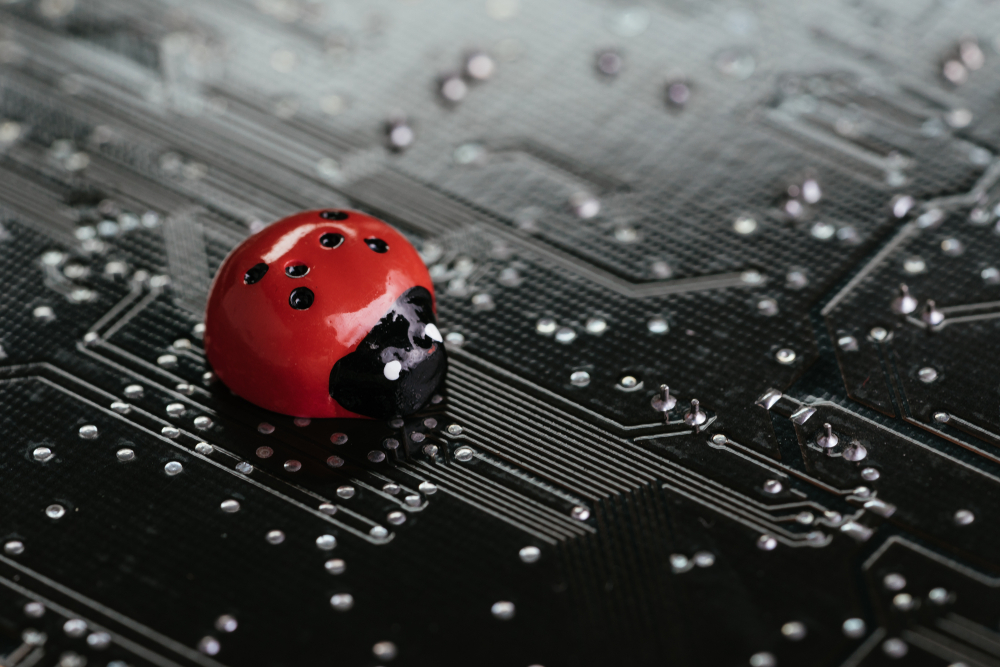
Developer scores $100,000 bounty from Apple for exposing a critical vulnerability
Apple ID bug would allow hackers to take control of a user’s account
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
Apple awarded $100,000 to Bhavuk Jain for identifying a security vulnerability in the "Sign in with Apple" feature found on some websites and third-party applications. Hackers could use the bug to take control of a user's account.
Apple's servers use a JSON Web Token, which can contain the user’s Apple ID email address, to verify a user account during the “Sign in with Apple” process.
Jain discovered he could request a JSON Web Token for a real Apple account, and the signature would be verified each time. With an email address connected to an Apple ID, a hacker could to get a validated token and access the account.
Apple reviewed server logs during the patching process and determined the flaw had not been exploited. Accounts using two-factor authentication are less likely to be vulnerable to this bug.
This type of hacking-for-pay is relatively common today. Apple and other tech companies use bounty programs to encourage white-hat hackers to uncover vulnerabilities in their software.
This allows companies to patch flaws before they are made public for a fraction of the cost of fixing hacks post-mortem. Companies pay the most substantial bounties for exposing serious vulnerabilities.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
David Gargaro has been providing content writing and copy editing services for more than 20 years. He has worked with companies across numerous industries, including (but not limited to) advertising, publishing, marketing, real estate, finance, insurance, law, automotive, construction, human resources, restoration services, and manufacturing. He has also managed a team of freelancers as the managing editor of a small publishing company.
