Access brokers are making it easier for ransomware operators to attack businesses
A new business model has been uncovered that makes it much easier for attackers to gain access to business' networks


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
Cyber security researchers have uncovered a new underground business model dubbed 'access-as-a-service' in which access to an organisation's network is sold rather than an exploit or zero-day vulnerability.
So-called access brokers are selling direct access to a company's network in which they're already embedded via shared remote VPN connections. Attackers can pay different sums for varying levels of access.
The business model, discovered and detailed by Trend Micro, could lead to a new way for ransomware operators to launch attacks without having working exploit themselves.
Attackers are now able to buy their way into a network, paying only as much as they need for the right level of access to achieve their objective.
The business model relies on stolen credentials for access brokers to have a viable service and Trend Micro said businesses will have to place a greater emphasis on protecting credential theft to avoid future breaches.
"Access brokers in the criminal underground often advertise this service like it’s a cinema ticket: Somebody buys this ticket, and they get straight in," read the report. "In reality, however, things are a bit different.
RELATED RESOURCE

The best defence against ransomware
How ransomware is evolving and how to defend against it
"For example, what exactly do customers get in exchange for their money? Sometimes, it’s access to a web shell or a similar straightforward method of getting a command prompt into the compromised network. More often than not, however, it’s just a set of credentials and a VPN server to connect to."
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Remote Desktop Protocol (RDP) access and VPN-based access were the two most common products being advertised, primarily in the United States, Spain, Germany, France, and the UK.
After viewing more than a thousand adverts for services online, the most common targets Trend Micro observed were universities and schools (36%), 11% offered access to manufacturing firms and professional services, with other miscellaneous companies comprising the remainder.
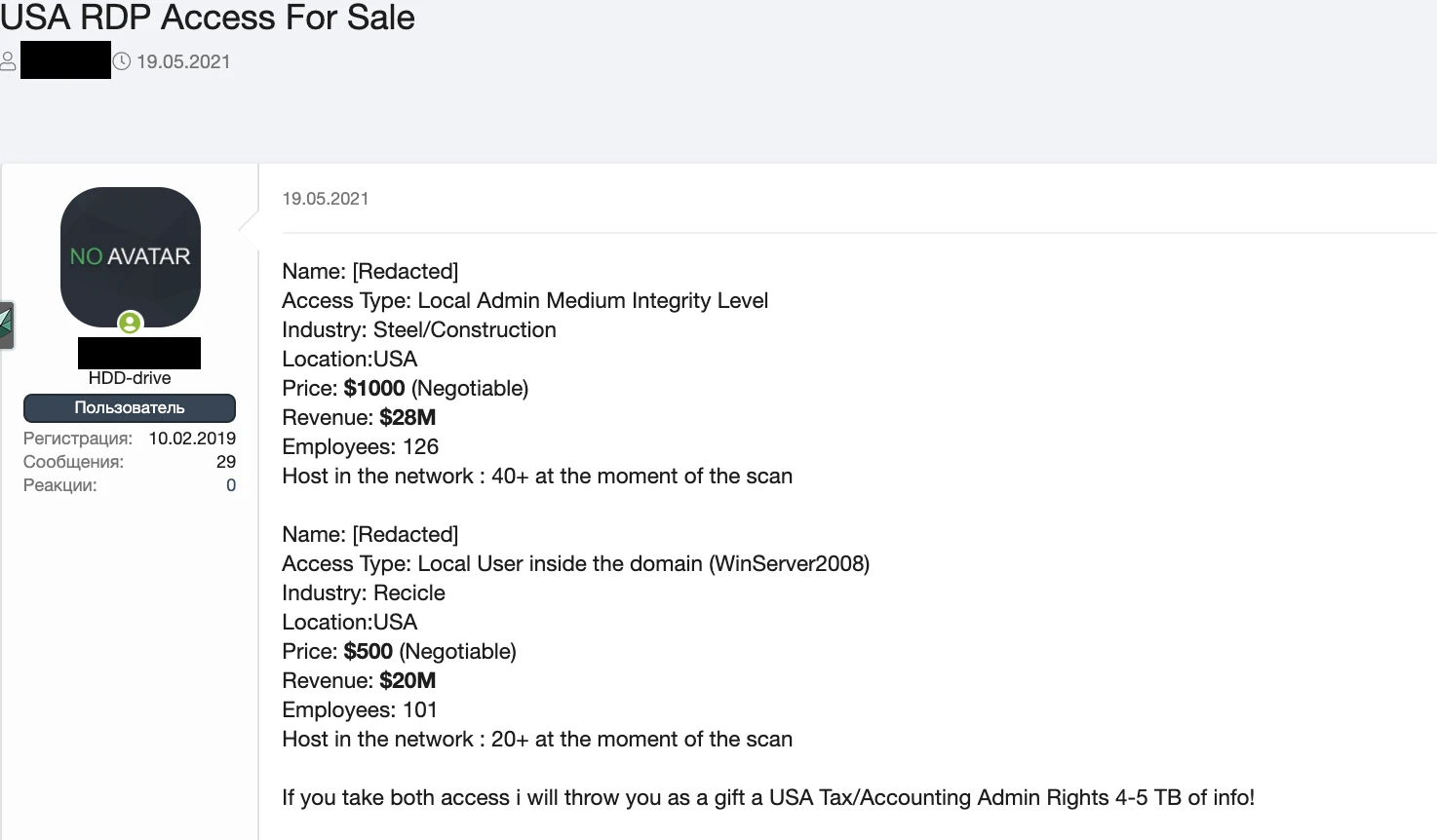
Online adverts typically offer access to a company with a broad description such as 'big German energy company', offer details of the level of access available, type of access on offer (RDP or VPN), cost of the service, and in some cases details of the company's turnover and employee numbers.

Prices for services can range between a few US dollars for access to a single machine and six-digit sums for admin credentials to an entire business, but most dedicated brokers don't advertise their prices openly, according to the researchers.
Access brokers are typically advertising their products either on deep web criminal marketplaces, through a network of connections throughout underground forums, and in less common cases dedicated online shops are used for smaller-scale, single-machine access.
Trend Micro made several suggestions for businesses wary of being exploited using this new business model. Monitoring public breaches can be useful in determining if credentials may have been stolen and triggering a password reset for all staff if one is detected.
Enabling two-factor authentication (2FA) for remote staff will also help prevent remote access from criminals, as will closely monitoring user behaviour on the network.
For the most cautious, operating on a zero-trust model and assuming all staff have lost their passwords to criminals before is recommended, applying the necessary security measures where appropriate.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwise
The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwiseNews Billing itself as the “only place ransomware allowed", RAMP catered mainly for Russian-speaking cyber criminals