became more robust these attacks stopped working, Friedrich says, prompting attackers to move onto BEC-2 attacks. These see attackers compromise a partner organization to launch further attacks.
“Now they are sending an email that comes from a legitimate source on an existing thread. So they’ve replied to an email you sent, but it’s malicious because they broke into the other account.”
The third and most recent generation of BEC attacks involves attackers leveraging legitimate services that use email such as Zoom or QuickBooks to deliver malicious files. “You can set up a meeting and the recipient will get an email but at the top in the notes it might say ‘please read this before the meeting starts, and there’s a [malicious] link”, Friedrich outlines.
AI can combat business email compromise attack
The strength of this latest generation of BEC attacks is that there’s nothing about the language in the email that would indicate it was malicious, and this is where Friedrich thinks AI can play a significant role in keeping an organization’s email systems secure.
Friedrich explained that previous forms of static, signature-based threat detection flag prevalent threats like links to crypto wallets, which are malicious 98% of the time in a business context, but these systems struggle when attackers impersonate legitimate services employees frequently use.
“A link to Google Drive is 3% likely to be malicious. So when you think about the static layer you could say it's useless because it's mostly legitimate, there’s nothing I can do.”
Friedrich tells ITPro that AI security tools can combine this probability with other threat indicators to detect threats that static layers might view as statistically insignificant.
“But in the context of AI, 3% is actually a lot because you allow the AI to correlate that with the first-time sender and the language of the email and a ton of other indicators we are looking at”.

Solomon Klappholz is a former staff writer for ITPro and ChannelPro. He has experience writing about the technologies that facilitate industrial manufacturing, which led to him developing a particular interest in cybersecurity, IT regulation, industrial infrastructure applications, and machine learning.
-
 HMRC pens £175m deal with Quantexa in data modernization push
HMRC pens £175m deal with Quantexa in data modernization pushNews The UK AI unicorn will work to improve HMRC’s core data infrastructure
-
 Workers are wasting a full work day each week switching between AI tools
Workers are wasting a full work day each week switching between AI toolsNews Transferring data from one AI tool to another is costing more time than the tools actually save