-
 Google Cloud Next 2026: all the live updates as they happen
Google Cloud Next 2026: all the live updates as they happenLive blog ITPro is on the ground at Google Cloud Next 2026, to cover all the latest announcements from the day one keynote
-
 AWS UK chief touts big gains with AI-powered coding
AWS UK chief touts big gains with AI-powered codingNews Developers at AWS were able to speed up delivery of what would have traditionally been an extensive project
-
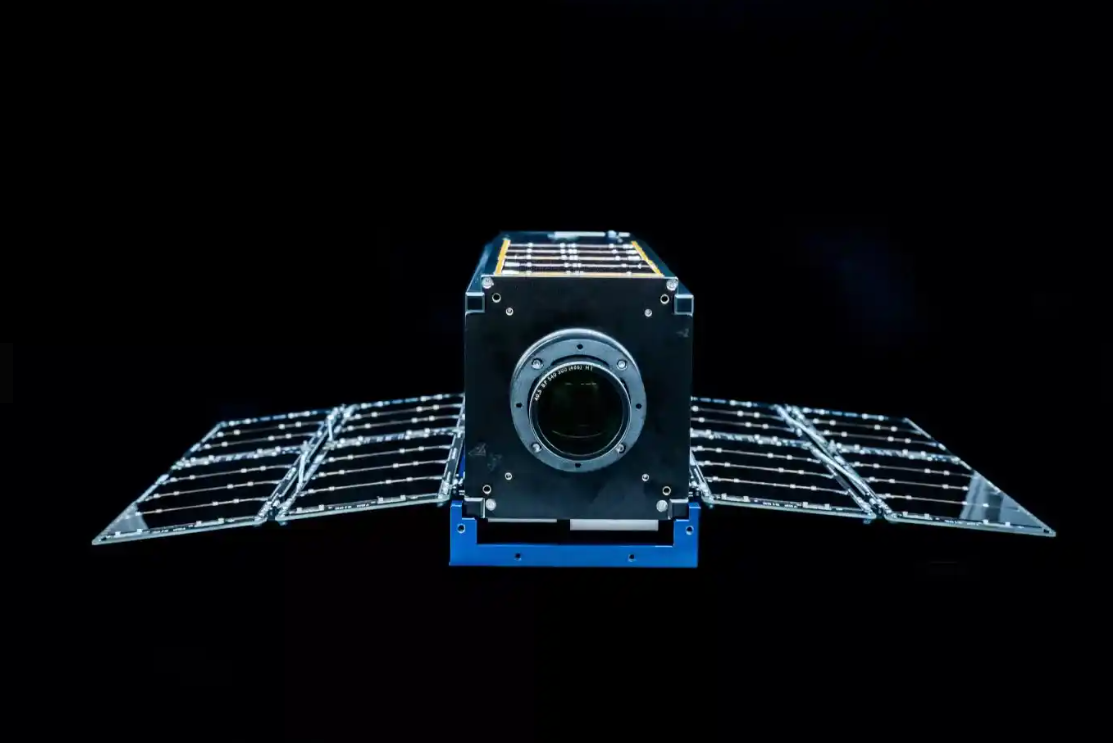 Why the Space Force wants white hats to attack a satellite
Why the Space Force wants white hats to attack a satelliteCase study Authorities hope the first-of-its-kind competition could bring benefits to the cyber sector
-
 OpenAI to pay up to $20k in rewards through new bug bounty program
OpenAI to pay up to $20k in rewards through new bug bounty programNews The move follows a period of unrest over data security concerns
-
 New ‘DarkBit’ ransomware gang shuts down Technion, demands $1.7 million ransom
New ‘DarkBit’ ransomware gang shuts down Technion, demands $1.7 million ransomNews A politically charged ransom note suggests DarkBit are one of the newest hacktivist gangs to emerge in recent months
-
 Research: Luxury cars and emergency services vehicles vulnerable to remote takeover
Research: Luxury cars and emergency services vehicles vulnerable to remote takeoverNews A "global API issue" has been highlighted through months-long research into brands such as Ferrari and Mercedes-Benz, leaving owners open to hacking, account takeovers, and more
-
 Podcast transcript: Meet the cyborg hacker
Podcast transcript: Meet the cyborg hackerIT Pro Podcast Read the full transcript for this episode of the IT Pro Podcast
-
 The IT Pro Podcast: Meet the cyborg hacker
The IT Pro Podcast: Meet the cyborg hackerIT Pro Podcast Resistance is futile - offensive biotech implants are already here
-
 SpaceX bug bounty offers up to $25,000 per Starlink exploit
SpaceX bug bounty offers up to $25,000 per Starlink exploitNews The spacecraft manufacturer has offered white hats immunity to exploit a wide range of Starlink systems, with a dedicated report page
-
 Nomad happy to forgive hackers if they return 90% of $190 million that was stolen
Nomad happy to forgive hackers if they return 90% of $190 million that was stolenNews The crypto bridge is offering 'white hat hackers' a 10% bounty following the attack earlier this week